Overview
NSFOCUS Security Labs detected a string of related phishing attacks recently. The analysis confirmed that these activities were staged by the APT group Evilnum and they were a continuation of the group’s recent operation DarkCasino.
This round of cyberattacks occurred in late July and lasted until early August. Evilnum attackers maintained consistent attack methodology and tools during the campaign. They continued to employ decoy files of PIF type and compressed type, design attack chains based on the self-developed DarkMe trojan, and use various third-party tools. DarkCasino was an APT operation observed by NSFOCUS Security Labs, mainly aimed at western European countries in the Mediterranean region and targeting cash flows in online transactions. For more information, refer to Operation DarkCasino: In-depth Analysis of Attacks by APT Group Evilnum.
About APT Group Evilnum
Evilnum is a financially motivated threat group that has been active in the UK and Europe since 2018. The group mainly targeted online trading platforms by stealing transaction credentials for the cash in the accounts of both parties.
The group is named after a trojan called Evilnum, whose alias is DeathStalker.
Its typical attack method is to disguise malicious programs as customer identification documents, trick trading platform employees into running these programs, and then steal valuable information on victim hosts by implanting spy trojans.
Evilnum has strong development capabilities and can design complex attack flows and components. NSFOCUS Security Labs had ever observed and disclosed multiple attack flows that were launched by the group with a high completion rate and various self-developed trojans.
Attack Targets
Evilnum attackers still targeted online transactions in this campaign.
The name of decoy documents captured by NSFOCUS Security Labs revealed the attack tendency.
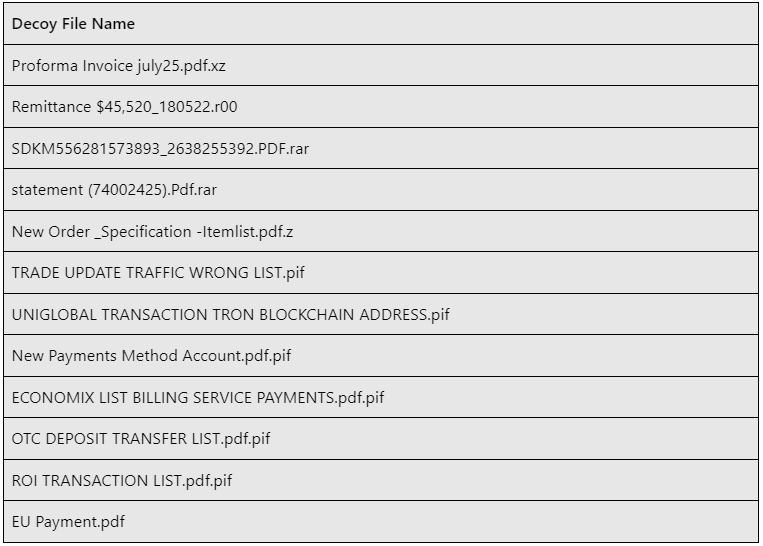
Table 1 Decoy file names
These lures were disguised as common transaction documents such as bills, lists, and invoices to attack operations staff. Part of the keywords indicated that the targets could collect cryptocurrency payments.
These characteristics are similar to those in previous operations of the Evilnum group. The group usually uses such lures to attack online transaction systems, aiming to steal money from the accounts of both transaction parties. Targeted industries include online banking, Internet finance, cryptocurrency platform, online entertainment, and others.
Attack Flows
The typical attack flow used in this campaign was similar to attack flow B in Operation DarkCasino, with some adjustments.
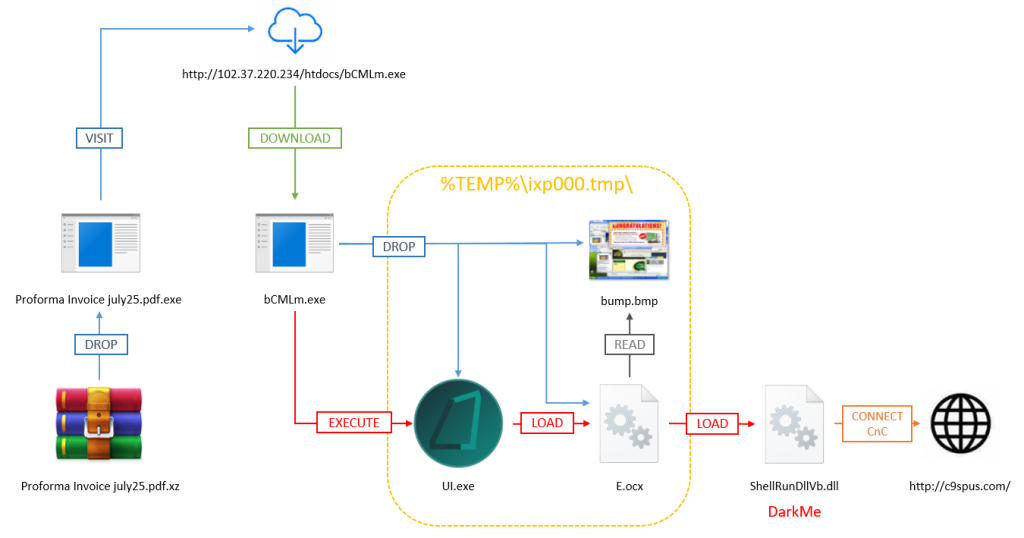
Figure 1. Attack flow A
Attack flow A shown in the above figure was used in the campaign in late July. A downloader trojan with double extensions was packaged in a compressed file and delivered to the victim, tricking the victim into running the trojan. Then the next-stage trojan bCMLm.exe placed in http[:]//102.37.220[.]234/htdocs/ was downloaded.
