The French Computer Emergency Response Team (CERT-FR) warned that [1] an attacker exploited a two-year-old remote code execution vulnerability in VMware ESXi server to deploy new ESXiArgs ransomware. The security vulnerability number is CVE-2021-21974 [2] and it is caused by a heap overflow vulnerability in the OpenSLP service. Unauthenticated attackers...
Blog
Fortinet Multiple Product Security Vulnerability Alerts
Overview Recently, NSFOCUS CERT found that Fortinet officially released a security notice, which fixed multiple Fortinet product vulnerabilities. The key vulnerabilities are as follows: FortiNAC keyUpload remote code execution vulnerability (CVE-2022-39952): Due to a flaw in the keyUpload script of FortNAC, an unauthenticated attacker can execute arbitrary code on the...
Microsoft’s February security update for multiple high-risk product vulnerabilities
Overview On February 15, NSFOCUS CERT monitored that Microsoft had released a security update patch for February, which fixed 75 security issues, involving widely-used products such as Microsoft Exchange Server, Microsoft Word, Windows Graphics Component, Microsoft Publisher, etc., including high-risk vulnerability types such as privilege enhancement and remote code execution....
Key Technologies for Software Supply Chain Security—Techniques for Generating and Using the List of Software Compositions (Part 2)
Key Technologies for Software Supply Chain Security—Techniques for Generating and Using the List of Software Compositions (Part 1) Analysis Tools of List of Software Compositions According to the classification by the LINUX Foundation [1], SBOM tools are grouped into three categories, namely, to produce, consume and transform. Each category has...
Introduction to NSFOCUS WAF REST API
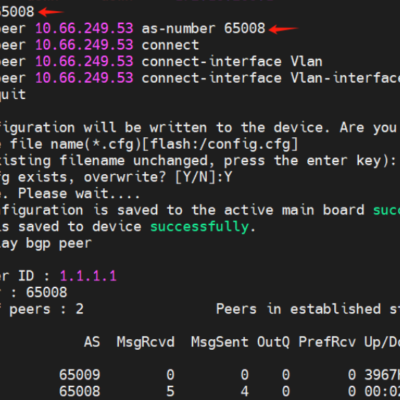
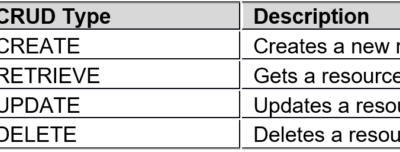
WAF REST API is known as the secondary development interface, and can be called by third-party platforms/software for adding, deleting, modifying, and querying WAF as wells its site, policy, and other configurations. Basic Conventions Format conventions: WAF REST API requests and responses are in JSON format: The attribute (primary key)...
Key Technologies for Software Supply Chain Security—Techniques for Generating and Using the List of Software Compositions (Part 1)
The list of software compositions and the software bill of materials (SBOM) are different in the requirements for the granularity of the "minimum elements" of the software, without a substantial difference in technical ideas and implementation steps. Considering the relatively mature SBOM generation tools and techniques, this document focuses on...