Recently, Linux’s mail transfer agent Exim was reported to contain a remote code execution vulnerability (CVE-2019-15846). When the Exim server is accepting TLS connections, attackers could exploit this vulnerability to remotely execute arbitrary code with root privileges by sending an SNI ending in a backslash-null sequence. By default, the TLS function is disabled on the Exim server, but many users need to have this function enabled for processing network traffic.
Exim is a mail transfer agent (MTA), which is responsible for receiving, routing, and delivering email messages. Exim has been ported to most UNIX-like systems, including Solaris, AIX, and Linux. Since it can be flexibly configured, Exim is often used together with other applications. Currently, the vulnerability’s proof of concept (PoC) has not been made publicly available. Users are advised to upgrade as soon as possible to prevent attacks exploiting this vulnerability.
Reference:
http://exim.org/static/doc/security/CVE-2019-15846.txt
-
Scope of Impact
Affected Versions
- Exim Version < 4.92.2
Unaffected Versions
- Exim Version = 4.92.2
-
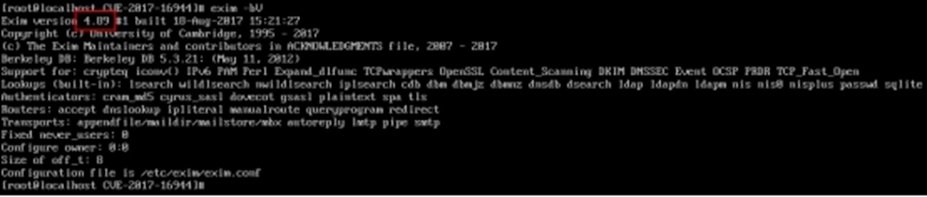
Vulnerability Detection
- Manual Detection
The exim -bV command can be executed to view the current version of Exim. If the version is included in the affected list, it indicates that Exim is vulnerable.
-
Mitigation
- Official Fix
Currently, this vulnerability has been fixed in Exim 4.92.2. Affected users are advised to upgrade to version 4.92.2 as soon as possible from the following link:
https://ftp.exim.org/pub/exim/exim4/
This vulnerability has also been fixed in operating systems and applications integrated with Exim. Related users should update as soon as possible.
| Product | Reference Link |
| Ubuntu | https://usn.ubuntu.com/4124-1/ |
| Debian | https://www.debian.org/security/2019/dsa-4517 |
| cPanel & WHM | https://documentation.cpanel.net/display/CKB/CVE-2019-15846+Exim |
- Workaround
If users who cannot upgrade to version 4.92.2 temporarily, they can prevent this vulnerability-based attacks by configuring the following rules to the email access control list (ACL) through Exim’s acl_smtp_mail.
| # to be prepended to your mail acl (the ACL referenced
# by the acl_smtp_mail main config option) deny condition = ${if eq{\\}{${substr{-1}{1}{$tls_in_sni}}}} deny condition = ${if eq{\\}{${substr{-1}{1}{$tls_in_peerdn}}}} |
Note: Configuring the preceding rules affects the TLS function, and therefore users are recommended to check whether this will impact their business before configuration.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Information Technology Co. Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.