4.2.2 AnalysisÂ
During the first quarter of 2018 when BillGates was extremely active, the family was found to attack 3962 targets, most of which were in two Central American countries. The following map shows the distribution of BillGates targets in China that NSFOCUS was able to directly monitor.
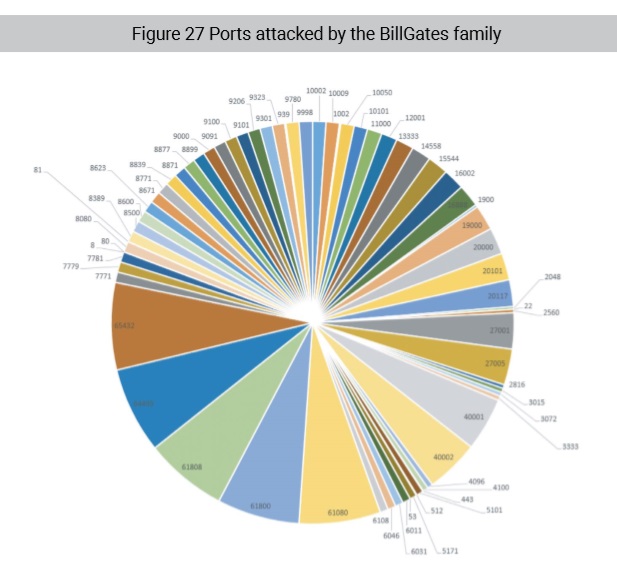
BillGates ignored common ports, such as 22, 23, 80, 8080, and 443, and instead attacked uncommon ports as its targets. These uncommon ports are not usually bound to known protocols but are used to provide agent and gaming services. This leads us to believe that BillGates is focused on agent tools, online gaming servers, and proprietary gaming servers.
The following figure shows ports attacked by the family.
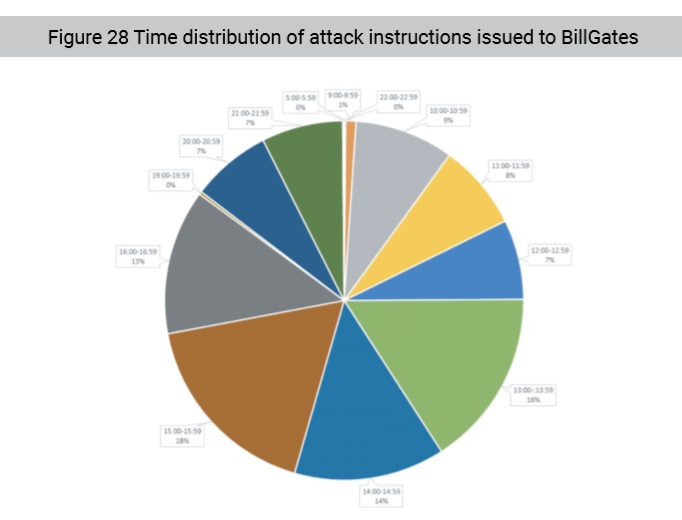
The following figure shows that BillGates received attack instructions almost around the clock. In our opinion, the even time distribution suggests that this botnet family is highly automated and likely being used as some form of botnet-as-a-service. Thus, the BillGates family may be deployed in a very efficient environment operated by a well-organized group.
Interestingly, BillGates became inert after members of another active hacking group, Shadow (Anying in Mandarin) DDoS group, were arrested. It is not known whether the two groups were directly linked or BillGates’ controllers decided to shut down operations after the high-profile arrest. However, the rise and fall of BillGates is a good view into the lifecycle of botnet development and provides good examples of attack event traceback and behavior analysis.
To be continued.