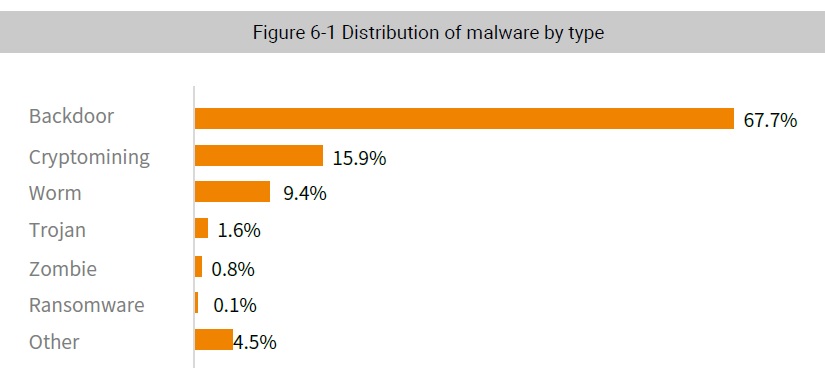
Backdoor, cryptominer, worm, trojan, and zombie115 made the list of active most malware in 2018. Strains of backdoors malware are still extremely active because they are too stealthy to be easily detected. As the virtual currency market continues to shrink, cryptomining is less popular than before, but still very active, coming second behind backdoors.
6.1 Backdoor
In information security, a backdoor is a method of bypassing security restrictions to gain access to a process or system, for later re-access or to take control of the system. This is often done by tricking a user into downloading or opening a file with malicious code, creating a backdoor in the victim computer without the user’s knowledge. Alternatively, attackers can create a backdoor on a host compromised by other attack methods, making it possible to intrude the system at any time in a stealthy way to avoid detection.
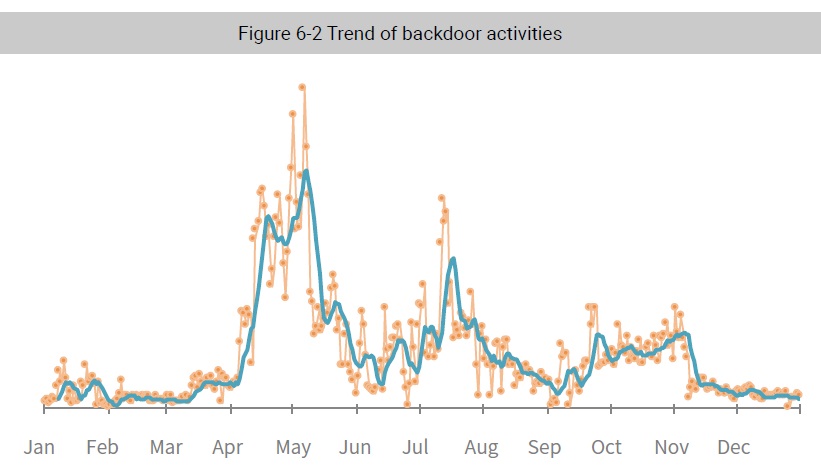
From January to the end of March, backdoor activity was relatively low and fluctuated only slightly. From April to the end of October, however, backdoor activity swung wildly. April and May saw the most backdoor activities. From December, the amount of backdoor activities began to decrease.
As early as 2014, routers from NetCore, a Chinese electronics vendor, were reported to have a high privileged backdoor vulnerability available. Attackers could exploit the vulnerability existing in NetCore routers to obtain root privileges, taking full control of affected products. Vulnerable routers are still used on the Internet, and are exploited by the Gafgyt botnet. According to the monitoring data in 2018, activities exploiting the NetCore router backdoor were quite rampant.
6.2 Cryptominer
In 2017, with cryptocurrency prices soaring, most traditional malware operators, driven by profits, turned their eyes to cryptomining. Bitcoin, Monero, and Ether were actively traded at that time. Data shows that there are 1600 cryptocurrencies in the world, with a total market capitalization of USD 340 billion. In 2018, a sharp drop in cryptocurrency prices reduced. But did not halt, cryptomining activity. The market was and still is active making cryptomining an important method for attackers to make profits, with no sign of declining in the future.
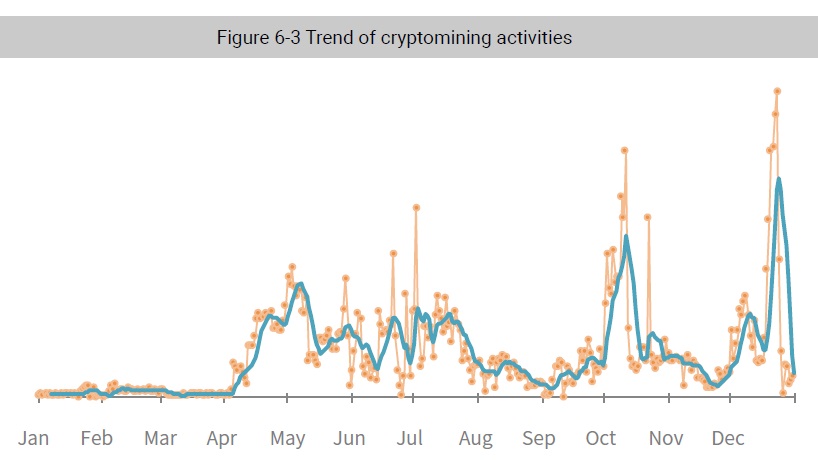
In 2018, cryptomining malware exhibited different degrees of activity, but showed an overall upward trend. Starting in April, cryptomining activities began to increase and reached a peak in the middle of May. Compared with the first half of 2018, cryptomining activities in the second half went more turbulent. In August and September, cryptomining activities experienced a downturn but rapidly increased in October then hit their lowest point in November. However, activity quickly bounced back, reaching the annual peak in December.
It is important to note that WannaMine was the most active mining virus, which exploited EternelBlue vulnerabilities for propagation. EternelBlue is an attack developed by the Equation Group and the U.S. National Security Agency (NSA), which exploits SMB vulnerabilities in Windows systems to obtain the highest privileges.
In 2017, WannaCry swept across the globe. This ransomware attacked the entirety of Europe (including UK and Russia) and China within just five hours. It affected as many as 150 countries and caused extremely serious economic losses. Likewise, the WannaMine family was also the major player to exploit EternelBlue vulnerabilities in 2018. Spreading at an alarming rate, its cryptomining activities accounted for 70% of all cryptomining activities detected in the first half of the year. It is no surprise EternelBlue exploits are favored by most cryptomining virus families as an attack weapon; though EternelBlue vulnerabilities have been known since May 2017, attacks exploiting these vulnerabilities have never failed. This definitely needs attend from professionals of all sectors.
Monitoring cryptomining activities in 2018, we found that cryptominers preferred Monero to Bitcoin. This is because Monero, with anonymity and covertness, does not require the wallet address during transactions, and thus can better protect privacy of traders. In addition, Monero makes cryptomining so easy that any CPU or GPU can participate in these malicious activities. Monero, while open to mining by common users, provides more opportunities for hackers to make profits.
To be continued.
15 There is no uniform standard for classifying viruses. We roughly classify viruses according to the essential nature or functionality of code as follows: worms are characterized by the large-scale self-propagating capability; Trojans take information theft and other complicated actions like remote control as their core functionality; bot programs are characterized by construction of botnets from computer clusters for large-scale hacking activities (such as DDoS attacks and cryptomining); backdoors and Trojans are much alike, but the former are mostly used to provide a persistent entrance for further attacks.