In the process of developing code, developers will worry about whether there are security problems in the image of code, dependencies and projects packaged. In the RSAC 2023 this year, David Melamed and Luke O’Malley recommended five open source security tools in their speech “5 Open Source Security Tools All Developers Should Know About”.
When evaluating each category of security tools, the contestants of security tools under this category is listed, and the optimal security tools under this category are finally evaluated by integrating multiple factors.
When evaluating security tools, a comprehensive evaluation is mainly carried out from the following aspects:
- Result quality: accuracy of results from a development perspective
- DevX: It can be used from the command line or integrated with various IDEs, which is fast and easy to understand
- Maturity: community support, bug repair and certificate
- Customizability: Tools can be easily extended to suit developers
The recommended tools for each category are as follows:
Table 1 Recommended open source tools for each category
| Categories | Tool Name | Link |
| Code Scanners | Semgrep | https://github.com/returntocorp/semgrep Semgrep |
| Dependency Checkers | OSV-Scanner | https://github.com/google/osv-scanner |
| Infrastructure as Code Scanners | KICS | https://github.com/Checkmarx/kics |
| Container Scanning | Trivy | https://github.com/aquasecurity/trivy |
| Runtime Scanning | ZAP | https://github.com/zaproxy/zaproxy |
1. Code Scanners
Code scanning is mainly used to find vulnerabilities in the code. Typically, this includes:
- OWASP Top 10
- CWE Top 25
- Secrets
- Custom rules (e.g. authentication/authorization information, etc.)
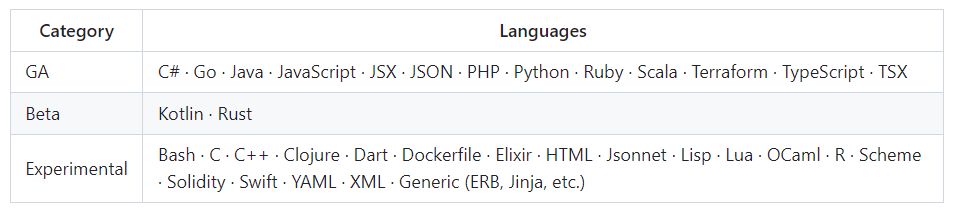
Finally, Semgrep was selected from the following contestants.
Semgrep’s rules integrate many security tools (such as Gitleaks, Findsecbugs, Gosec, etc.) and support more than 30 languages. From a usability point of view, it is compile-free and can run on any environment (command line, Docker, IDE). It’s also easy to extend, just by writing rules. Semgrep has a large community and active contributors.
As shown in the figure below, scan the code with Semgrep. The result shows that there is a line of eval($arg) code in src/test.php, which has command injection vulnerabilities:
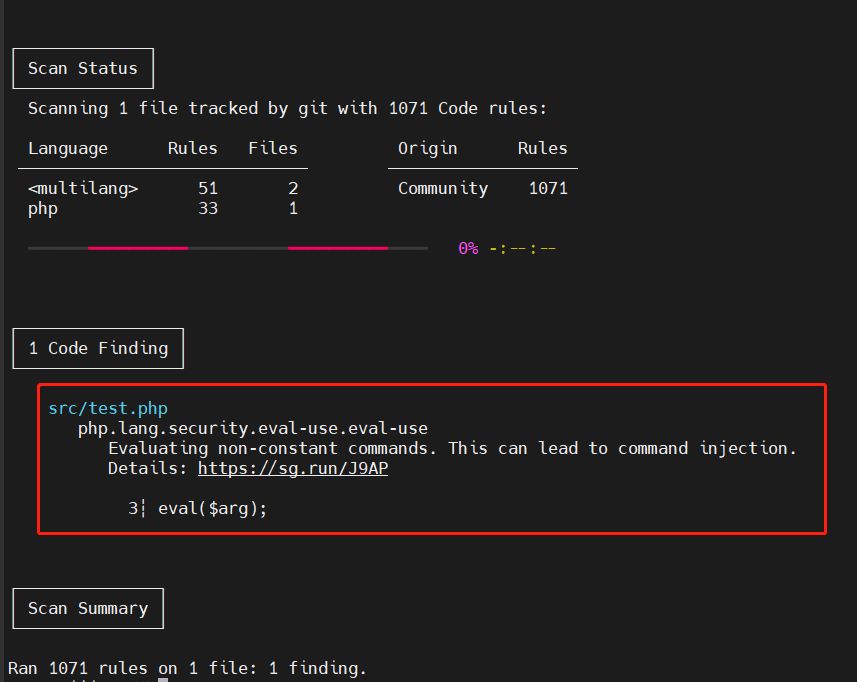
2. Dependency Checkers
Dependency checking is mainly used to find vulnerable components on which the project code depends. The main step is to first identify the open source components used by the software and then compare them with a database of known vulnerabilities to check for any publicly disclosed vulnerabilities in these dependencies. This is called SCA, or Software Composition Analysis.
