The Future of Data Protection: The Emergence of Confidential Computing
In today’s information age, data has become an invaluable resource ubiquitous across various sectors, from financial institutions to healthcare and scientific research. However, as data continues to grow, concerns about data privacy and security become increasingly prominent. Incidents of data breaches, hacking, and misuse of personal information are common, leading to concerns about how to better protect sensitive information. While traditional encryption technologies provide some protection during data transmission and storage, there are potential risks during data analysis and processing when the data needs to be decrypted. It is in this context that Confidential Computing technology has emerged.
Representing an innovative field in computer science, Confidential Computing aims to protect the confidentiality of data even during computation. It employs advanced encryption techniques to keep data encrypted during computation and analysis, allowing only authorized users to access and use the data, preventing others from peering into its contents. This technology provides robust protection for data privacy and security while still allowing data analysis and computation without exposing its content. Its potential extends beyond individual privacy protection to various domains such as finance, healthcare, scientific research, and national security, offering innovative solutions to the challenges of data protection.
Introduction to Confidential Computing
Technical Overview
Confidential Computing is one of the privacy-enhancing computing technologies, with a key focus on protecting actively used data. The core idea involves executing computations in a Trusted Execution Environment (TEE) at the hardware level to ensure data security.(1) Normally, computation components on a computer and data in memory exist in a decrypted state, making them vulnerable to unauthorized software or administrator viewing or manipulation. TEE provides a protected environment, ensuring that only authorized computing processes can access and operate on data without being affected or leaked externally. Thus, TEE’s primary role is to prevent unauthorized access or modification of applications and data in use, thereby enhancing the security level of managing sensitive or regulated data.
The Confidential Computing Consortium (CCC) suggests that Confidential Computing should have at least three properties to protect data in use:(2)
- Data confidentiality: Unauthorized entities cannot view data while it is in use within the TEE.
- Data integrity: Unauthorized entities cannot add, delete, or alter data while it is in use within the TEE.
- Code integrity: Unauthorized entities cannot add, delete, or alter code executing in the TEE.
Common Types of Confidential Computing
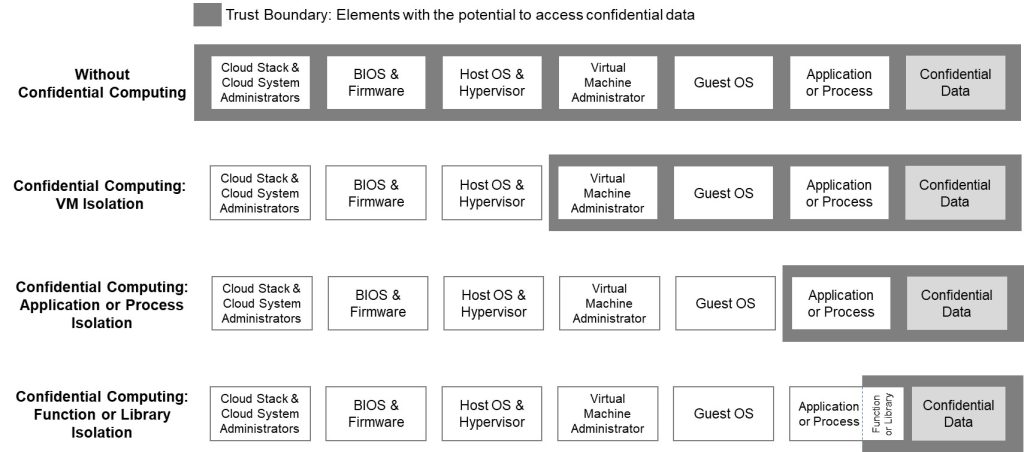
The concept of the “Trust Boundary” defines which elements might access confidential data, whether benign or malicious. Depending on the definition of the “Trust Boundary,” different types of Confidential Computing technologies emerge, primarily three types(3) (4):
- Virtual Machine Level Isolation: Only elements within virtual machines running on the infrastructure can access potential data.
- Process Level Isolation: Only authorized software applications or processes can access data.
- Function Isolation: Only authorized subroutines or modules within large applications can access data, preventing access by any other unauthorized elements, including untrusted code within large applications.
Virtual Machine Level Isolation is represented by CPU vendors such as Haiguang CSV and AMD SEV, while Process Level Isolation is represented by CPU vendors like Intel SGX.
