No complexo mundo da cibersegurança, a detecção e resposta estendidas, que também pode ser chamada de XDR, emergem como uma solução eficaz. Continue a leitura para entender o que é, como funciona e por que as empresas estão recorrendo a essa abordagem inovadora para proteger suas operações contra ameaças digitais....
Blog
Interpretation of Guidelines for Secure AI System Development
Introduction On November 26, 2023, the Guidelines for secure AI system development was jointly released by the UK National Cyber Security Centre (NCSC), the US Cybersecurity and Infrastructure Security Agency (CISA), in collaboration with the US National Security Agency (NSA), the Federal Bureau of Investigation (FBI), and the cybersecurity and...
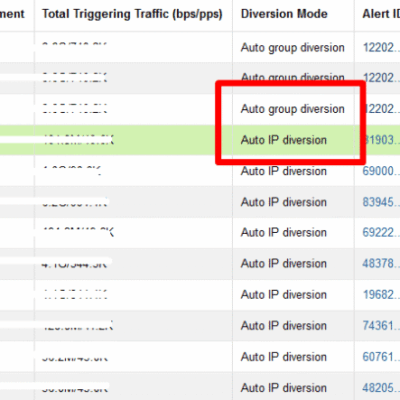
Differences between NTA Auto IP Diversion and Auto Group Diversion
You may have seen that there are two diversion modes in NTA alerts. They are Auto IP diversion and Auto group diversion. The Auto group diversion is triggered by the Region/IP Group Traffic Alert (at step 3 when configuring Regions or IP Groups). The Auto IP diversion is triggered by...
The Imperative for Zero Trust in a Cloud-Native Environment
What is Zero Trust Security? Zero-trust security is not a specific technology or product, but a security model based on the concept that "All entities are untrusted". Forrester defines zero trust as “Zero Trust is an information security model that denies access to applications and data by default. Threat prevention...
CDIC 2023
CDIC, Nov 29-30, 2023, BITEC Bangna, Thailand. The CDIC conference & exhibition was held with the theme of “Powering Techno-Drive in Digi-Hype Behaviour towards Digital Trustâ€. NSFOCUS participated this pivotal event as Gold Sponsor in APAC to introduce our latest effective continuous threat exposure management (CTEM) program and XDR-powered threat analysis and...
Prepare, Prevent, and Response: A Comprehensive Ransomware Protection Guide
Rampant Ransomware Attacks On November 8, 2023, U.S. Eastern Time, ICBC Financial Services (FS), the U.S. arm of China's largest bank, fell victim to a ransomware attack, disrupting certain systems. Reports indicate that the attack, linked to a Citrix vulnerability known as "CitrixBleed," was orchestrated by the LockBit group. ICBC...