Overview of DDoS Attacks in 2019
According to the observation of NSFOCUS Security Labs, DDoS botnets in 2019, though with some changes, continued with the same patterns in attack targets, families, and operating platforms overall.
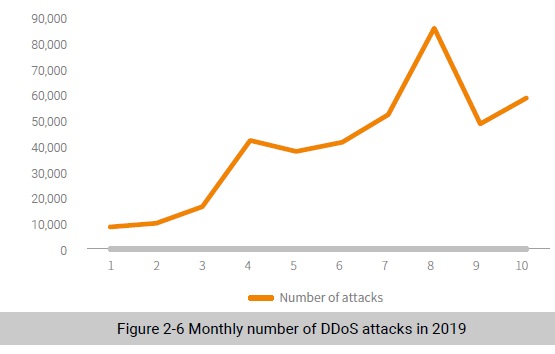
Among the track data of NSFOCUS Security Labs in 2019, there were more than 1.1 million instructions given by DDoS botnet families, 63% of which (over 700,000) were effective ones. According to the Labs’ metrics, these DDoS instructions resulted in over 400,000 attack events.
In terms of geographic locations, the USA was still the most targeted country, followed by China, the UK, and Australia.
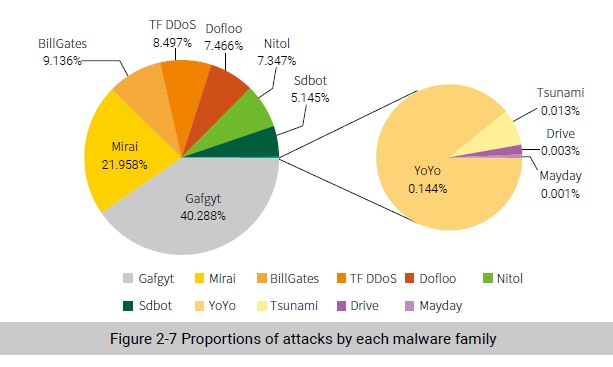
In terms of botnet families, the number of active families dropped to seven in 2019, indicating that network resources tend to be controlled by a limited number of powerful families.
When it comes to operating platforms, Linux/IoT-based families were found to contribute 60% of command and control (C&C) servers and were responsible for 60% of attacks, further distancing themselves from families on Windows. Of all families, Gafgyt overtook BillGates and Dofloo to launch
40% of attacks, running neck and neck with Mirai.
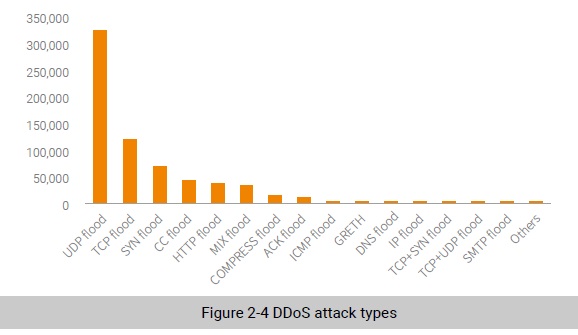
As for attack types, the UDP flood took up 55% of DDoS attacks, establishing itself as the dominant type of DDoS attacks.
DDoS Attack Patterns
From the perspective of a DDoS attack duration:
- About 91.4% of attacks lasted no more than one hour.
- About 7.1% of attacks lasted one to six hours.
- About 1.5% of attacks lasted more than six hours.
Among the first type of attacks (< 1 hour), 25% lasted 50 to 60 minutes and the remainder lasted for varying lengths of time. The attack duration varied irregularly, indirectly revealing a trend towards botnet as a service (BaaS), which means that a botnet user, after spending money on a leased service, can specify parameters at his or her discretion.
Port 80 was most frequently attacked. Besides, ports 443, 3074 (Xbox), 53, and 10011 were also attractive to attackers. These ports are for web services and online games.