Comparison with Related Technologies
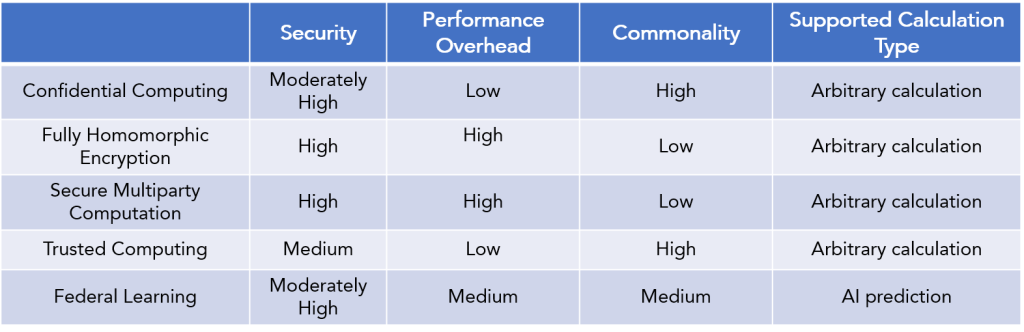
Confidential Computing technology is often compared with other privacy-enhancing computing technologies, including Fully Homomorphic Encryption, Secure Multiparty Computation, Trusted Computing, and Federated Learning. These technologies aim to achieve data availability without visibility, but they differ in security, performance overhead, generality, and supported computation types.
- Fully Homomorphic Encryption allows computations on encrypted data, providing high privacy protection. However, it incurs significant computational overhead, requires knowledge of cryptographic principles for encoding, and has lower generality.
- Secure Multiparty Computation enables collaboration on computations without revealing private data. While ensuring data availability without visibility, it involves substantial computational overhead, long communication times, and requires specific application-specific coding, limiting its generality.
- Trusted Computing aims to establish trust in computing systems using standardized hardware mechanisms, such as Trusted Platform Modules. While sharing similar security concepts with Confidential Computing, Trusted Computing does not encrypt memory, whereas Confidential Computing ensures the confidentiality and integrity of code and data used through memory encryption.
- Federated Learning is a decentralized machine learning technology allowing multiple participants to collaboratively train AI models without sharing raw data. It reduces the risk of data leakage, but its decentralized nature introduces some performance overhead. Notably, Federated Learning is not suitable for all computation types, primarily supporting collaborative modeling of multi-party data rather than typical computation tasks.
Applications of Confidential Computing
The applications of Confidential Computing can be summarized into three main categories: secure outsourcing of computation and cloud computing, multi-party collaborative computing, and secure data sharing. The following sections provide detailed explanations of these three application scenarios.
Secure Outsourcing of Computation and Cloud Computing
Enterprises often require tasks involving significant computational resources, such as data cleaning and analysis. In such cases, enterprises can choose to outsource data processing tasks to third-party service providers to reduce hardware, manpower, and operational costs. However, this introduces the risk of data leakage, as outsourcing service providers can access the enterprise’s processed data. To address this challenge, Confidential Computing technology comes into play. It allows enterprises to maintain data privacy and security while outsourcing computation. Using Confidential Computing, outsourcing service providers cannot access the data being processed by the enterprise because the data undergoes encryption during computation, preserving data confidentiality without exposing the plaintext content. This enables enterprises to lower costs and increase efficiency without worrying about the risk of data leakage.
Cloud computing is the most common form of outsourcing computation. In traditional cloud computing environments, cloud service providers typically have access to the data processed by users on their platforms. However, using Confidential Computing technology in a cloud computing environment alleviates concerns about cloud service providers or other users accessing data processed in the cloud. This contributes to increased data privacy and security. For example, enterprises can use Confidential Computing to protect their machine learning models, allowing them to train in a cloud environment without disclosing sensitive training data. Similarly, financial institutions can upload customer transaction data to the cloud for risk assessment and fraud detection while ensuring that cloud service providers cannot access customer’s private data.
Multi-party Collaborative Computing
Confidential Computing enables collaboration between multiple organizations or individuals for data analysis or computation without sharing original data. Here are four examples:
- Medical Research and Collaboration: Multiple medical research institutions can collaboratively analyze large-scale medical data, such as genomic data and case records, to study disease treatment and prevention. Using Confidential Computing, these institutions can share data and analysis results without revealing patient identities and sensitive information.
- Financial Risk Assessment: Different financial institutions and insurance companies can collaborate on risk assessment by sharing customer credit data to determine loan or insurance conditions. Confidential Computing allows them to collaborate while protecting customer privacy.
- Supply Chain Management: Various participants in supply chains, such as manufacturers, suppliers, and logistics companies, can collaborate to improve supply chain efficiency and visibility. They can use Confidential Computing to share critical supply chain data, such as inventory, transportation, and order information, while preserving business confidentiality.
