Overview
Overall, malware on mobile platforms, though evolving in the same way as those on PC, has a complex composition.
In 2019, ad apps still dominated the list of malware threatening the security of Android users. Potentially dangerous software involving sensitive operations also made up a large proportion. Agent programs launching attacks via remote code execution, thanks to the inherent nature of Android, were another type of mobile threats at the top of the list. In addition, it becomes quite common to use dropper or downloader to drop malicious payloads, but the scale is yet to be as large as those released by PCs. High-risk threats, such as spyware, banking Trojans, and ransomware, were small in number, but most of them had been around for some time and some even for years.
Adware
In 2019, Android adware could be classified into the following types from the aspect of the delivery method:
Bundled adware. When developing such adware, the writer decompresses a popular, legitimate app and then adds an advertisement module to it before compressing and uploading the tampered package to third-party app markets.
Disguised adware. Adware has an icon and name looking identical or similar to a popular app and is available on third-party app markets.
Adware in the form of the software development kit (SDK). Some adware developers have acquired the legal status and do business by pushing their own adware in the form of SDKs to partners. Applications using these SDKs will be included in the advertisement push network to show advertisements, thus garnering profits.
Though different in the delivery method, all these types of adware could cause bad experience to Android users.
Banking Trojans & Ransomware
By analyzing malware against banks, we found that banking Trojans such as Wroba, SvPeng, and Asacub were quite rampant in 2019.
Svpeng is a banking trojan mainly targeting Russian users. Usually disguised as an application like Flash Player or a popular game, the trojan is distributed via application markets. It is mainly used for espionage purposes, including collecting SMS, call, and keystroke records of devices, sending text messages, and obtaining administrative privileges to gain persistence. In addition, with a forged credit card page, the malware can collect users’ credit card information.
while collecting user information, some variants of the banking trojan Svpeng come with the ransomware feature, which is achieved by locking users’ screens, the oldest practice of Android ransomware. These variants had the most samples detected in 2019 among all ransomware families.
Disguising itself as an application offering adult content, such a variant uses a high-privileged window to freeze the screen and disable all buttons except the power button. Besides, it accuses users of viewing illegal content on their smartphones and uses it as an excuse to demand users to pay ransom.
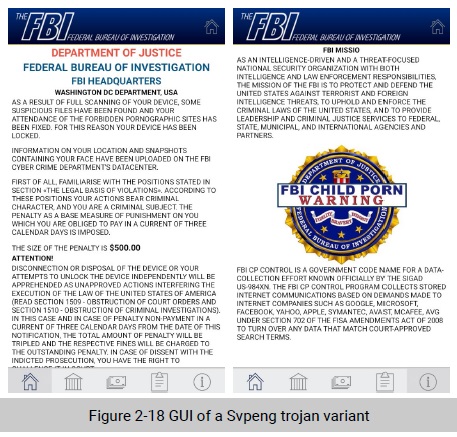
As seen from blackmail contents, Svpeng ransomware variants mainly target Android phone users in the USA.
Android-based ransomware has existed for a long time in China. These programs are popular among cyber criminals in an attempt to make quick money by charging membership dues and selling selfdeveloped ransomware. These developers independently write their own programs, resulting in large quantities and varieties of ransomware families targeting Chinese users.
Fortunately, ransomware families are less original in their delivery method. Android users can walk around them as long as they avoid downloading applications from unofficial channels.
Cryptojacking Malware
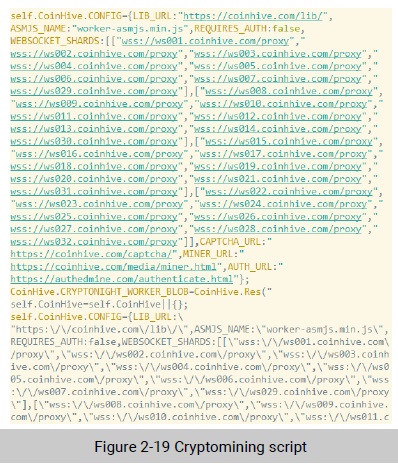
Some Android applications, upon startup, will execute JavaScript cryptomining scripts bundled with them. Most commonly, such malicious scripts execute to run coinhive’s (coinhive.com) cryptomining module which mines Monero.
The following is a cryptomining script discovered in a streaming application for a TV box:
Some applications invoke their built-in shared objects (SOs) to carry out cryptomining activities. Compared with JavaScript scripts, SOs are characterized by more efficient cryptomining and larger file sizes. The latter characteristic makes it difficult to spread SOs by means of bundling. Common SO cryptomining modules include NeoNeonMiner and MinerGate, built on mainstream architectures such as x86/x64, ARM, and MIPS.
Conclusion
In 2019, active malware on mobile platforms was largely from veteran families and mainly distributed via third-party markets and illegitimate links. Although this type of malware, as a whole, made not much headway technically, banking Trojans and ransomware became more skilled in social engineering and could launch attacks by means of highly deceptive content. When it comes to the gray industry, 2019 saw more and more applications bundled with malicious functions or modules intentionally by developers or stealthily by evil-minded people.
To be continued.
