Efficiency is Key to Cybersecurity in the Post-Cloud Era
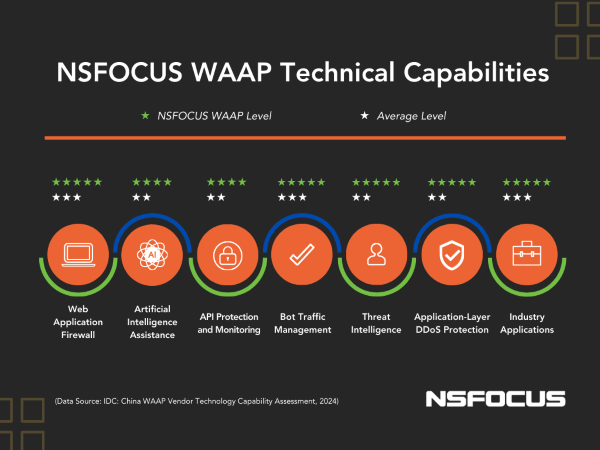
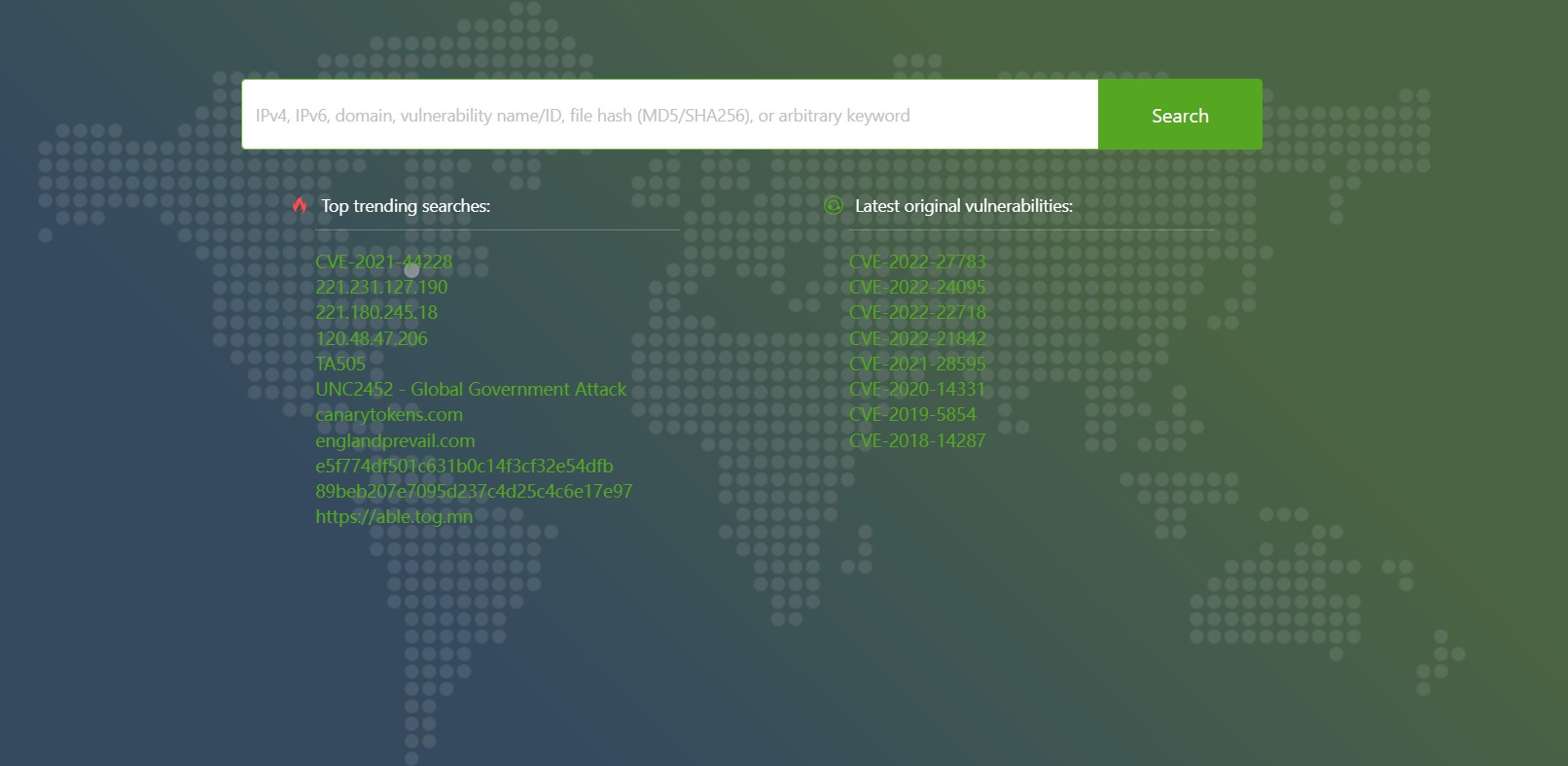
SANTA CLARA, Calif., June 26, 2024 — At the 16th Information Security Forum and 2024 RSAC Hot Topics Seminar held on June 7, 2024, Richard Zhao, Chief Operating Officer of International Business at NSFOCUS, presented the new picture of cybersecurity in the post-cloud era with his professional insights. Key Highlights Richard’s speech focused on three […]