At RSA Conference Innovation Sandbox Contest 2020, SECURITI.ai was named “Most Innovative Startup”. The technical directions shown in this year’s contest covered external data representation (XDR), DevSecOps, and TVM+SOAR. Obviously, security operations are still one of the main directions that ignite the most efforts of innovation companies.
According to the topics talked about at RSAC 2020, security operations are shifting from security orchestration automation and response (SOAR) solutions to DevSevOps, which features end-to-end automation and streamlined processes, and have incorporated automated security processes (such as automated bug findings) into the security orchestration and response system to practice the concept of “automate as much as possible”.
In the past years of security operations, NSFOCUS has established a comprehensive automated security orchestration and response system based on the SOAR solutions proposed by Gartner and incorporated the DevSecOps concept into the integrated device management and control system. This implementation path coincides with the concept of “automate as much as possible” put forward at the RSAC 2020 conference. The following sections detail NSFOCUS’s practices in and technical system for automated security orchestration and response.
Case-based Orchestration and Response System
Each security team has their own security toolkits, capabilities, general use cases, and compliance requirements. The process that includes all these elements is actually the steps that should be followed during incident response. We define the lifecycle of response to security O&M incidents as a continuous, cyclic process that involves security O&M incident learning and enrichment, incident management, in-depth investigation, response implementation, performance measurement, and improvement of future operations efficiency based on lessons learned. During incident response, the security team can collect logs from the SIEM or iSOC platform and then correlate log information based on incident contexts. For them, it is of crucial importance to have the event-oriented case management capability to avoid fragmented information.
Case management helps users to conduct procedural and continuous investigation and analysis and response for a series of associated incidents. Via procedural case handling, users can adopt different case handling procedures (playbooks) for different cases and then check how the procedures are performed. Through artifact management, users can collect related indicators of compromise (IOCs) and information about attackers’ tactics, techniques, and procedures (TTP). With the orchestration investigation and response function, users can execute the playbook or take actions on any artifacts recorded in the case, expand and track clues, dig deep to clear doubts, and enrich case information.
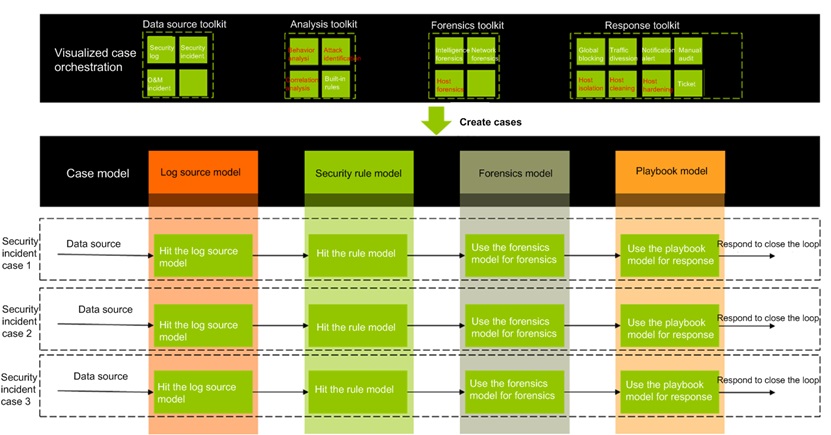
NSFOCUS’s SOAR system uses visualized security orchestration for security incidents of the same type. Our case models include the data source model, security rule model, forensics model, and automatic response model. The architecture is as follows.
Incidents of the same type are categorized into one case. In this way, they can be responded with the same playbook. Besides, security, execution success rate, and execution efficiency of such responses are measured to check the overall execution efficiency and accuracy, thereby facilitating the adjustment of policies.
Visualized Security Orchestration Process
The security orchestration process is about the arrangement, coordination, and management of predefined limited operations, operation processes, and assets. The automation of heterogeneous solutions helps reduce the time to respond. As a result, the orchestration reduces the risk exposure window and gives security analysts more time to focus on tasks of a higher value.
Security orchestration is equivalent to a power amplifier, which simplifies analysts’ work process, provides instant contexts for security alerts, and accelerates alert operations that would otherwise be performed manually. Technology integration, playbooks, and dashboards can be used for quick investigation and collaboration with infrastructure. Automated security processes and maintenance process consistency can save time and improve the efficiency of security operations. Through the security orchestration process, security analysts can focus on high-priority links such as threat analysis, threat hunting, in-depth investigation, and proactive forensics, in a bid to put enterprises one step ahead of attackers in the closed-loop process of security threat monitoring, analysis, forensics, and response.
