Overview
In 2019, banking Trojans frequently launched attacks via the multilevel free technology, posing a severe threat to enterprises and public sectors. Spam was still the main propagation method. Attackers collected a great number of email addresses against which they launched phishing attacks. In 2019,
NSFOCUS Security Labs captured and tracked such banking Trojans as Emotet, TrickBot, LokiBot, Gozi, and QakBot.
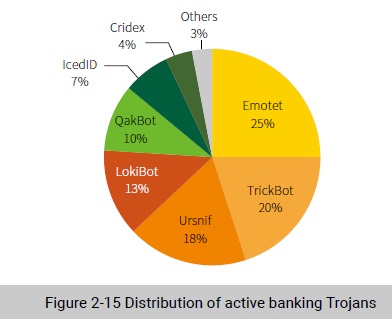
Emotet and TrickBot were the most active families, followed by Ursnif and LokiBot.
Emotet & Trickbot
In 2019, Emotet had hit industries such as hospitality, education, finance, transportation, and medical sectors and local governments, posing an adverse impact.
C&C servers of Emotet were distributed in many countries. The USA was home to the most C&C servers (23%), followed by Argentina (12%), Mexico (8%), and Columbia (6%).
Emotet contains multiple components to steal email content and browser credentials. It also exploits weak password cracking for lateral movement by detecting shared hosts in LANs or enumerating user names. In the meanwhile, it requires port mapping be enabled on the gateway in order to allow external hosts break into the intranet to connect to zombies, using them as C&C proxies to hide attackers’ real addresses.
TrickBot mainly targets financial enterprises. TrickBot spreads mainly via spam. It is quite threatening because it exploits shared networks and EternalBlue vulnerabilities for lateral movement.
Highly modularization allows TrickBot to expand its functions flexibly. TrickBot conveniently installs various payloads, to increase uncertainties in attacks and improves its antagonism.
Triple Threats
Banking Trojans cooperate closely with ransomware increasingly. Attacks launched by multiple families put enterprise intranets at risk.
Emotet can spread TrickBot, which dispatches other malware, forming a long and complicated kill chain. In 2019, TrickBot began to dispatch Ryuk to launch a tertiary payload attack (Emotet → TrickBot → Ryuk), yielding greater proceeds to attackers.
Another tertiary payload attack chain in 2019 was Emotet → Nymaim → Nozelesn. By comparing the two tertiary payload attack chains, we found that ransomware is always at the end of the kill chain, indicating that ransomware families resort to banking Trojans to obtain the required data.
These increasing close cooperation between banking Trojans and ransomware indicates that cybercriminals are cudgeling their brains to milk victims dry.
To be continued.
