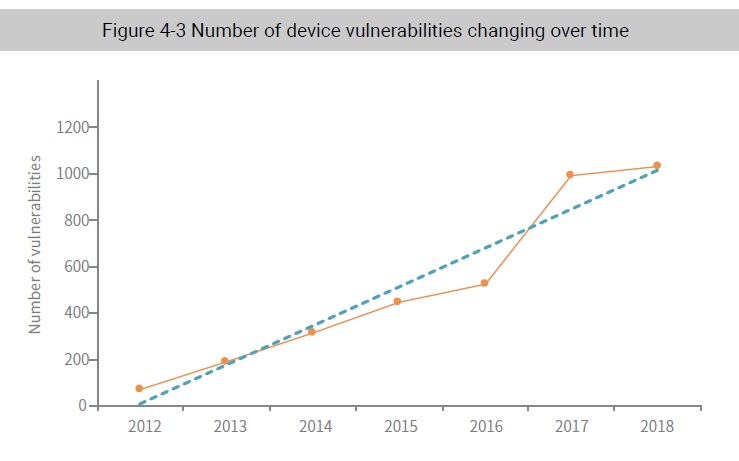
4.2 Significant Increase in Device Vulnerabilities
In the past few years, vulnerabilities associated with network devices have grown rapidly. This is because more network enabled devices of more diverse types are connecting to the network. The threat increases as device vendors do not take security seriously and are remiss in providing timely firmware updates. Thus, the discovery of more vulnerabilities is not that difficult.
With the significant increase in network enabled devices, hackers have no shortage of targets to go after. They are easy to hack due to poor security design. Once they are successfully exploited, attackers easily gain administrator privileges. It is no surprise then that these vulnerabilities are naturally attractive to attackers. Thus, security vendors and cybersecurity professionals should pay special attention to these vulnerabilities and explore proper defense techniques and solutions.
Among all CVE vulnerabilities disclosed in 2018, 986 are related to network enabled devices, including 482 high-risk ones (which account for 12% of total high-risk vulnerabilities). According to preliminary statistics, these 986 vulnerabilities are found in 1503 devices from 145 vendors, including processors, routers, cameras, and smart devices.
In January 2018, Google’s security team disclosed two types of vulnerabilities in CPU chips, namely “Meltdown” (CVE-2017-5754) and “Spectre” (CVE-2017-5753/ CVE-2017-5715), which were believed to be the most serious security issues found till then. In the following year, 14 more vulnerabilities similar to Meltdown and 13 others like Spectre were discovered.15
Meltdown breaks the most fundamental isolation between user applications and the operating system. It allows a program to access the memory, and thus also the sensitive data from other programs and operating system. This vulnerability “melts down” security boundaries implemented by hardware, allowing lower-privilege applications to access system memory across boundaries leading to data leaks.
Spectre, a class of hardware vulnerabilities that affects modern microprocessors performing branch prediction. It allows a malicious process to access the memory of other programs, making it possible for an attacker to read the content of the accessed memory. All Spectre vulnerabilities are based on exploiting side effects of speculative execution, a common means of reducing memory latency and speeding up execution in modern microprocessors. In particular, Spectre centers on branch prediction, a special case of speculative execution.
Being hardware-related, Spectre cannot be fixed through microcode updates and requires kernel-level fixes. According to studies, remediating these vulnerabilities may decrease performance by 5%–30%.
As for vulnerabilities in routers, the situation is also severe. According to Securing IoT Devices: How Safe Is Your Wi-Fi Router 26 published by The American Consumer Institute, 83% of Wi-Fi routers were found to have known vulnerabilities. These routers, if not updated in time, would become an entry point for cyberattacks. Attackers can gain access to devices connected to the router to launch DDoS attacks and collect your financial and personal information.
In March 2018, Cisco disclosed a remote code execution vulnerability (CVE-2018-0171). On April 6, a hacker group dubbed JHT exploited this vulnerability to attack network infrastructure of several countries, including Russia and Iran.
On April 30, 2018, researcher “vpnMentor” disclosed two high-risk vulnerabilities in TP-Link’s GPON routers: authentication bypass vulnerability (CVE-2018-10561) and command injection vulnerability (CVE-2018-10562). These two vulnerabilities allow attackers to execute arbitrary commands on GPON routers by sending only one request. Within 10 days after disclosure, these vulnerabilities were actively exploited by several botnet families to build zombie corps and were delivered over the Internet as worms.
To be continued.
5 https://www.kaspersky.com/blog/35c3-spectre-meltdown-2019/25268/
6 https://www.theamericanconsumer.org/wp-content/uploads/2018/09/FINAL-Wi-Fi-Router-Vulnerabilities. pdf