The following sections analyze threats from the port mapping service based on UPnP port mapping tables collected from network-wide devices.
Overview
In the 2018 Annual IoT Security Report , we focused our attention on four types of malicious port mappings that had the most distinctive characteristics and the most extensive impact. Of the four major malicious types, EternalSilence, IntraScan, and NodeDoS were mainly used for intranet intrusions, while MoniProxy acted as a proxy for access to the Internet. In 2019, we also turned our eyes to other malicious port mapping types to get a whole picture of devices infected with malicious port mappings.
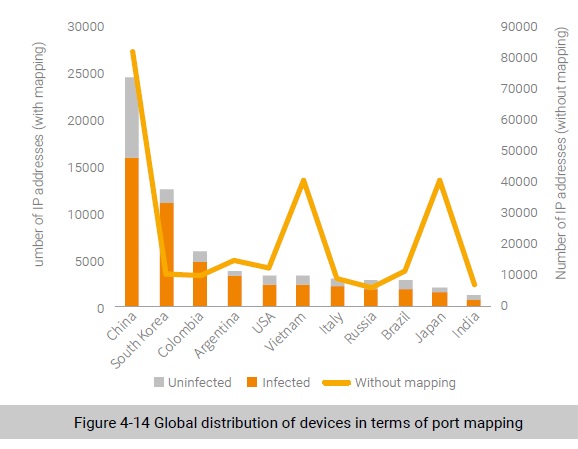
Of 390,000 devices with port mapping publicly accessible, a total of 63,000 devices were found to be affected by more than one type of malicious behavior and some suffered several kinds of intrusions. Up to 45,000 devices experienced intranet intrusions and approximately 30,000 were detected to be broken into by a malicious proxy. Figure 4-14 shows the global distribution of devices by port mapping.
It can be seen that, whether in terms of the total number of exposed port mapping services or the total number of infected devices, China took the first spot. Therefore, we believe that if more than one malicious port mapping record is found in the port mapping table of a device, the port mapping service of this device is highly likely to be used by other attackers. Our scanning data shows that there were approximately 63,000 high-risk devices infected with malicious port mapping. In view of characteristics
of port mapping, if we assume that an intranet has 20 devices on average, we can infer that about one million devices are potentially affected.
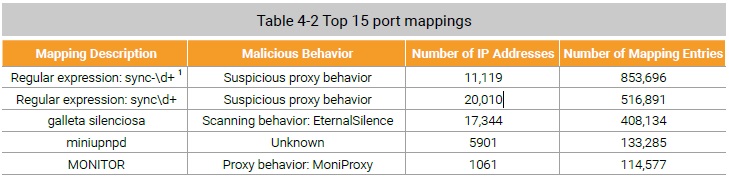
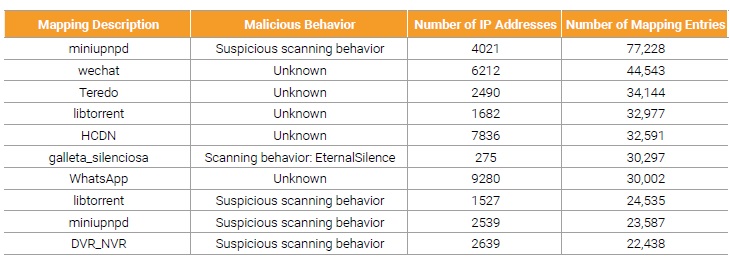
A total of approximately 3.12 million UPnP port mapping entries were detected worldwide, of which 2.4 million were malicious ones involving proxy and scanning behaviors, representing 77% of the total number. Obviously, port mapping abuse is not unusual. We found around 80,000 mapping descriptions (the description field) in port mapping tables of devices around the world. It is impossible to identify all types of applications from tons of description data. For this reason, we focused our attention on top malicious behaviors by the number of port mappings. We analyzed top 15 malicious behaviors and found that three were known ones and six were suspicious proxy detections and intranet scans, as shown in Table 4-2. Besides, we detected legitimate port mappings of some non-malicious applications, including those containing the mapping description like miniupnpd, WeChat (messaging application), libtorrent (P2P download), HCDN (streaming media application), or WhatsApp (messaging application). We dissected these mappings from dimensions such as the destination IP address, destination port, and transport protocol and determined that they were highly likely to be secure.