Finally, OSV-Scanner was selected from the following contestants.
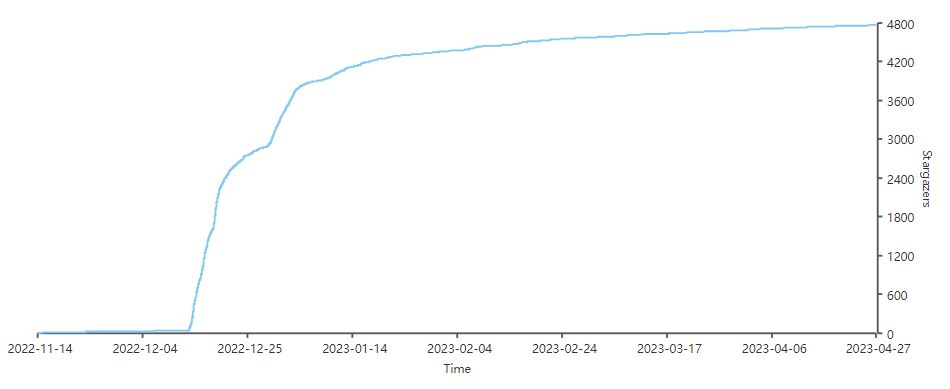
OSV-Scanner uses Google-maintained OSV database (open source vulnerability library), supports 13 languages, and can scan specified SBOM and lockfile files. OSV-Scanner is growing in popularity and community support:
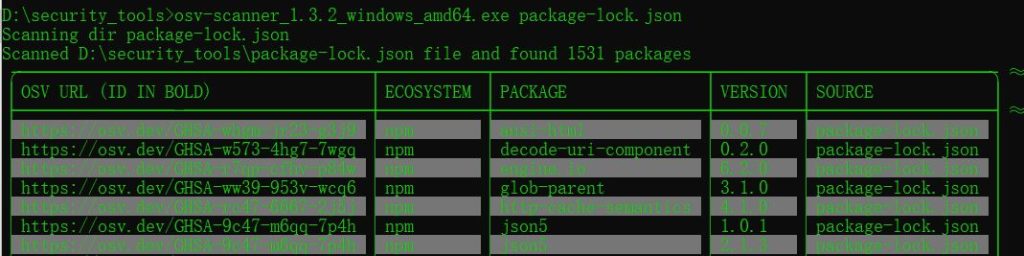
As shown in the figure below, use osv-scanner to scan npm lockfile. It scanned 1,531 software packages and found some security issues. Each question has an OSV URL (ID of the security vulnerability) to provide more information about the vulnerabilities, and also lists the package name and version number associated with each vulnerability.
3. Infrastructure as Code Scanners
Infrastructure scanning, which treats the configuration and management of infrastructure as code, is mainly to detect security configuration errors before the code is submitted to the cloud. These errors may include:
- Missing encryption
- Broad permissions
- No logging
- Default settings
Finally, KICS was selected from the following contestants.
KICS supports 18 frameworks and provides 200+ built-in remediation recipes. It can run everywhere (IDE plugin, local, CI)
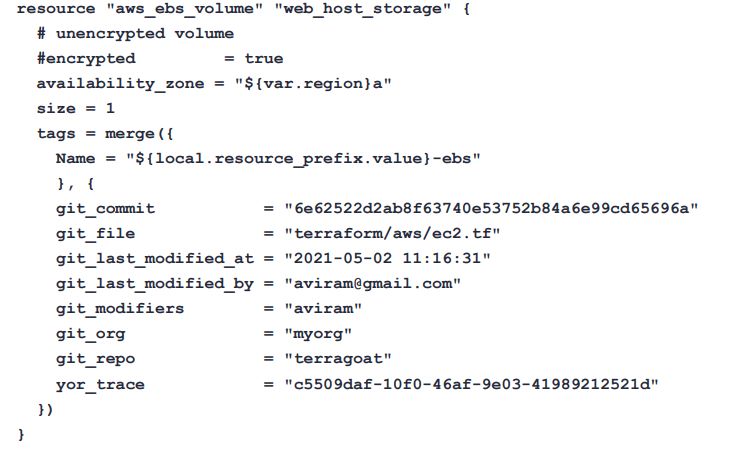
Below is an example of creating an EBS volume in Terraform:
KICS can scan two medium-risk vulnerabilities, one is undefined by IAM Access Analyzer and the other is that encryption of EBS volume is not enabled.