- Multi-party Data Modeling: Confidential Computing empowers multi-party data modeling, allowing multiple data participants to collaborate in creating models without sharing raw data. This is crucial for protecting data privacy and compliance, as data remains encrypted and does not need to be exposed to other collaborators. This ensures data security and privacy while allowing multiple parties to collaborate in creating more accurate models.
Data Security Sharing
For data-rich entities such as telecommunications operators and governments, data plays a dual role in the new era. On one hand, data has become a valuable asset that can promote social development and industry progress; on the other hand, these entities must shoulder the responsibility of protecting data assets. They need to achieve data sharing to drive social development while ensuring the security of shared data. Here are two examples:
Telecommunications operators sharing user location data with advertising companies: Advertising companies can leverage this data to provide users with location-specific advertisements, such as recommending nearby restaurants or shops on the user’s mobile app. By employing confidential computing technology, data can be securely shared, aiding advertising companies in delivering more accurate ad services while ensuring the security of the telecommunications operator’s data, avoiding the leakage of personal privacy data.
Government sharing anti-money laundering (AML) data with financial institutions: Government agencies, such as financial intelligence units, provide information to financial institutions regarding suspicious transactions, accounts, and clients, which may include signs of money laundering, such as large transactions, frequent cash deposits, and cross-border transfers. Financial institutions can use this data to enhance due diligence on clients and report suspicious transactions to ensure compliance with anti-money laundering regulations. The use of confidential computing technology can ensure the secure sharing of data, assisting financial institutions in their anti-money laundering efforts and protecting the security of government data, preventing the leakage of personal privacy data.
Future Prospects of Confidential Computing
Confidential Computing Consortium (CCC)
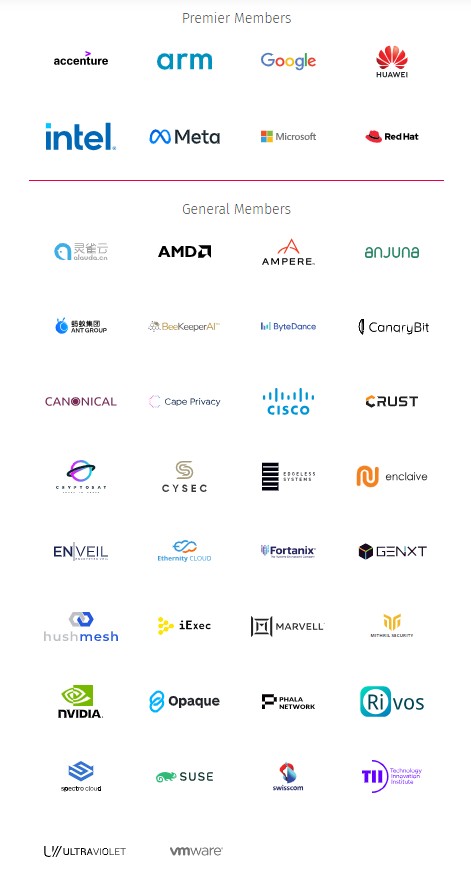
Confidential computing technology is primarily driven by the Confidential Computing Consortium (CCC), a project community under the Linux Foundation, aimed at accelerating the application of confidential computing through open collaboration(6). The consortium brings together hardware providers, cloud computing providers, and confidential computing service providers, with its main member units illustrated in the following figure.
Future Market Estimates
In 2020, Gartner listed confidential computing as one of the 33 key security technologies in its annual “Top Actions from Gartner Hype Cycle for Cloud Security 2020.”(7) In recent years, several market research and consulting firms have predicted rapid growth in the future market for confidential computing.
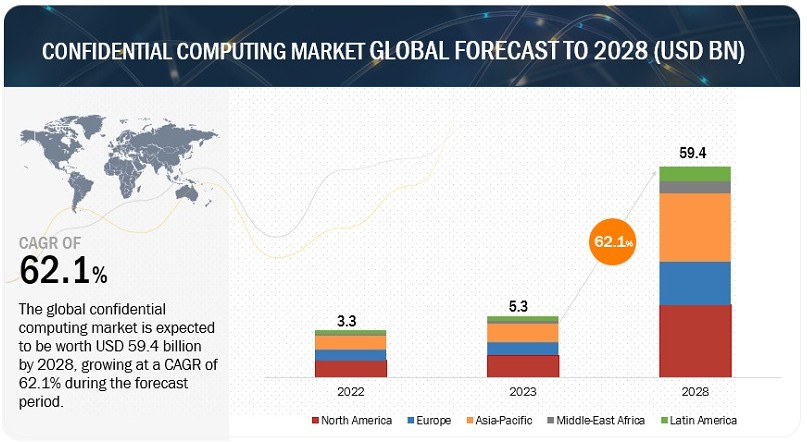
MarketsandMarkets, established in 2009, is one of the renowned consulting firms in the United States. (8) In May 2023, the company released a report on the analysis of the confidential computing market. (9) The report predicts the market share of confidential computing in five regions, namely North America, Europe, East Asia, the Middle East & Africa, and Latin America, during the period from 2023 to 2028. The market share is composed of hardware, software, and services related to confidential computing. According to the report, the global market share of confidential computing will reach $5.3 billion in 2023 and will grow to $59.4 billion by 2028, with a compound annual growth rate (CAGR) of 62.1%.