Here is a brief comparison with data in the previous year. We analyzed only four types of malicious port mapping that infected a total of 44,000 devices in 2018, but collected statistics from different dimensions in 2019. Therefore, it is impossible to make contrast in the distribution of the total number (for example, by country). Also, we found that four major types of malicious port mapping all infected a declining number of IP addresses in 2019: The figure was decreased from 40,000 to 17,000 for EternalSilence and from 7000 to 1000 for MoniProxy. We guess that the quantity reduction may result from two factors:
- Port mapping entries are automatically deleted once the lease time expires.
- Port mapping entries are cleared upon the device restart.
As devices could possibly have dynamic IP addresses, attackers had to scan the entire Internet from time to time to have a relatively complete list of infected devices. For those attackers that are not active enough, the list may be actually shortened over time.
Intranet Intrusion via UPnP Port Mapping
According to the design and application of the UPnP port mapping service, we believe that this service is supposed to temporarily enable public ports for foreground intranet applications. Foreground applications refer to application services that are started for use and closed by users immediately after use, including P2P downloads, VoIP communications, and online games, instead of those daemons that run persistently in the background like SSH, FTP, and HTTP services1. All behaviors, except legitimate ones, are either port mapping abuses or malicious intrusions.
As for malicious intrusion, if the destination IP address (internal_ip) falls within the private IP address range defined by RFC 1918 and the destination port number (internal_port) is smaller than 10000, this is a malicious mapping entry potentially for intranet intrusion. Such a malicious intranet intrusion behavior attempts to map IGD devices’ application services in the intranet to the external port (external_port), exposing intranet services to intrusion risks.
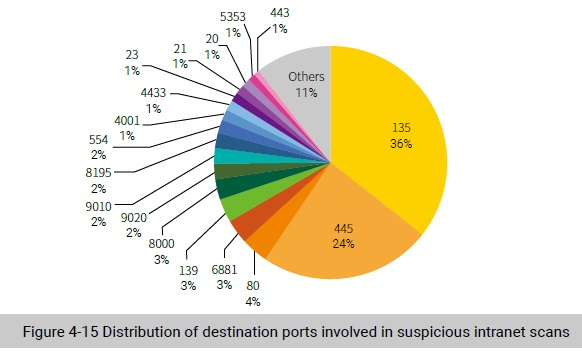
Of 86,000 IoT devices with port mapping entries exposed on the Internet, 52.3% were found to engage in malicious intranet intrusions, with destination ports 135, 445, 80, 6881, and 139 used most frequently.
We define mappings of destination ports with a number smaller than 10000 as malicious behaviors. According to the ephemeral port number range definition, a high-level port with a five-digit or greater number is an ephemeral port. Though the ephemeral port range varies slightly among standards organizations and operating systems38, from our experience, users or O&M personnel usually deploy most application services on ports with a number less than 10000.
We observed that 60% of intranet intrusions targeted ports 135 and 445 and a small portion were against common application service ports.
Malicious Proxy Behavior Based on UPnP Port Mapping
As for malicious proxy behavior, if the destination IP address (internal_ip), this is a malicious mapping entry potentially for proxy behavior. This malicious proxy behavior attempts to use a victim’s device as a springboard by mapping an external port (external_port) of the device to a certain port of a server. In this way, an attacker could send a malicious request to the server by masquerading as the victim’s device.
Of 86,000 IoT devices with port mapping entries exposed, 35.2% are found to be associated with malicious proxy behavior, including the most common ones like setting up a web proxy and sending spam via SMTP. These malicious behaviors compromise IP reputation of customers and their carriers.
A UPnP-based port mapping setup request contains three key fields: external port (external_port), destination IP address (internal_ip), and destination port (internal_port). Through this kind of port mapping, data from an external port will be forwarded to the destination port on the destination (intranet) IP address. Certain UPnP SDKs, however, do not strictly restrict the destination IP address range, allowing the devices using these UPnP SDKs to send data from an external port to another external
server. In this case, by sending a request using the IP address of a victim’s device, an attacker could evade certain restrictions to perform malicious operations like bulk account registration and sending mass spam. In the actual environment, attackers tend to use these devices to access websites (mostly Google) and SMTP on port 25. Typical examples include our newly discovered exploitation behaviors in 2019, like MiniUPnPd exploitation behaviors with the mapping description beginning with “sync”.
Some vulnerability-based attackers that perform malicious proxy behaviors have shown preference for certain types of device. For example, 91.62% of attack attempts with the mapping description starting with “sync” targeted port 49125; all requests from MoniProxy were directed to the SOAP service available on port 2048.
To be continued.
