1. Overview
From data collected throughout 2019 and data as of June 30, 2020, we extracted information about malware, whose distribution by type is shown in Figure 1-1. Compared with 2019, the percentages of various types of malware in 2020 H1 changed, with backdoors overtaking crytominers to become No .1 with a percentage of 48.05%, and the percentage of cryptominers fell significantly. Meanwhile, worms’ activity level was basically flat on 2019. Cryptominers, worms, and backdoors together accounted for 87% of all malware activities.
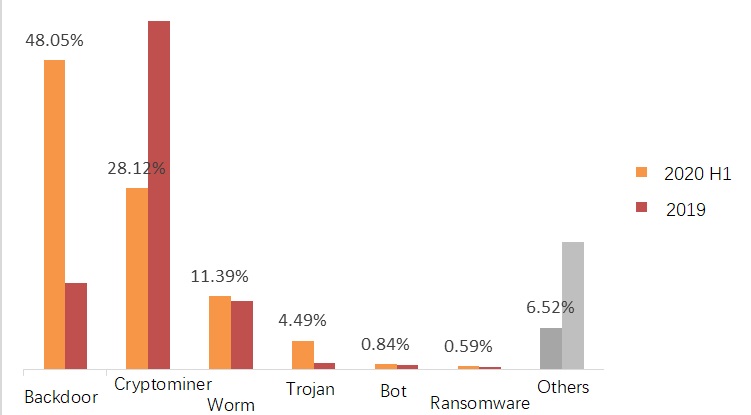
Figure 1-1 Distribution of malware types
2. Malware Trend
Backdoor
In the domain of information security, a backdoor is a method of bypassing security restrictions to gain access to an application or system. The primary purpose of backdoors is for subsequent stealthy access to or control of system. Attackers often use some deceptive means to trick users into performing some operations, such as downloading or opening a file with malicious code, thus creating a backdoor in their computers without their knowledge. Alternatively, attackers can create a backdoor on a host previously compromised by other attack methods, which allows them to easily intrude the system at any time. Such backdoors feature high elusiveness, making them difficult to detect.
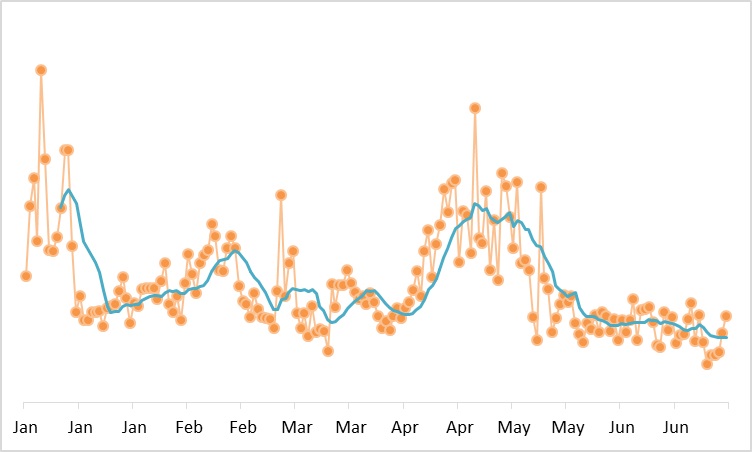
Figure 2-1 Backdoor activity in 2020 H1
Obviously, in 2020 H1, January and May saw relatively active backdoors with short durations. June witnessed stable performance of backdoors, with the lowest activity level in six months. Backdoors with a high activity level in 2020 H1 are as follows:
- Netis router backdoor
As early as 2014, Netis routers were reported to have a high-privileged backdoor. Attackers could exploit this vulnerability to obtain root privileges, thereby taking full control of affected products. Up to today, such vulnerable routers are still used in the Internet, which have been exploited by the Gafgyt botnet family.
- nssock2.dll backdoor communication
Malicious code exists in nssock2.dll released in multiple versions of Xmanager, Xshell, Xftp, Xlpd, and other NetSarang products. The backdoor could initiate requests to a DGA-generated domain name that could illegally extract data from multiple overly long domain names through Domain Name System (DNS) resolution. Besides, it collects and uploads host information to one domain name generated with a domain generation algorithm (DGA) monthly and saves configuration information returned by the server.
Cryptominer
In 2017, with the cryptocurrency price soaring and driven by profits, most traditional ransomware manipulators turned to mining cryptocurrency. Bitcoin, Monero, and Ether transactions were quite active at one time. Data on hand shows that there are 1600 cryptocurrencies, with a total value of USD 340 billion. Cryptomining is always an important method for attackers to make profits, with no decline sign in the foreseeable future.
