Nowadays, the advancement of information technology has brought tremendous convenience to people. Whether it is social networking or ecommerce, the Internet has become an integral and essential part of our lives. As Internet brought new opportunities, it also created new threats. DDoS is one of the most destructive form of threats. In the past decade, DDoS has been weaponized by various organizations and individuals used for ransomware, revenge, even cyber warfare.
Background and History of DDoS Attack
Before we start, let’s look at the definition of what DoS and DDoS attacks are.
What is a DoS attack?
The simple explanation is, make a website or computer unavailable by overloading with traffic.
What is a DDoS attack?
In fact, with the growth of computing power and increasing availability of broadband network, denial service attack from a single host is no longer a serious problem. The attackers now launch aggregated attacks from multiple hosts to render the victim’s website or service inaccessible. This is called a “distributed†attack. The average attacker can’t organize a distributed attack, so “botnet” is typically used to launch distributed attacks.
What is a “botnet�
A botnet is a large-scale network consists of remotely controlled compromised computers or bots. Those hacked computers are also referred to as â€zombie computersâ€. A “botnet†tends to have large number of “Zombie computers†that are dispersed worldwide. The botnet is highly controllable, and the controller can disconnect from the botnet after issuing the command, and the control command will automatically propagate execution between the bots. It’s like an ecosystem of its own. For security researchers, you can discover many zombie hosts on botnet by capturing a node, but it’s challenging to see the whole picture, and even if you block some zombie hosts, it won’t affect the function of the entire botnet.
Evolution of DDoS
Now we have a basic understanding of DDoS, let’s take a look at how DDoS has evolved. In the beginning, hackers were mostly trying to show off their skills, so the choice of attack targets was very casual and entertaining. Later on, some religious organizations and organizations discovered the impact of this attack. They attacked specific targets for the purpose of extortion, retaliation, etc., and developed some corresponding tools to ensure the cost of attack was reduced. When state-level political forces are aware of this value, DDoS is beginning to be weaponized and easily used in cyber warfare against precise targets.
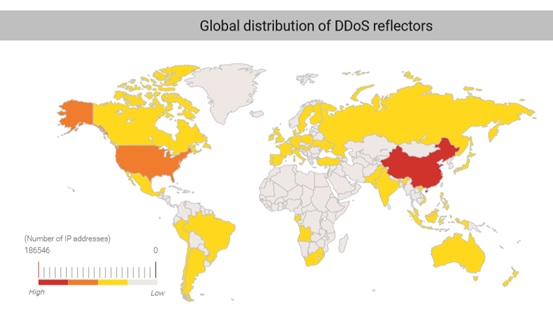
According to the latest DDoS analysis from NSFOCUS, China and the United States received most of the DDoS attacks.
DDoS attack methods
The essence of Distributed Denial of Service attacks is to use distributed clients to launch a large number of seemingly legitimate requests to the target, consuming a large amount of resources, thereby achieving the purpose of denial of service.
The four main attacks
1〠Attacks against Broadband networks
As with the traffic jam on the freeways, when the number of network packets reaches or exceeds the upper limit, there will be network congestion and slow response. DDoS uses this principle to send a large number of network data packets, which fills the entire bandwidth of the attacked target, thus causing the normal request to fail and achieving the purpose of denial of service. An attacker can use an ICMP flood attack (that is, send a large number of ICMP-related messages), or a UDP flood attack (that is, a large packet or packet that sends a user datagram protocol), use a forged source IP address to conceal, and cause congestion on the network. The attack victim would respond slowly or stop responding completely.
However, this direct method usually relies on the network performance of the controlled host itself, so the effect is not desirable, and it is easy to identify the source of the attack. The reflection attack was built to get around this limitation. The attackers send packets to the reflector servers with a source IP address set to their victim’s IP therefore indirectly overwhelming the victim with the response packets.
The reflector servers used for this purpose could be ordinary servers not obviously compromised, which makes this kind of attack particularly difficult to mitigate. When the reflector receives the data packet, it is deceived. The response data is sent to the target being attacked, and then the bandwidth resources of the target network are exhausted.