bCMLm.exe was a dropper trojan, and it dropped three built-in files to the %TEMP% system directory and executed the UI.exe file.
After lddAw.exe was executed, the E.ocx library file was loaded to read hidden data in the bump.bmp steganographic image file. The hidden data was the ShellRunDllVb.dll file that was loaded and executed by E.ocx.
ShellRunDllVb.dll is a DarkMe trojan that was frequently used by the Evilnum group, and it can execute file operations and CMD commands. ShellRunDllVb.dll communicated with the C&C server c9spus[.]com:333.
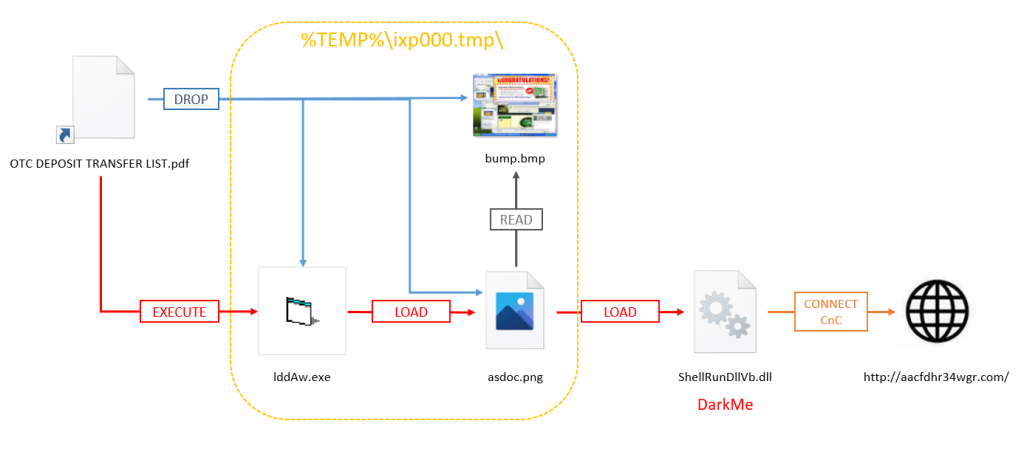
In early August, Evilnum attackers adjusted the attack flow by simplifying the download part of remote files and delivering a dropper trojan as a shortcut file.
Figure 2. Attack flow B
In attack flow B shown in the above figure, the initial stage payload was disguised as a PIF shortcut. Its double extensions misled victims into viewing it as a PDF file. The payload was a dropper trojan. It dropped three built-in files in the %TEMP% system directory and then executed the lddAw.exe file. The subsequent process was almost the same as that used in late July.
In addition, Evilnum attackers used large numbers of third-party trojans such as AgentTesla and FormBook, which were delivered in a way similar to attack flow B. These third-party trojans have powerful data theft ability and can help attackers steal more valuable information like credentials.
Conclusion
This round of attack activities demonstrates that the Evilnum group is vigorous and has a clear division of labor. Evilnum developers constantly iterate attack tools to enhance performance and confrontation abilities. Evilnum attackers keep trying different methods to deliver trojans and rapidly adjusting the execution for better attack results. As Evilnum continues to expand its targeting scope, ordinary users who conduct online transactions should be vigilant of such attacks to prevent personal information leakage and resulting property damage.