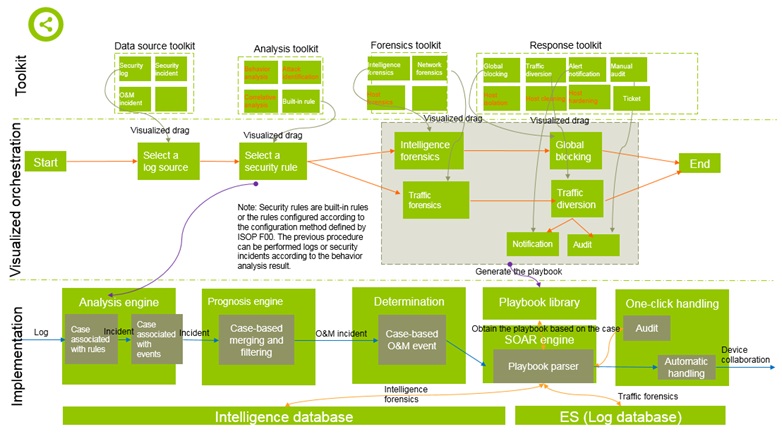
NSFOCUS’s SOAR system supports such logical toolkits as log source defining tookits, analysis toolkits, determination and forensics toolkits, and response toolkits. Based on the threat analysis and response process, operations personnel can select tools for the orchestration of analysis, forensics, and response. The overall flow is as follows:
Playbook-based Automatic Handling
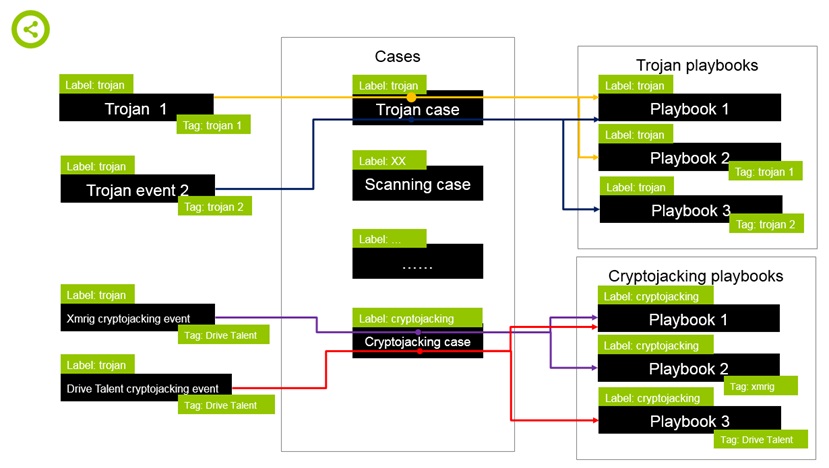
Playbooks record security engineers’ experience and workflow of responding to threat scenarios. Playbooks can be used for automatic O&M work, which is more rapid, accurate, and sustainable than manual O&M work. Playbooks can be referenced during visualized orchestration, forming an automatic handling model for a specific threat case. Threat events can be handled according to the selected playbook. The implementation is as follows:
As shown in the preceding framework, when designing case models, the user can categorize similar threat models and similar response methods into one case and adopt the same playbook to handle them, which greatly reduces the difficulty of security orchestration and effectively improves the flexibility and efficiency of responses.
Technically, playbooks are written in Python and can be updated by using NSFOCUS’s official knowledge base. NSFOCUS’s SOAR system provides a powerful SDK toolkit and playbooks can be used in complicated automated orchestration scenarios with less code, to address not only NDR-oriented global blocking, traffic diversion, and host isolation but also EDR-oriented host cleaning and hardening.
Playbooks can be generated in either of the following ways: (1) They are automatically generated via visualized orchestration; (2) They are manually written and imported. In simple scenarios, visualized orchestration can be directly employed, with no need of manual code. In complicated orchestration scenarios, though the code cannot be automatically generated simply by dragging, a code framework can be generated for manual orchestration.
DevSecOps-based Device Integration and Collaboration
While guaranteeing the product reliability, DevOps is designed to significantly reduce the development cycle and improve the system deployment frequency and efficiency by means of optimized technical frameworks and agile development processes. The focus is on rapid delivery.
In NSFOCUS’s SOAR security operations system, how to rapidly integrate various security devices is an important link and has rapidly evolved into a critical part in incident response. As we all know, the traditional waterfall-like development and version-by-version deployment greatly slow down device integration, thereby remarkably reducing the efficiency of the SOAR operations system.
