6.3 Worm
In the 2018 H1 Cybersecurity Insights , we pointed out that most worm viruses were discovered more than five years ago. This indicates how capable these viruses are of propagating and evolving and how difficult it is to remove them completely from the network. According to data throughout the year, this was still the case. In 2018, we detected a total of 39 types of active worm viruses, 60% of which were discovered over five years ago.
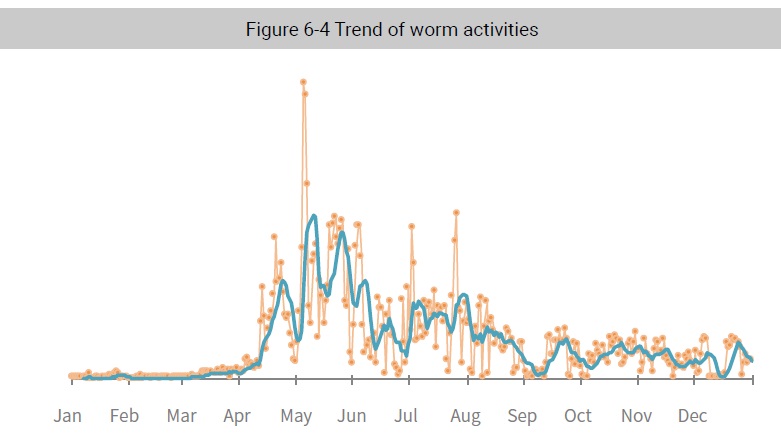
Worm activity was quite low in the first quarter but sharply increased in April reaching the annual peak in May. In the second half of 2018, the number of worm activities slightly fluctuated, showing an overall downward trend. The most active worm viruses in 2018 were:
- W32.Faedevour: It was particularly active in the first half of 2018 and ranked No.1 in terms of malicious activities throughout 2018, far ahead of ranking No. 2. W32.Faedevour opens a backdoor
into an affected computer to steal information while executing remote attackers’ commands of taking screenshots, downloading files, sending files, and attempt to spread via a network driver and shared file folder. - SQL Slammer: It exploited SQL server vulnerabilities to launch DoS against port 1434 and infect the SQL server in the memory. Then it used the infected SQL server for DoS and malware propagation & infection, causing the SQL server to work improperly or collapse and finally leading to internal network congestion.
6.4 Remote Access Trojan
Trojans attempt information theft and running complex remote controls. Unlike common viruses, Trojans are not self-propagating and do not “deliberately” infect other files. Concealing themselves using disguise and stealth, these viruses entice users to download and execute them, opening a door for the attacker to break into the victim’s computer to destroy or steal files or remotely control the infected computer.
2018 witnessed the most information disclosure events. Victims including Facebook, AcFun, YTO Express, Huazhu Hotels, and Marriot, suffered the theft of hundreds of millions of personal information records. Login credentials, sensitive files, and banking & payment information are still hackers’ favorite targets.
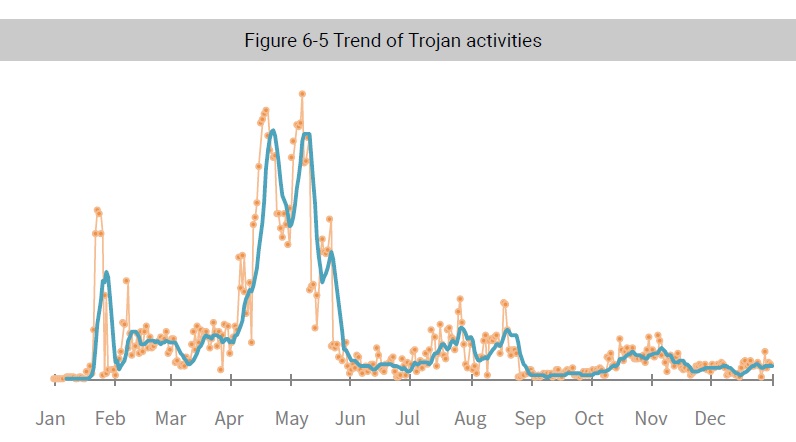
In the first half of 2018, Trojans were quite active with bursts of activity seen from early April to the end of May. They were sluggish in the second half of the year, with some minor fluctuations. While Trojans overall were less active, new bootkits kept emerging. Since 2015, bootkits have infected millions of computers. After several updates and iterations, related variants have sprung up like mushrooms and are difficult to eradicate. The bootkit trojan is one of the most complicated Trojans ever discovered, reaching every corner of the internet, dark or light.