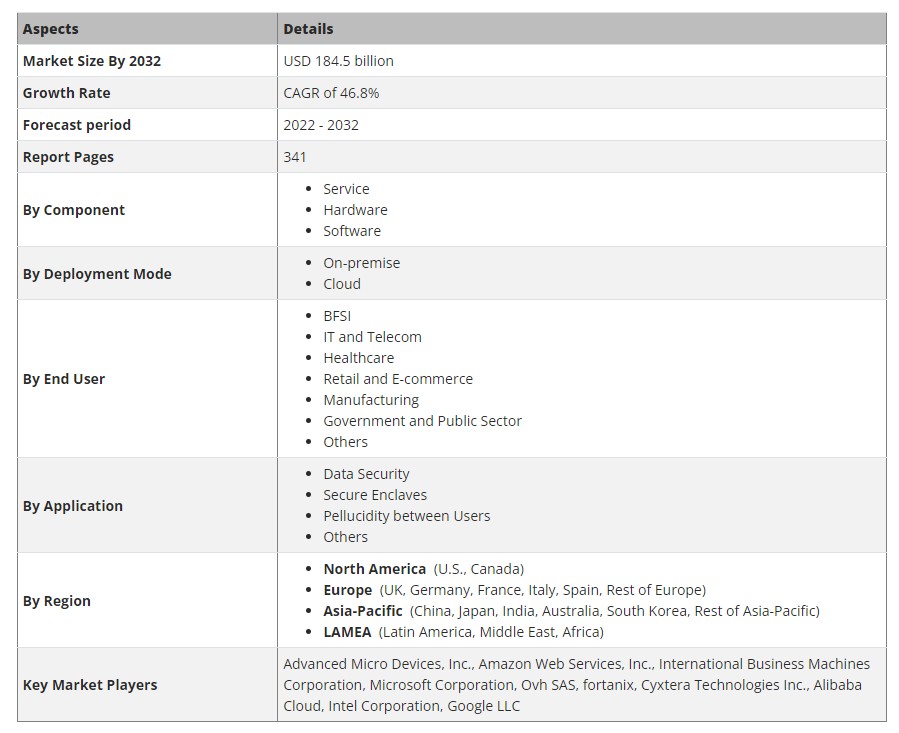
Allied Market Research, founded in 2013, is another prominent consulting firm in the United States. (10) The company released a report on the analysis of the confidential computing market in 2023. (11) Unlike MarketsandMarkets, Allied Market Research, in this report, forecasts the market share of the global confidential computing market for the period 2023 to 2032. The market share comprises hardware, software, and services related to confidential computing. According to the report’s predictions, by the year 2032, the global market share for confidential computing is expected to reach $184.5 billion, with a compound annual growth rate of 46.8%.
Conclusion
This article first introduced the background of the emergence of confidential computing technology, then detailed its characteristics, common types, and comparisons with other similar technologies. In the third chapter, we summarized the three main application areas of confidential computing, including secure outsourcing computing and cloud computing, multi-party collaborative computing, and secure data sharing. Finally, we introduced the main organization in the field of confidential computing, the CCC consortium and its members, and discussed the future market predictions for confidential computing (the market for confidential computing is expected to grow rapidly in the next 5-8 years).
In summary, the innovative prospects of confidential computing technology are changing our digital world. In terms of data security and privacy protection, it provides unprecedented opportunities. In the future, we can expect to see the widespread application of confidential computing in various fields, from finance to healthcare, from cloud computing to the Internet of Things. Let’s closely monitor the evolution of this technology and contribute to a more secure digital future.
References:
(1) https://ieeexplore.ieee.org/document/9935045
(5) https://en.wikipedia.org/wiki/Confidential_computing
(6) https://confidentialcomputing.io/about/
(8) https://www.marketsandmarkets.com/AboutUs-8.html
(9) https://www.marketsandmarkets.com/Market-Reports/confidential-computing-market-27796261.html
(10) https://www.alliedmarketresearch.com/about-us
(11) https://www.alliedmarketresearch.com/confidential-computing-market-A188159