The parameter of DDoS attack type tells a lot about the attack method an attacker tends to use, informing defenders from the offensive perspective how to enhance protections. The UDP flood, TCP flood, and SYN flood were still the dominant types of DDoS attacks.
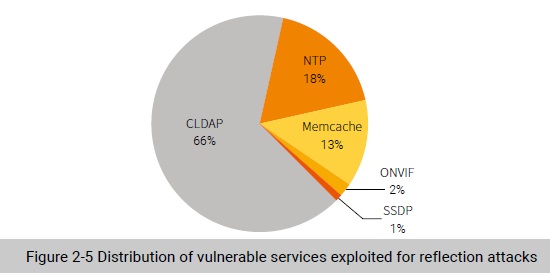
Reflection DDoS attacks took a good part of UDP flood attacks. Besides those initiated by DDoS botnet families, NSFOCUS Security Labs found over 1.1 million reflection attacks achieved by exploiting such vulnerable services as Memcache, CLDAP, Open Network Video Interface Forum (ONVIF), Network Time Protocol (NTP), and Simple Service Discovery Protocol (SSDP).
The USA was the biggest target, seeing 53% of such attacks, followed by the Netherlands (16%) and China (8%).
Among vulnerable services exploited for reflection attacks, CLDAP took the lead, found in 66% of reflection attacks. NTP came in second at 18%, followed by Memcache, ONVIF, and SSDP.
Characteristics of Attack Targets
In 2019, DDoS botnet families monitored by NSFOCUS Security Labs originated attacks on over 90,000 targets at home and abroad. Taking into account the family name (including related variants), attack target, and attack time, we identified over 400,000 attack events, or over 38,800 events a month.
The USA was still the biggest target, receiving 55% of DDoS attacks. China came in second, followed by the UK, the Netherlands, Australia, and Canada.
A look into owners of victim hosts found that hosting service providers like cloud platforms and virtual private servers (VPSs) were most severely hit, suffering 46% of attacks.
According to statistics about attacked cloud platforms, Microsoft Azure hosted 55% of victim hosts, many of which provided the Xbox game service. Over 90% of such attacks to Microsoft Azure were initiated by Gafgyt, 8% by Mirai, and the remainder by BillGates, Nitol, Tianfa, and others.
Platform Characteristics
According to statistics, DDoS attacks against Linux/IoT platforms, with a percentage of 87%, outnumbered those targeting the Windows platform.
Since variants from Gafgyt and Mirai families have seen an explosive growth, the proportion of attacks launched by IoT malware families reached a new high. Statistics show that the two families (including
their variants) contributed more than 60% of attack events.
Long-established families, Nitol and Sdbot, are still active on Windows platforms.
Attacks against Linux/IoT platforms made up a dominant portion of all attacks, involving C&C servers far outstripping those targeting the Windows platform. According to the data obtained from the tracking system of NSFOCUS Security Labs, the C&C servers of Gafgyt variants exceeded 1000 in 2019. This explains why there were a huge quantity of attacks against the Linux/IoT platforms.
In 2019, NSFOCUS Security Labs detected and tracked a total of over 5800 C&C servers of DDoS families and found that the monthly number of active C&C servers remained stable, with the peak figure standing at around 700 each month.
Most C&C servers are deployed in the USA, accounting for 43%, followed by Holland (13%). There is no obvious difference in the number of C&C servers found in China, Germany, and the UK.
Over 90% of C&C servers are deployed on the cloud or VPS servers, up from 79% in 2018. This is mainly because public cloud platforms, thanks to their low cost, ease of use, and controllable bandwidth, are increasingly favored by cybercriminals.
Summary
Nowadays, more and more small and medium-sized enterprises and individuals choose to host their servers on the cloud or VPS platform. However, such hosting service also diverts DDoS attack traffic to cloud/VPS platforms, putting these platforms to more and more tests.
To be continued.