The XCodeGhost trojan was second only to bootkits, in terms of communication activity. The XCodeGhost trojan has garnered wide attention from the security industry since its debut in 2015.
Originally an Apple app development tool, Xcode was used by criminals to inject malicious code into the Xcode installation package and leak it to the Internet. Many app users are affected because some developers, instead of downloading Xcode from a trusted source, used an untrusted tool embedded with malicious code for app compilation. The controller could collect information from users’ devices or even direct such devices to launch other attacks. This sounded an alarm to both developers and enterprises, but the best defenses against it are software code audits and security testing.
6.5 Zombie
Botnets have always been a danger not to be ignored in the Internet environment. Common and malicious, a botnet program is well concealed and has the characteristics of both the worm and
Trojan. It can gain control of the target host via loopholes or other vulnerabilities, and it can steal the information in the target host or manipulate the host to carry out network attacks. A botnet has the capability of being a significant medium for carrying out network attacks. It can initiate multiple attacks by controlling many zombies, and it can even initiate unknown attacks in combination with new types of attacks. Common attack practices include DDoS attacks, sending junk mail, ransomware, and abuse of resources.
Botnets currently have mature business operations. Under the model of BaaS (Botnet as a Service), platforms are becoming more and more mature. Ordinary users can initiate large-scale botnet attacks through simple operations. The threshold of attackers has been greatly lowered.
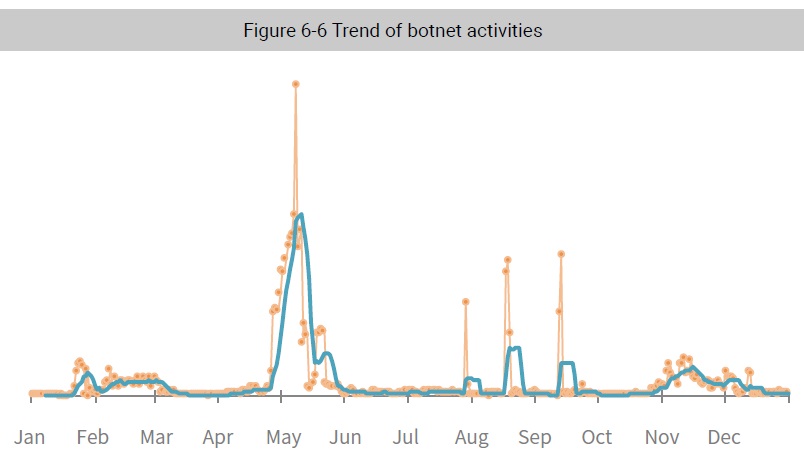
As can be seen in the data from the monitoring of botnets throughout the year, May was the outbreak month of bot activity. The number of attacks in other months was relatively lower, with slight fluctuations. As we mentioned in “2018 H1 Cybersecurity Insights Report216”, the BillGates botnet and Artemis botnet families were very active. According to the data for all of 2018, BillGates was the most active, far and away exceeding other families.
BillGates, which was first disclosed in 2014, is a multi-platform family and mainly runs on *nix platforms. In the four years since its birth, the BillGates family has continued to develop. The Webtoos variant operating on the Windows platform and the BillGates.lite series of variants specifically for infecting arm and other embedded devices were successively created. As it provides a UI that makes it easy for attackers to use, the BillGates family is very popular among hacker groups. In the first quarter of 2018, it entered the fully active period. Many attacks were launched within a short period of time, and then it turned to a silent mode very quickly. The fact that the attacks lasted for a long time and that the scope of the attacks was extensive is of great value for analysis and tracing.
Gafgyt is very active in the IoT field. We have been conducting long-term tracking of this family since 2017. As we pointed out in the “2018 Botnet Trend Report”, Gafgyt family botnets have transformed, going from the conventional profit model of selling attack traffic to providing lease services of zombie hosts via cloud platforms. Under such a sales model, the threshold of using a botnet will be further lowered, and attacks will inevitably affect more fields. Thus, if this model becomes the mainstream, botnets will present a higher level of threat.
To be continued.
16 https://nsfocusglobal.com/2018-h1-cybersecurity-insights/