2〠Attack against the Operating System
Creating a TCP connection requires the client to interact with the server three times, this is often referred to as a “three-way handshake.” This information is usually stored in the server operating system’s connection table. The size of the connection table is limited.
After the amount of resource is exhausted, the server cannot create new TCP connections. When the attacker sends many TCP SYN packets, causing the server to generate many half-open connections in a short period of time, the connection table will be quickly filled up, resulting in the inability to establish a new TCP connection. This method is a SYN flood attack. Many attackers are more common.
3〠Application Attacks
Due to the popularity and importance of DNS and Web services, these two services have become the main targets of Distributed Denial of Service attacks. In the case of DDoS attack against DNS, many query requests are sent to the DNS server to achieve the effect of Denial of Service. If the domain name queried by each DNS resolution request is different, the server cached parsing record is effectively avoided, thereby achieving better resource consumption. When the availability of DNS services is impacted, large number of devices using their services would be affected. In recent years, Web technology has developed very rapidly.
If an attacker amasses large number of controlled hosts to continually send a large number of HTTP requests to the Web server and request the Web server to process it, it would completely consume the server resources and render the Web service inaccessible. Once a Web service is attacked by this type of attack, it will have a detrimental impact on the business.
4〠Combination Attacks
In real life, attackers don’t care which attack method they use as long as they can achieve their goals. They will generally launch with all their attack methods in their tool chest. For the targeted victims facing different protocols and Distributed Denial of Service attacks from diverse sources, the cost for the analysis, response and mitigation will be greatly increased. The attack trend suggests botnets are moving toward scale down model to reduce attack costs.
They are more also effectively hiding attack sources and evading security devices. This led to the gradual increases in low and slow type of application attacks. Therefore, from another perspective, two types of DDoS attacks on the rise: UDP and reflective high-traffic high-speed attacks, and multi-protocol small and slow attacks.
DDoS attack tools
As more and more open source DDoS tools become available, cyber attacks are becoming easier and the threats are getting greater. There are a lot of attacks tools available to the attackers Here is a brief introduction to several well-known ones, so that everyone can gain a basic understanding.
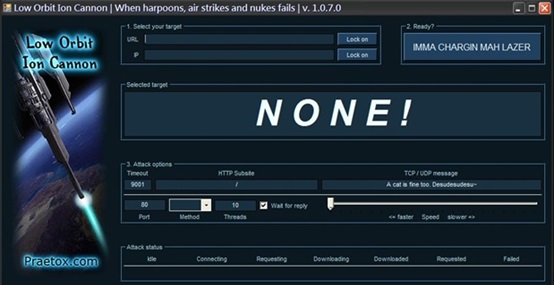
LOIC
The LOIC Low Orbit Ion Cannon is a flooding tool for the most popular DOS attacks. It generates a lot of traffic and can run on multiple platforms, including Linux, Windows, Mac OS, Android and more. As early as 2010, the tool was downloaded more than 30,000 times by hackers in attacks against companies and organizations that were against WikiLeaks.
The LOIC interface is friendly and easy to use, so beginners can get started quickly. Since the tool now requires a real IP address to download, Anonymous login is now deprecated.
HULK (HTTP Unbearable Load King)

HULK is another DOS attack tool. This tool uses UserAgent’s forgery to avoid attack detection. It can initiate high-frequency HTTP GET FLOOD requests to the target by starting 500 threads. It is imperative that each request is independent and can be bypassed. The server’s caching measures allow all requests to be processed. HULK is written in Python and is very handy for making changes to the source code.
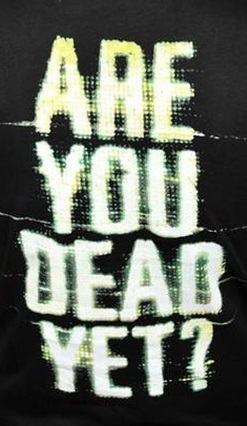
R.U.D.Y.
