Heuristic Recon of IPv6 Addresses Based on Their Characteristics
Previously, we mentioned that IPv6 addresses, when assigned, can, for example, include random values in particular bytes or embed MAC addresses. With these facts in mind, we exercised some restrictions to narrow down the address space to be scanned.
Specifically, we employed the following approaches to conduct the recon based on data from the collection of IPv6 addresses available on Hitlist.
- Recon of low-byte addresses and addresses containing random bits in particular bytes
For low-byte IPv6 addresses, the recon method is similar to that for IPv4 addresses. Such addresses contain 0s in all bytes except the least significant byte, so it is only necessary to base the scan on this part (least significant byte).
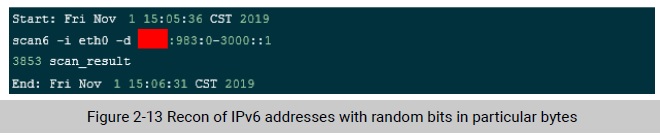
For those containing random bits in particular bytes than in the least significant byte, Scan6 uses hexadecimal notation to specify the scanning scope so as to traverse only specified bits. To do so, we ran the “scan6 -i eth0 -d ****:983:0-3000::1” command, in which 0-3000 (hexadecimal) specifies
the traversal scope. It took about 1 minute to complete a scan of 12,288 IPv6 addresses, with 3853 active ones found, as shown in Figure 2-13.
- Recon of IPv6 addresses embedding the MAC address
A MAC address consists of two parts: vendor ID in the first 24 bits uniquely assigned by the Institute of Electrical and Electronics Engineers (IEEE) and extended ID added by the vendor in the last 24 bits. The two parts constitute a universally unique 48-bit MAC address, also known as the IEEE 802 address. The 24-bit vendor ID of a vendor can be queried at IEEE’s official website. Figure 2-14 shows such a vendor ID.
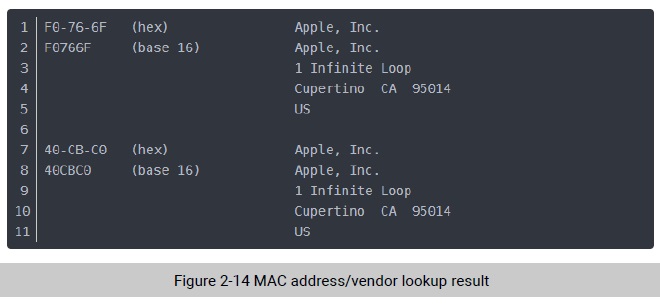
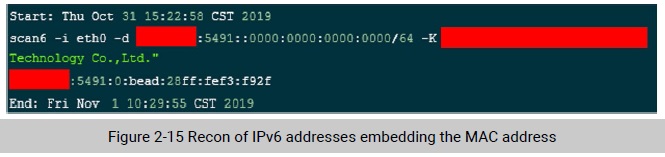
Based on the rule of generating an IPv6 address from the MAC address and the vendor ID provided by IEEE, we can reduce the scanning scope by specifying the address of the vendor within an IPv6 range, thus shortening the scanning time. Take the MAC ID “BCAD28” of a smart device vendor H. We specified a network segment that contained active IPv6 addresses embedding the MAC address and did the following test:
scan6 -i eth0 -d ::5491:0:0000:0000:0000:0000/64 -K " **** Technology Co.,Ltd."
where, -K indicates the vendor name, meaning that the scan covers only /64 IPv6 addresses embedding the vendor’s MAC address.
This testing scan took about 19 hours. Although only one active address was discovered, the method of scanning only IPv6 addresses embedding the MAC address proved to be feasible. As we had the vendor’s six-bit MAC ID and four-bit FFFE, the number of bits to be traversed lowered from 16 to 6, which, in turn, led to a decrease in the number of addresses to be scanned from 264 – 1 to 218 – 1. As a result, the recon time was significantly shortened. In addition, this recon method is conducive to discovery of IPv6 addresses of IoT devices. By typing the MAC address of a vendor of smart IoT devices, we can be returned with a list of IPv6 addresses, among which the active ones are probably associated with IoT devices. Moreover, we can extract the MAC address from such addresses and match it with the vendor, thus determining the device type of scanned assets.
To be continued.
