1. Background
In early 2020, the US Department of Defense (DOD) released the Cybersecurity Maturity Model Classification (CMMC).

On average, the USA loses USD 600 billion a year to adversaries in the cyberspace. Currently, the DOD has about 300,000 contractors, covering a variety of fields from hypersonic weapons to leather factories. Of all these contractors, about 290,000 virtually have no cybersecurity measures. In the past few years, the US Government has stepped up efforts in regulating the defense supply chain, with cybersecurity as the top concern.
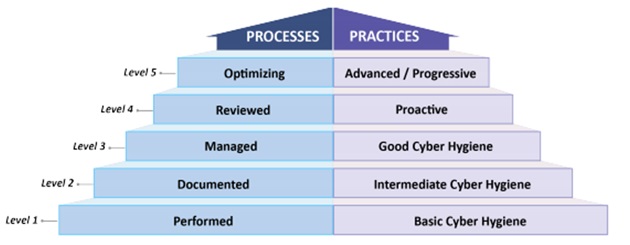
The CMMC maps cybersecurity best practices and processes to five levels. A vendor that wants to attain certification for a certain level must meet requirements of that level and demonstrate achievement of lower levels.
For vendors, it is very important to be CMMC-compliant because the level they are evaluated to achieve determines what project contracts they are entitled to. But to be CMMC-compliant, what challenges should they overcome?
2. Challenges
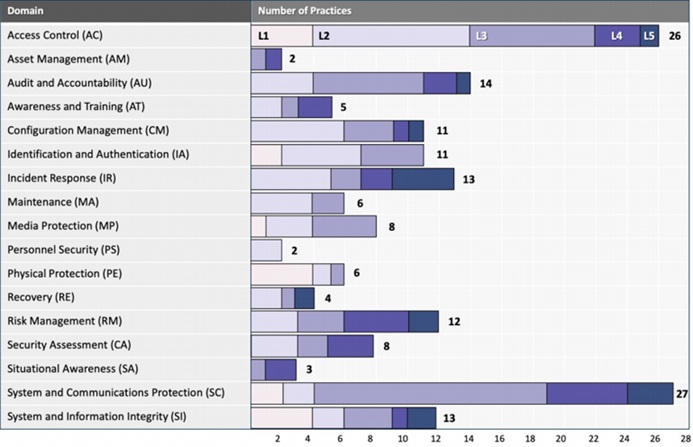
The CMMC contains a variety of capability domains from physical security to personnel security and to asset management. However, the CMMC’s goal is not just to make vendors comply with its requirements but to require them to possess comprehensive cybersecurity capabilities, with which they will be capable enough to cope with future threats.
Vendors who are preparing for CMMC certification must take into account their industrial control system (ICS) environments. Today, no manufacturer can operate without using ICSs, and modern attacks are often executed across IT/OT borders. Besides, some CMMC capabilities do not apply in ICS network environments. Asset discovery, threat detection, and incident response are capabilities equally important in IT networks and ICS network environments.
While CMMC has many specific requirements, most of them can be summed up with broader considerations. The following sections delve deeper into considerations to be made in four aspects to make ICS networks CMMC-compliant.
3. Four Considerations
3.1 Visibility into Assets in ICS Network Environments
Without knowing what assets are on a network, the network owner does not know what to protect and cannot make data-driven decisions on how to approach cybersecurity. At present, many organizations do not know how many devices are on their ICS networks or what vulnerabilities are in their devices, let alone how these assets communicate with and connect to one another. Without this information, it is impossible to nail down an appropriate strategy to mitigate cybersecurity risks.
Before gaining visibility into assets in its ICS network environment, an organization cannot address CMMC compliance for its ICS network. Such visibility is not limited to assets and their properties but extends to risks and vulnerabilities, such as unauthorized connections to the Internet or unpatched devices.
3.2 Robustness of the ICS Network Architecture
The visibility into assets and their properties and communication is also crucial to this issue. The CMMC is focused on building a stronger overall cybersecurity posture in DOD supply chain contractors, in which building a strong overall approach to ICS network security is extremely important.
With visibility into ICS device communications, one can verify that his or her ICS network architecture is as strong as expected, for example, make sure that devices are communicating only with the Internet as intended, or make stronger network segmentation rules.
3.3 Vulnerabilities That Could Put Organizations at Risk
Many CMMC requirements focus on identifying and addressing system or device vulnerabilities. In the case of ICS networks, these could mean unfixed CVEs, malfunctioning devices, or the use of unauthorized ports. CMMC capability domains require that organizations be able to detect and prioritize such vulnerabilities so as to manage and address risks on an ongoing basis.
3.4 Detection of Threats Targeting ICS Systems
Compared with detection of threats targeting IT systems, detecting ICS threats can be very different. While IT threats are often detected and blocked by endpoint detection and antivirus software, most embedded ICS devices do not support such methods and are typically invisible to IT teams. Therefore, the approach to ICS threat detection should incorporate ICS-aware behavioral analytics and traffic analysis.
4. Conclusion
While CMMC requirements dive into deeper specifics, most of them are closely related to the four considerations discussed here. Addressing these considerations for ICS security will be a good place to start to make ICS networks CMMC-compliant.
By providing a brief introduction to the CMMC model released by the US Department of Defenses, this document is aimed at informing China’s development of vendor assessment systems for the national defenses and critical infrastructure sectors. Including the cybersecurity aspect in vendors’ capability assessment lists will help the country cope with cyber threats in an increasingly complicated international environment.
References:
1. https://cyberx-labs.com/blog/four-considerations-for-making-your-iot-ics-networks-cmmc-compliant/