4. Container Scanning
The main purpose of container scanning is to detect vulnerabilities and configuration issues in container images.
Finally, Trivy was selected from the following contestants.
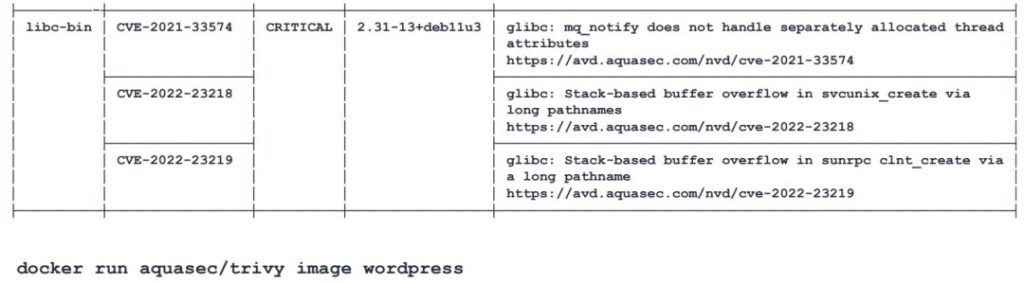
Trivy supports scanning container images, file systems, git repositories, virtual machines, etc. It can also generate SBOMs. The following figure shows the vulnerabilities discovered by Trivy scanning wordpress images. A total of 3 vulnerabilities were found, namely CVE-2021-33574, CVE-2022-23218 and CVE-2022-23219.
5. Runtime Scanning
Runtime scanning refers to discovering vulnerabilities when Web applications or APIs are running. Runtime scanning typically uses Dynamic Application Security Testing (DAST) to simulate attacks and detect vulnerabilities in applications or APIs. Finally, ZAP was selected from the following contestants.
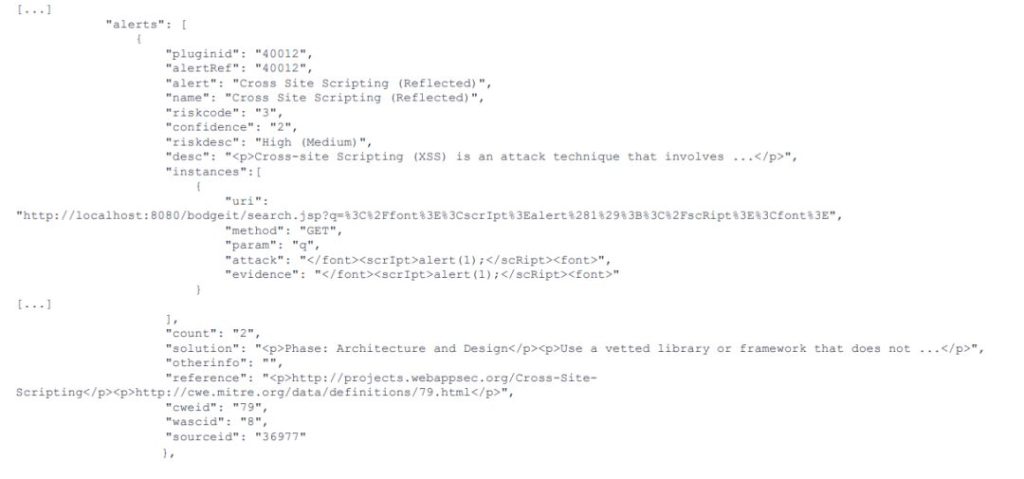
ZAP can detect OWASP Top 10 risks and also includes more than 250 curated rules. ZAP is also one of Github’s top 1,000 projects, very popular and has a large community. As shown in the figure below, ZAP has detected an XSS vulnerability and gives a description of the vulnerability, risk level and possible solutions. In addition, the output includes detailed information about vulnerabilities, such as the location of vulnerability discovery, parameters, and values of parameters that can trigger vulnerabilities. This information can help developers better understand and fix vulnerabilities. Finally, reference links are included in the output that provide more information about vulnerabilities.
Companies usually have relevant tools and process systems for code auditing and penetration testing, but these open-source security tools can also be used for self-inspection during development to find various security problems in codes, dependencies, configurations and images and fix them in time, avoiding the accumulation of security problems until they are exposed at a later stage. They can be helpful to improve the efficiency and overall security of the project. Of course, when using open source software, open source software risk monitoring should also be done well.
REFERENCE
[1] 5 Open Source Security Tools All Developers Should Know About