DDoS Botnets
In 2019, NSFOCUS Security Labs detected over 400,000 DDoS attacks launched via botnets, a sharp increase compared with 2018 (8323 DDoS attacks). According to our observation, the
botnets running on IoT devices were mainly Mirai and Gafgyt families. These two families were exploited to launch over 60% of DDoS attacks in the first half of 2019. The following figure shows the proportions of high-risk commands observed by NSFOCUS Security Labs in 2018 and 2019.
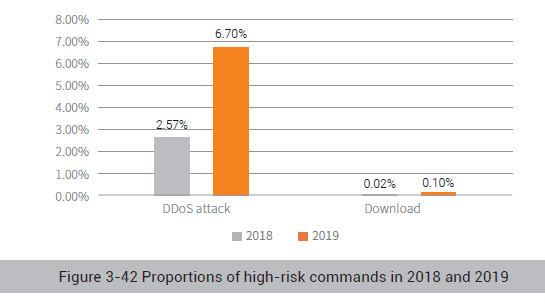
Compared with 2018, the attacks observed by NSFOCUS Security Labs increased significantly and the number of download directives saw a five-fold increase. The directives of downloading highrisk commands increased more rapidly than DDoS attack directives. This indicates that botnets not only continue to improve their DDoS attack capabilities, but also begin to develop a new trend of propagating other malware.
In terms of DDoS attack types, compared with 2018, UDP flood, TCP flood, and SYN flood attacks still dominated DDoS attacks in number.
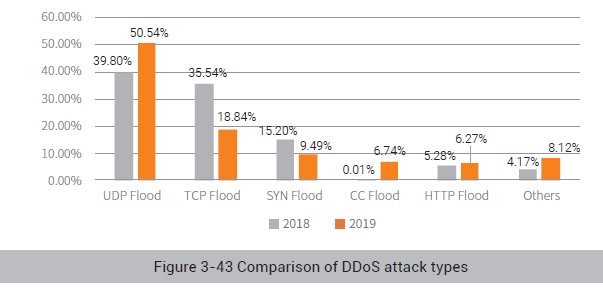
The following figure shows the proportions of current attacks by type in 2019. Compared with 2018, UDP attacks increased sharply, while TCP attacks decreased slightly. One of the reasons why TCP attacks decreased is that CC flood attacks surfaced as a new type of attacks.
Most DDoS attacks were launched via botnets. The following figure shows the activity of botnet families monitored by NSFOCUS Security Labs in 2019.
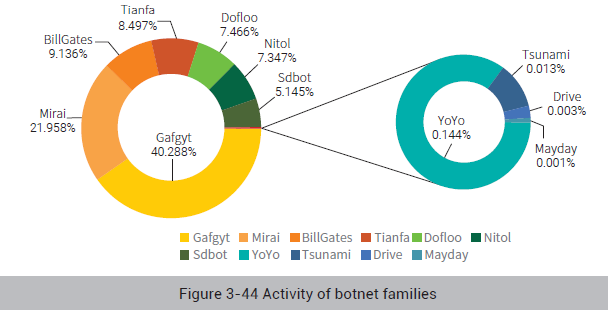
In 2019, botnet families mainly targeted IoT platforms, with Gafgyt and Mirai taking the largest proportion. Though the BillGates family was exploited to launch DDoS attacks most frequently in
2018, the number of such attacks declined greatly in 2019. We believe that in a scenario where the BaaS model becomes increasingly mature, attackers prefer to exploit open-source DDoS families for automatic deployment.
According to the monitoring of NSFOCUS Security Labs, the propagation methods used by botnets during the expansion were upgraded from 2018. The exploit payload of IoT botnet families in 2019 shared similarities with that in 2018, mainly targeting smart IoT devices by exploiting CVE-2017-17215 and CVE-2014-8361 vulnerabilities.
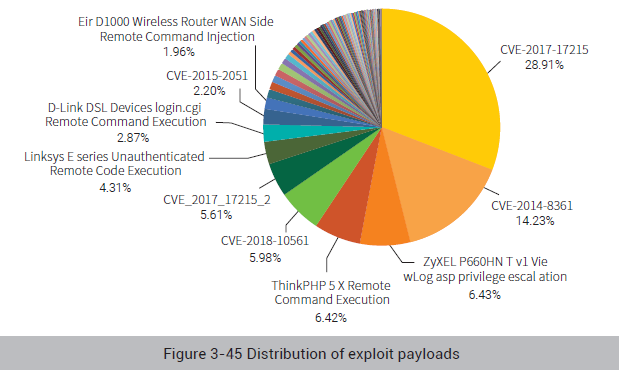
At the same time, the number of IoT family-based exploits hit the three-digit mark for the first time, reaching 103, with a broad chronological span.
Windows botnet families tend to spread by exploiting weak passwords, phishing documents, and CVE vulnerabilities. Phishing document-based spreading can be subdivided into macro viruses-based spreading and Office vulnerabilities-based spreading. The following figure shows their respective proportions.
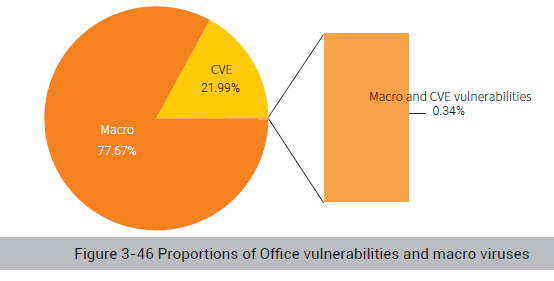
As a representative of vulnerabilities that spread via system-level CVE vulnerabilities, the EternalBlue vulnerability is widely found in the spreading process of cryptominers and ransomware.
The following sections dwell upon the most active DDoS families, Gafgyt and Mirai.
To be continued.