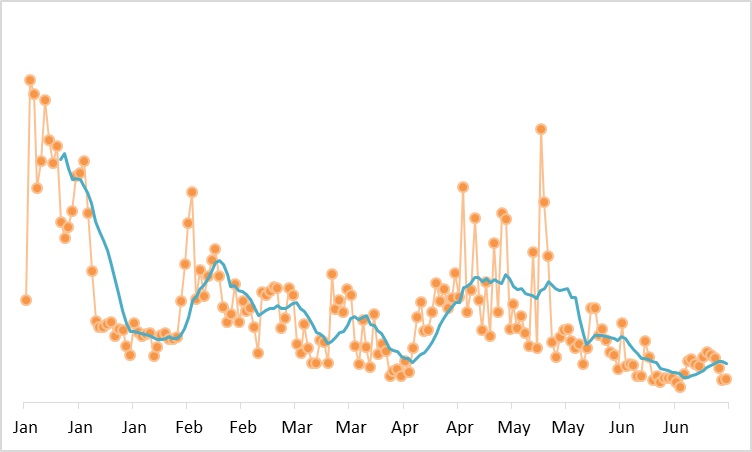
Figure 2-2 Cryptomining activity in 2020 H1
In early 2020, cryptomining was active. However, it declined continuously in whole January, and then fluctuated with different activity levels from February to June, though not comparable to the peak in early 2020. Cryptominers with a high activity level in 2020 H1 are as follows:
- Watchdogs
Watchdogs exploits hosts infected with the watchdogs virus. The virus is implanted by means of the Redis unauthorized access vulnerability and SSH weak passwords. Then, it drops a mining trojan for cryptomining, launches Redis vulnerability attacks and SSH brute-force attacks on intranet and extranet hosts, and infects more computers by scanning the intranet and extranet.
- WannaMine
Likewise, the WannaMine family also exploits the EternalBlue vulnerability and has been the main force among cryptominers since 2018, accounting for 70% of all mining activities detected in 2020 H1. It spreads at an alarming speed. The EternalBlue vulnerability is favored by most cryptomining virus families as an attack weapon.
Worm
The worm is a common computer virus. It is an independent program that can operate without the intervention of computer users. It spreads by gaining partial or full control over vulnerable computers on networks. According to long-term observations, most worm viruses were first discovered more than five years ago. This indicates how capable these viruses are of propagating and evolving and how difficult it is to remove them completely from the network.
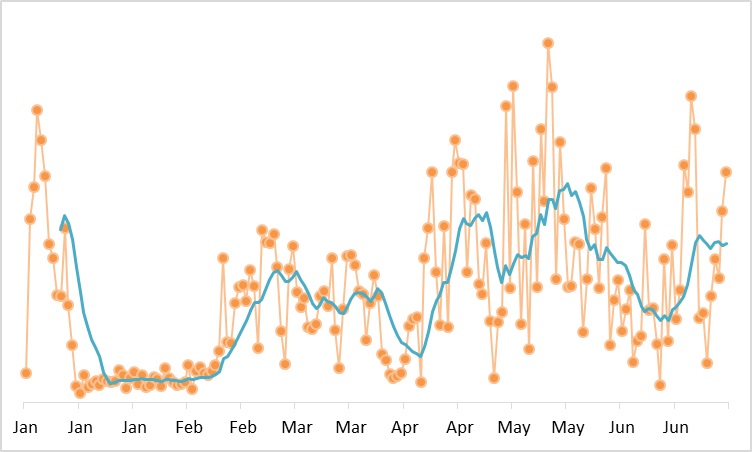
Figure 2-3 Worm activity in 2020 H1
In 2020 H1, worms changed greatly in the activity level. In February, worms were sluggish. In other months, their activity levels fluctuated and were high in May and June. Worms with a high activity level in 2020 H1 are as follows:
- W32.Faedevour
In terms of the number of events, W32.Faedevour stood out from the other viruses ranking among top 5. By opening a backdoor in an affected computer to steal information and execute remote attackers’ commands of taking screenshots, downloading files, and sending files, W32.Faedevour attempts to spread by means of a network driver and shared file folder.
- Code Red
Code Red is a network worm virus discovered on July 15, 2001. It infects computers that run the Microsoft IIS Web server. With a minor modification, the virus can become deadly. Code Red III allows hackers to obtain all privileges of the computers they have comprised and steal confidential data, thereby threatening cybersecurity.