RU-Dead-Yet is a tool for DOS attacks using slow HTTP POST requests. It provides an interactive console menu that detects a given URL and allows the user to select which tables and fields to apply to POST-based DOS attack, the operation is very simple.
It is written in Python and very portable. R.U.D.Y. can attack all types of web server software, so the threat of attack is high. These tools continue to improve on the ease of use while maintaining attack power. They are open source and freely available to the public. As the war on cyber-attacks escalates, these tools will become more powerful and play a bigger role in future attacks.
Let’s now talk about how we can defend against attacks
DDoS attacks are just the mean to achieve goals. In the future, cyber warfare will have experience more extensive attacks, more frequent attacks, and more precise attacks. How should we deal with them when they strike?
Deploy high performance equipment
To ensure that network equipment will not become the bottleneck. When choosing routers, switches, firewalls and other equipment, try to use products with strong reputation and battle proven. You should have a strong relationship or agreement with your network provider. When large scale attacks occur, it is very effective to ask them to perform traffic restrictions upstream to combat certain types of DDoS attacks.
Adequate Bandwidth
The network bandwidth directly determines the ability to resist attacks. If there is only 100M of bandwidth, it is difficult to defend against the current SYN Flood attack no matter whatever the measures are taken. Therefore, it is best to choose a shared bandwidth of 1G with 10G backbone rather than a fix 100M connection.
Don’t forget to optimize the configuration
With adequate network bandwidth, you should also need to ensure your anti DDoS hardware can effectively defend against attacks of 100,000 SYN packets per second. It is also recommended to optimize resource usage and increase the load capacity of your web servers.
Abnormal Traffic Mitigation
The DDoS appliance cleans and filters the abnormal traffic through rule filtering of data packets, fingerprint detection, filtering of data streams, and custom filtering of data packets. It accurately determines whether inbound traffic is normal and further prohibit abnormal traffic from filtering.
Reducing the attack surface with static websites
Consider using static websites. Static sites have several major advantages over their dynamic counterparts, mainly faster speed and more secure. When a browser requests a static site it does not have to wait for any backend database connections or scripts to be run before the user can see the webpage. Since static websites generally don’t run scripts and don’t communicate with backend database, attack surface is reduced much of the vulnerabilities associated with java scripts and database.
Hybrid Anti-DDoS Solution
Nearly all industry experts recognize the fact that defeating the broad spectrum of DDoS attacks requires more than just cloud DDoS defenses, and more than just on-premises defenses. It requires both. From volumetric DDoS attacks to low-and-slow DDoS attacks, the best approach to defeat all DDoS attacks requires a combination of on-premises defenses and cloud defenses – called Hybrid DDoS Defenses. This approach defeats all DDoS attacks regardless of their size, duration, or frequency.
WHY HYBRID DDoS DEFENSES
When Hybrid DDoS Defenses are implemented, the on-premises defenses deployed in your network are completely capable of defeating attacks against customers – up to the point of your available Internet capacity. This is the only limitation to defeating all DDoS attacks, on-premises. If your capacity is nearly consumed by a massive attack, or collateral damage is being experienced, cloud defenses must be engaged to defeat attacks against infrastructure.
Summary
DDoS attacks are real and attack size are growing year over year. They are no longer big corporations’ problem only. Small and medium-sized companies are increasingly becoming the targets. Today, with the large-scale commoditization and distribution of sophisticated and yet easy to use cyber-attack tools, DDoS attack tools can be easily obtained by anyone. Today’s organizations need to be prepared to defend against DDoS attacks or risk outages and other damage. Searching effective-yet-efficient solution during an attack event is not a viable choice and is also too late. To protect yourself from devasting DDoS attack a thorough understanding of its misconceptions and protection measures implementation is a must. You must have an incident response plan in place and talk about DDoS countermeasures in advance with your ISP and a security vendor that specializes in mitigating these types of attacks. Finally, as with any challenge, always practice your incident response plan. Your business continuity, reputation and customers are well worth the effort.