In the 2018 Annual IoT Security Report, we analyzed threats against UPnP and you can refer to the report for basics of UPnP. In this report, we updated UPnP-related data and added new findings.
Viewpoint 6: Approximately 2.28 million IoT devices around the world had the UPnP/SSDP service (port 1900) publicly accessible and therefore were vulnerable to DDoS attacks. The year of 2019 saw a reduction of about 22% in such IoT devices, compared with last year. The UPnP port mapping service, exposed on about 390,000 IoT devices, is likely to be misused as a proxy or render intranet services accessible on the extranet.
UPnP Exposure
In 2019, we continued to conduct research on the UPnP exposure. Unless otherwise indicated, all data provided in this chapter was obtained from a single-round global survey conducted in October 2019. This section analyzes the exposure of SSDP and SOAP services. Section 4.4.2 Threats from the UPnP Port Mapping Service will provide a detailed analysis of the port mapping table of the SOAP service.
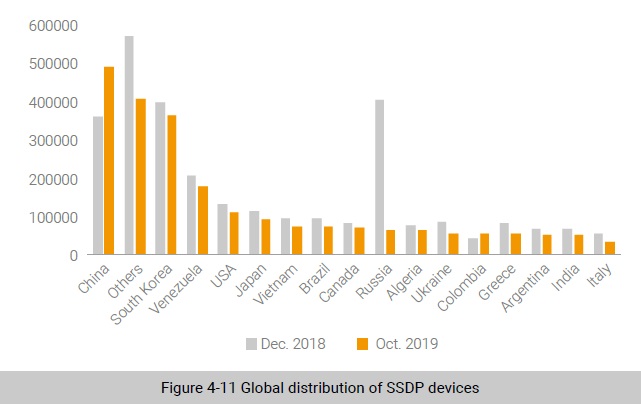
Finding 8: As for devices with the SSDP service publicly available, China, South Korea, Venezuela, the USA, and Japan had the most devices exposed. Meanwhile, we found that in Russia, 2019 saw an 84% reduction in the quantity of such exposed devices compared with the previous year. It is estimated that related authorities in Russia have pushed forward UPnP governance.
According to the global distribution of devices with the UPnP service exposed in 2019, most countries saw a reduction in the number of such devices, with Russia witnessing the sharpest decline, from 400,000 to 60,000. Currently, we have not found any related information accounting for this situation in Russia, but we have reasons to believe that related Russian authorities must have strengthened UPnP governance.
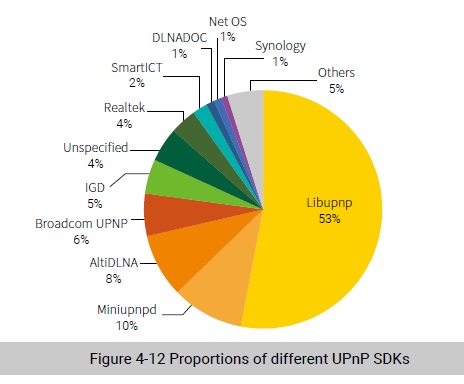
SSDP devices mostly used such UPnP SDKs as libupnp, miniupnp, AltiDLNA, Broadcom, and IGD. Of the SSDP devices, those using libupnp took up the largest proportion (53%). It should be noted that a significant increase was observed in the number of devices using AltiDLNA.
Compared with last year, two changes are observed in the distribution of UPnP SDKs:
- The number of devices with the Server field set to “IGD” decreased from about 290,000 to 100,000 and most of them had the SOAP port that was inaccessible.
- A sharp increase was observed for AltiDLNA devices. Fewer than 2000 devices were exposed in 2018, but the figure rose to nearly 200,000 in 2019. Our analysis shows that these devices are smart speakers from a Source Korean vendor and adopt the multimedia solution provided by Alticast.
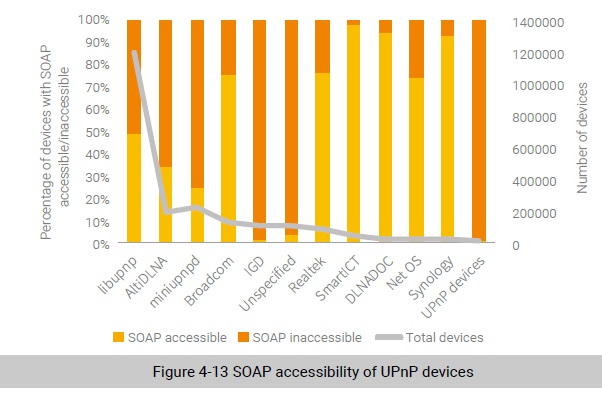
Finding 9: 46.9% of UPnP devices made the SOAP service accessible, 61% of which contained medium-risk or above vulnerabilities. Attackers could exploit these vulnerabilities to take full control of these devices or launch attacks to cause them to crash.
In the 2018 Annual IoT Security Report , we associated the existing vulnerability information with UPnP SDK versions and found that 69.8% of devices were vulnerable. This figure was decreased to 61% in 2019.
IoT devices adopt different kinds of UPnP SDKs. To analyze the SOAP accessibility, we classify these devices by SDK vendor, as shown in Figure 4-13. For devices using SDKs from the same vendor, most of them are either accessible or inaccessible via SOAP. According to our statistical analysis, libupnp is used by the largest number of devices. Many vendors choose to use it and different vendors tend to use different fixed ports for it, making its application quite complicated. For example, a camera vendor uses port 80 to provide the SOAP service, while a router vendor uses port 49152 or 49154 for most devices. In addition, many vendors choose to use the default manufacturer attribute (Linux UPnP IGD Project) in SOAP messages. For some devices, the SOAP port is not publicly accessible, and therefore we cannot determine their models and vendors.
To be continued.