Remote Access Trojan
The core function of trojans is information theft and other complex remote controls. Unlike common viruses, trojans are not self-propagating and do not “deliberately” infect other files. By disguising themselves, they seduce users into performing download and execution operations and open a door for attackers to enter the infected computer, who will then destroy or steal files or even remotely control the infected computer. In fact, there is no uniform standard for categorizing viruses. Trojans can also share similarities with worms. Here, we categorize trojans based on their core functions.
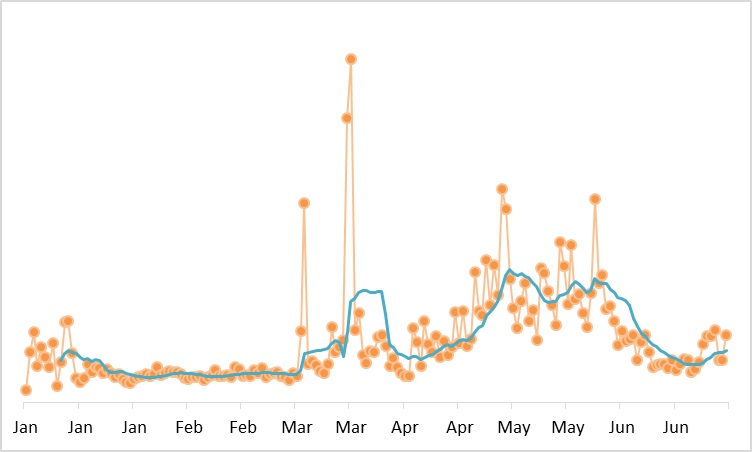
Figure 2-4 Trojan activity in 2020 H1
In 2020 H1, trojans were relatively sluggish in the first three months. March saw a short outbreak. April, May, and June witnessed a slight fluctuation and an active trend. Overall, trojans were stable. Trojans with a high activity level in 2020 H1 are as follows:
- DarkCloud
Since 2015, DarkCloud has infected millions of computers. After several updates and iterations, related variants have sprung up like mushrooms and are difficult to eradicate. Among them, Bootkit is one of the most complicated trojans ever discovered, affecting every aspect of the underground industry.
- NovaLite Remote Access Trojan
Simple but remarkable, the NovaLite Remote Access Trojan (RAT) could be immune to the defense of antivirus software and auxiliary security tools and easily sneak into users’ multilayer defense systems. It is easy to perform such powerful and practical functions. In addition, it is suitable for spreading via trojans attached to web pages due to its small size.
Ransomware
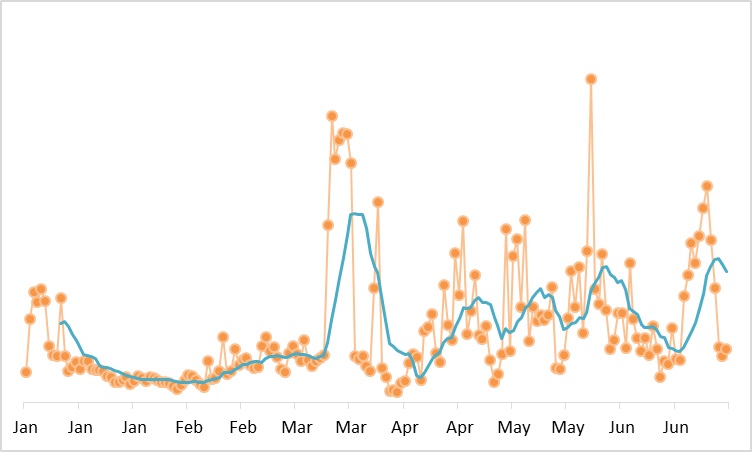
Figure 2-5 Ransomware activity in 2020 H1
In 2020 H1, ransomware was the most active at the end of March and fluctuated obviously after March. Ransomware with a high activity level are as follows:
- WannaCry
In 2017, WannaCry swept across the globe. They attacked the UK, Russia, Europe, and China within 5 hours and finally affected as many as 150 countries, causing extremely serious economic losses. Though the EternelBlue vulnerability has been known for one and a half years since May 2017, attacks exploiting this vulnerability have never failed. This should draw attention from professionals of all sectors.
- Variants of Locky ransomware
Locky first appeared in early 2016 and has evolved into many variants since then. The ransomware spread by exploiting social engineering to send lots of mails. It differs from the previous versions of Locky ransomware in that its mail attachments are WSF files, which are Windows script files and text documents with extensible markup language (XML) code. Therefore, they can be compiled on any editor that supports XML. Since windows script files are not engine-specific, they might contain the scripts of any scripting engine that is compatible with Windows scripts.
