This chapter explores further into active botnet families detected in 2018. We concentrate on four distinct families and tools focusing our analysis on their behavior changes, sample version changes, sample variants, and average age of C&C servers, to better understand the dynamic lifecycle of botnet families throughout 2018.
4.1 Gafgyt: The Choice for IoT Botnets
In August 2014, Sony PlayStation Network (PSN) suffered a massive outage caused by a DDoS attack launched from a legion of IoT devices. The hacker organization, Lizard Squad, claimed responsibility for the attack.
In December 2014, Lizard Squad again used a large number of IoT devices to launch a DDoS attack against Microsoft’s Xbox Live, disconnecting millions of game players from game servers.
In January 2015, the source code of the botnet Gafgyt used by Lizard Squad, was leaked. Analysis showed that the source code was written in C and with 1600 lines of code (including a telnet scanning module and a weak password dictionary).
Once in the wild, other hacking groups and threat actors around the world began to develop a myriad of variants based on this family, including Bashlite and Qbot, thus masking the originally unique traces of Lizard Squad attacks.
Despite being older than Mirai, Gafgyt is a latecomer to the cybersecurity battlefield. The first Gafgyt sample we captured exploited weak passwords in Telnet for propagation and had an additional module for exploiting a backdoor in Netis routers. Using the NSFOCUS Network Intrusion Prevention System (NIPS) massive alert log database, we began to track this family in 2017.
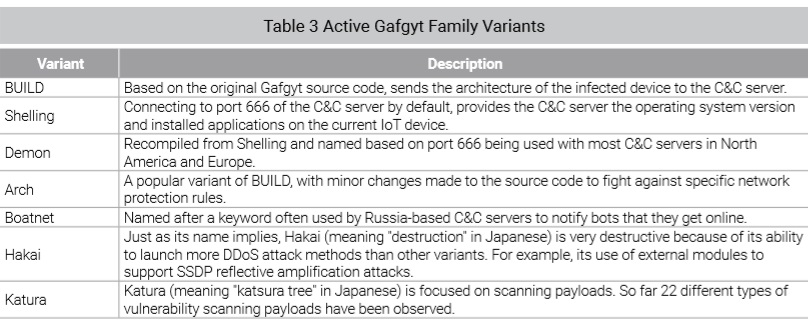
Since the time the source code was leaked, the Gafgyt family, like Mirai, has a lot of variants. The code of several major IoT botnet families overlaps, making it extremely difficult to separate these families from one another. Based on the method of communication a botnet family uses, we group several malicious programs with the same network behavior or patterns into the Gafgyt family. The following table lists active variants of the Gafgyt family.
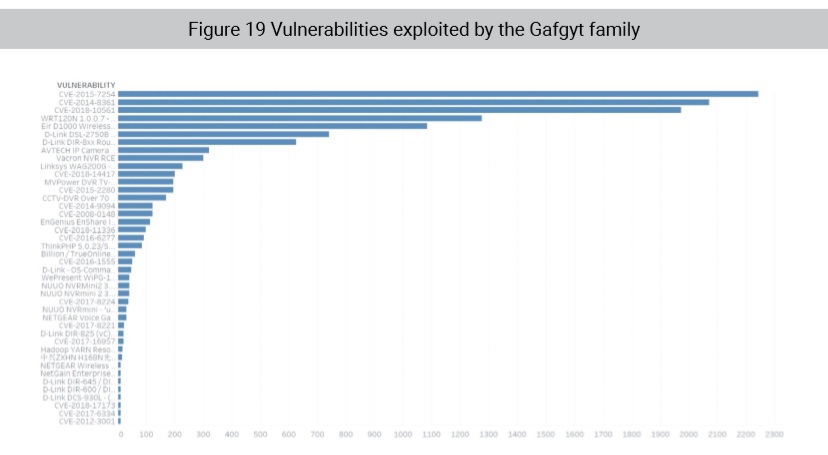
The Gafgyt family has set a record for the number of vulnerabilities it can exploit on various platforms. A total of 43 vulnerabilities can be exploited by all versions of Gafgyt, as shown in the following figure.
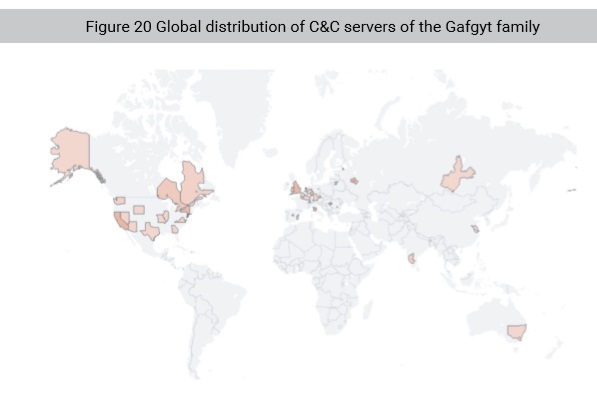
Because of their infection success rate and that their C&C servers are easy to deploy, Gafgyt botnets have propagated rapidly across the globe. The following map shows the global distribution of C&C servers belonging to the Gafgyt family and its variants that had been detected by NSFOCUS as of December 31, 2018.
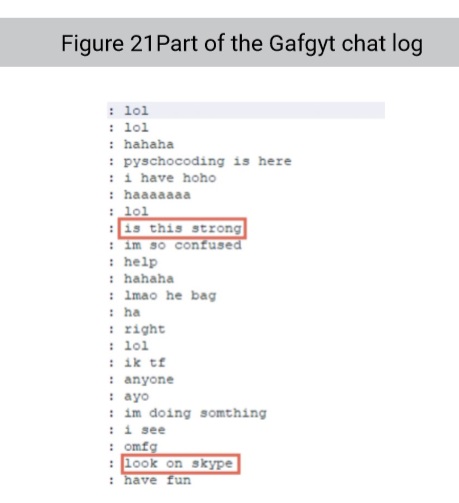
Gafgyt is the first IoT botnet successfully offered as a botnet-as-a-service, and originally offered by Lizard Squad. While tracking this family, NSFOCUS researchers found this family so successful that within Gafgyt C&C chatrooms there were people dedicated to answering questions about the use of this botnet.
For the uninitiated, it will be difficult to interpret, but what can be inferred from the above conversation is that the Gafgyt botnet has switched its business model from traditional sales of attack traffic capability to becoming a bot rental service via cloud platform. This business model further lowers the level of skills required to use the botnets and promises new avenues of attack against a broader range of targets. If this business model becomes popular, botnets will definitely become a greater threat based on upgraded capabilities while becoming ubiquitous.
To be continued.