Overview
Recently, NSFOCUS CERT detected that GitLab officially released a security announcement and fixed multiple security vulnerabilities in GitLab Community Edition (CE) and Enterprise Edition (EE), including two serious vulnerabilities. Affected users should take protective measures as soon as possible.
CVE-2023-7028: In GitLab CE/EE, users can reset their passwords through the auxiliary email address. Due to errors in the email verification process, attackers can send emails that reset account passwords to unverified mailboxes and take over accounts by resetting passwords without user interaction. The CVSS score is 10.
CVE-2023-5356: The attacker can abuse the Slack/Mattermost integration to execute slash commands as other users by checking improper vulnerabilities, with a CVSS score of 9.6.
Reference link: https://about.gitlab.com/releases/2024/01/11/critical-security-release-gitlab-16-7-2-released/
Scope of Impact
Affected version
CVE-2023-7028
- 16.1 <= GitLab CE/EE < 16.1.5
- 16.2 <= GitLab CE/EE < 16.2.8
- 16.3 <= GitLab CE/EE < 16.3.6
- 16.4 <= GitLab CE/EE < 16.4.4
- 16.5 <= GitLab CE/EE < 16.5.6
- 16.6 <= GitLab CE/EE < 16.6.4
- 16.7 <= GitLab CE/EE < 16.7.2
CVE-2023-5356
- 8.13 <= GitLab CE/EE < 16.5.6
- 16.6 <= GitLab CE/EE < 16.6.4
- 16.7 <= GitLab CE/EE < 16.7.2
Unaffected version
- GitLab CE/EE >= 16.5.6
- GitLab CE/EE >= 16.6.4
- GitLab CE/EE >= 16.7.2
Note: Repair procedures for CVE-2023-7028 have been migrated back to 16.1.6, 16.2.9, 16.3.7 and 16.4.5.
Detection
Version detection
Relevant users can determine whether the current application has risks through version detection.
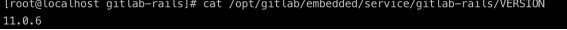
Use the following command to view the currently used GitLab version:
cat /opt/gitlab/embedded/service/gitlab-rails/VERSION
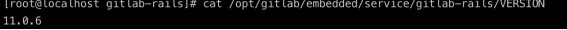
If the current version is affected, there may be a security risk.
Attack screening
Relevant users can check whether there is any exploit attempt of CVE-2023-7028 vulnerability by viewing the application log:
1. Check gitlab-rails/production_json.log to see if there is an HTTP request pointing to the /users/password path, which contains params.value.email and consists of a json array with multiple email addresses.
2. Check gitlab-rails/audit_json.log for entries containing PasswordsController#create and target_details for meta.caller.id, which consist of a json array with multiple e-mail address.
Mitigation
Official upgrade
At present, the above vulnerabilities have been officially fixed in the latest version. Please upgrade the version for protection as soon as possible. The official download link: https://about.gitlab.com/update/
Other protective measures
If the relevant users cannot upgrade for the time being, the following measures can also be taken to temporarily relieve CVE-2023-7028:
Enable Two-Factor Authentication (2FA) for all GitLab accounts, especially users with advanced privileges (e.g. administrator accounts); access to the target application can be restricted without impacting business.
Note: SSO users (such as SAML) are affected, but LDAP users will not be affected because there is no forget/reset password option.
If 2FA has been enabled, the attacker will not be able to take over the account and requires a second authentication factor to log in, but it can still reset its password.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Technologies Group Co., Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.