Vulnerability Description
On March 23, 2021, NSFOCUS detected that Adobe released a security bulletin fixing a code execution vulnerability (CVE-2021-21087). Due to improper sanitization of user inputs, unauthenticated attackers could execute arbitrary code on the target server by sending a crafted, malicious request to the ColdFusion server.
Adobe ColdFusion is a rapid application development platform. ColdFusion is often used in the development of data-driven websites and intranets. However, it can be used for remote services as well such as SOAP web services or Flash. It can also be used as a background server for Adobe Flex applications.
Reference link: https://helpx.adobe.com/security/products/coldfusion/apsb21-16.html
Scope of Impact
Affected Versions
- Adobe ColdFusion 2021 <= 2021.0.0.323925
- Adobe ColdFusion 2018 <= 2018 Update 10
- Adobe ColdFusion 2016 <= 2016 Update 16
Unaffected Versions
- Adobe ColdFusion 2021 Update 1
- Adobe ColdFusion 2018 Update 11
- Adobe ColdFusion 2016 Update 17
Check for the Vulnerability
Version Check
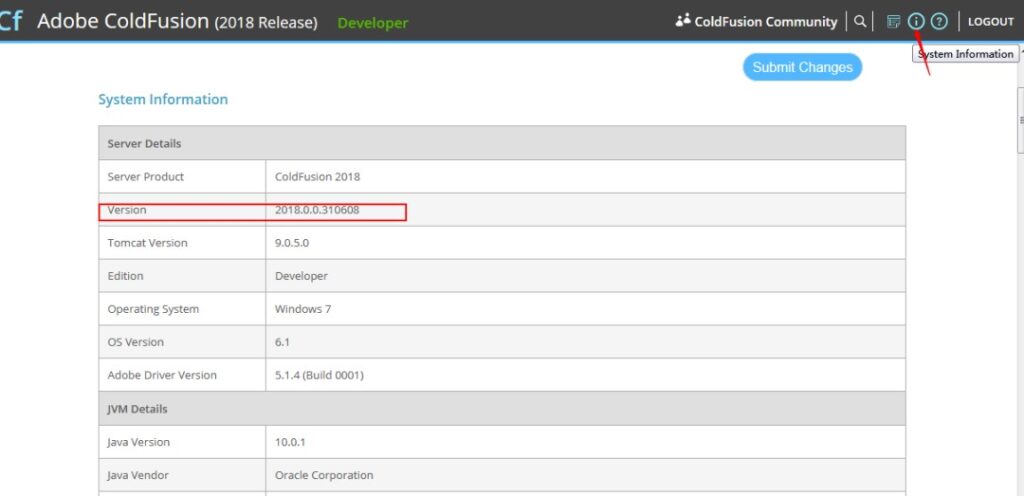
Users can determine whether their application is vulnerable by checking the current version.
1. Log in to Adobe ColdFusion and access /CFIDE/administrator/index.cfm to check the version in system information.
2. Run the cfinfo -version(info) command under bin of the installation directory of Adobe ColdFusion to view the version. If it is one of the affected versions, the application is vulnerable.
Mitigation
Official Fix
Currently, the vendor has fixed this vulnerability in the latest versions. Affected users are advised to upgrade as soon as possible from the following links:
Adobe ColdFusion 2021:
https://cfdownload.adobe.com/pub/adobe/coldfusion/2021/updates/hotfix-001-325996.jar
Adobe ColdFusion 2018:
https://cfdownload.adobe.com/pub/adobe/coldfusion/2018/updates/hotfix-011-326016.jar
Adobe ColdFusion 2016:
https://cfdownload.adobe.com/pub/adobe/coldfusion/2016/updates/hotfix-017-325979.jar
Note: For Adobe ColdFusion 2016 HF7 and earlier, this security update requires ColdFusion JDK/JRE to be updated to JDK 8u121 or higher.
Additionally, execute the following commands according to the downloaded patch files (on the condition that you have the ability to start or stop ColdFusion services and have full access to the ColdFusion root directory.)
Execute the following command on Windows:
<cf_root>/jre/bin/java.exe -jar <jar-file-dir>/hotfix-*.jar
Execute the following command on Linux:
<cf_root>/jre/bin/java -jar <jar-file-dir>/hotfix-*.jar
Ensure that the JRE bundled with ColdFusion is used to execute the downloaded JAR. In a standalone installation, ColdFusion must be installed under <cf_root>/jre/bin.
For more information, see Adobe’s ColdFusion User Guide at the following link:
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