Indicators of Compromise (IoCs)
74329f3585df9b4ac4a0bc4476369dc08975201d7fc326d2b0f7b7a4c1eab22b
15f3d7a366a7101d8be528683a223aa6831f2697d118f72c2de85f7467d1cd89
21269d54395a1c7949c5919819b8533bfc2508318ec625ec8ee57654a39b698e
22548aaf2ca74dabb3fe50b274c08a71e72a31ecc79f53416007f7332d2ce19e
25605ccb0d3bf15f9e496dcc4d5a035a432a0226828cbb49230208bb5873c935
4d6da7db85da305cca557c4e3e3e909f0e7e706f68592845dfee0ee7e220d11f
6d5a01dedfcea8fed1d6df29d4c72a592176bc9214fe1cfd8aadcc2a6a21c31b
7005e6d9b81a8392bef6e6667f49adf342d4bcfff339d1337b5caf620061959a
818f1f455b20d34ff17bf88cac0f4d02f5aaad46af2d7a0e81459793931fb20a
85bb47acf3e9e3bd5d677eda5e9383a80bf7d9e424113f1b4d6f2cef7c7476af
c3ca57ce8c9b2804038525ac16b4e73af857a6b9eede7ef06d3c836bdeec0973
d787b403e7447e1851336a2655a1c8f911c302ccdc5bc63cfc8bfac1e1d4f77c
ef2c54b2ebfcd6daa2c9a96e15f206ab07b62a5c4ab2244ee70ae18f3aba7dff
1dd764b819ac194712c5269c886b71883a3182b1e488a69f9cf032fbcb258076
d1ab76d6fb30e774089214c14319c10273a6361da9890ec5cb0c6b19a231a0d0
258fde5161a07b89ff33142fb57a2fe176f7e0ea58f46acf9d7c6cf834f83731
015b823d7a91f30d1a2ad1ffad9cf5b62a3191181d4c8c1631716014eb2ad51f
05ad34f00a06df222f2a8179bddf6a55367d498763cbe65be341bcc6a7e28415
09d8451dc6facfe27b63b3daf89f47d9f70820a87a68bd630188958b40edf928
0c743bec2ded9ea3b10f973288cfe0f410ef680d89e52bd14d1073c385fc92b4
0cb3a4e2a6e1767356066266c709da67605096daa7a6dd9d7d58cf94606726c3
0cff04be7f720460b2915fc0e21f13de7fb0d918731c526c3407503f96a3c76d
0f236ff44394b314a8981b03c6b6ca8c57c901476a4146f7dd1a1efd81b2a1e8
1040403a9928dafe952ee43667cb725d3d9e26e73c6083dc5ed2cda437b4bf5e
107f75a8523a90c34426d144c6631d51f9406280ff117ef4fc1ec25afc97bf29
116ab974ec6c1db53b7d8254ca564e55b94d1597290c979892b034b29bb09898
11928d2b9537fe5f9eaad05aaf1ebf4adf93ed68417e9ca60081ecb061ef74c7
14d62b9dd87150bad3eafda51b5c2bd4639bd1e830fcde6254e4fe72a81b6a46
15c4fcf8498ad3f9b06af006d1e5f672b387ef57de435b3a9389089565851a17
1e1b9a014fb18c544e5f451171cd228e416e9d2ade1b2cf9ed90f7606a0b18e0
2d0307e4156c1e31ceb006e8f5d6c76e3b18899d15682697a3ba3dd49a759ab7
2f4077171ac081126a98982e2fe84bca197b6f9d56627f2904a6de48557af244
3a3d40045c5f673d5914b2e057e69d5f05e3fe15da282bc0687f43dccace7f08
db482bcdfac9d5b1201cd4576f1cf6885dd93b783c4f7f6150666a2f142dd8dc
5eff810e68fc0cf97346c4797a04bc4bbe98069f584973e8e9f0466c2ed1af3d
088a6db1ccfe330c113ce56ac485b83f36a04e1ded3a2b5736799c03382f50be
616c3026c24426706adab5487891137a925e6d3056e190231612ff55a685d374
fd8b80db189d9ffff96d8aed16d55406fd94b72c1cad092c782342036c0b01d2
c2a3958006dd5cb31ce7c7e4e145616aa0dd6734ebe0065f1daf810d630d391c
ad98934c2116a8c1b2eb4122d5d4b7232ebc1ebf7eeefcd46762dbbae73ed7ad
3d6c67e7bdc1b12664da2709b0aea624f0a3104cbbb7fb9bbf3d671c8ccd8d3f
677601caaef09a9bd8c8c7298674e8cbd728021ad284352978881028b0720e69
355c5eb559447a7d0c1aa8ba08db12b8b252db0377429d602b9b71e1e0f97046
4b37a07624ffb4f6a132ba315f96cce2559793cf7c71204b1bbdb00e35e49c2d
caee51524d1e97152f5c6b98401c9d553fbfa976def5517aed4114cc3da58d6d
950328ed53e05d2ff7b069a4418da326898ba11a874a549660d16b30407a0f22
c6384b86f18b6a78ab0283bed6a11472e4e9d266d210be8aae9a10708433c786
c9spus[.]com
aacfdhr34wgr[.]com
http[:]//102.37.220[.]234/htdocs/