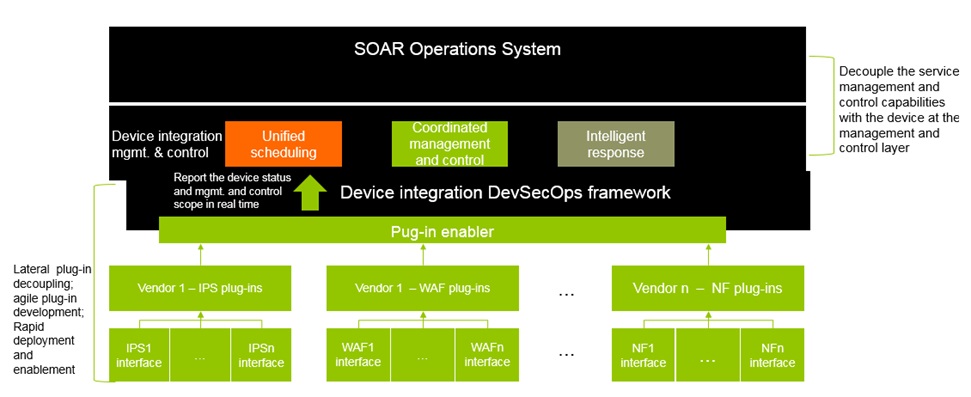
To guarantee the speed and efficiency of device integration, we introduce the DevSecOps framework for device management and control.
Through the DevSecOps framework:
- Any devices of a new type can be integrated for iterative development by installing a plug-in package and be deployed quickly, without affecting the existing devices.
- After a device is deployed, its management and control scope will be instantly reported to the device integration DevSecOps framework for intelligent scheduling in a unified manner.
- Based on the device integration DevSecOps framework, the SOAR engine can obtain the management and control scopes and status information of different devices in real time. Based on the management and control scope, the engine then intelligently selects a response device for collaboration, thereby implementing service response and device decoupling. This lays a solid foundation for the security orchestration and the versatility and openness of response, providing cross-platform portability of cases and playbooks.
Efficiency of Orchestration-based Automatic Handling
By accelerating and simplifying the threat response process, security orchestration makes competitions fairer. It integrates different technical and incident handling processes into a coordinated security operation process. A proper orchestration solution can buy time for security professionals, allowing them to focus on urgent tasks with a higher priority. This helps reduce response time and risk exposure, and keep the consistence of cross-application processes. However, to ensure the effectiveness of orchestration, we must avoid incorrect concepts and defective methods when assessing and selecting orchestration policies.
According to the status quo of different enterprises, policies and practical application must be taken into consideration for automatically performing tasks. To achieve this goal, tasks should be broken down, analyzed, and encoded as granular as possible in the process of integration automation. During automatic tasks, we can concentrate more on repeated tasks and high-valued tasks with repeated steps, in a bid to prioritize them and allow them to be performed more rapidly and efficiently.
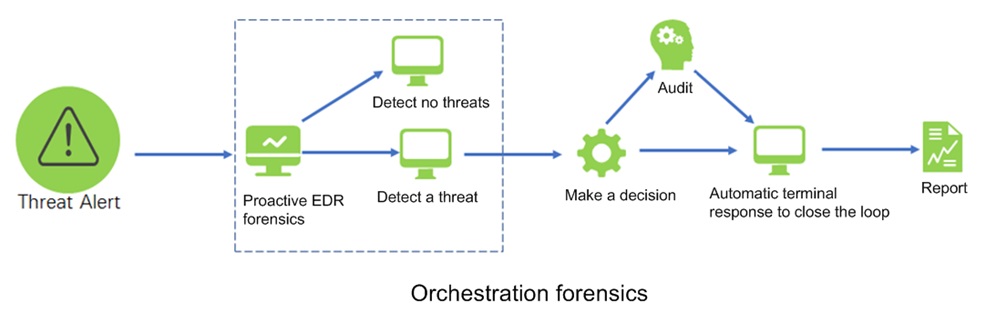
For example, host security threat alerts require instant host contexts for determining whether the terminal (or host) is prone to any IOC threats. Then the analysts decide whether to isolate the terminal to reduce further risks. The forensics and query processes adopted by the analysts are repeatable and expected responses are identifiable. Manually executing these responses can prolong the risk and increase the possibility of risk spreading. Prior to human intervention, these steps can be automatically performed.
For security threats of this type, in the NSFOCUS’s SOAR system, the data source model, analysis model, forensics orchestration model, and response playbook model are defined as a case based on the case model. Therefore, when an attack occurs, a model defined by the case will be triggered and the corresponding task will be automatically performed.
During an automatic task, when an IOC alert is generated, the orchestration process will be immediately initiated to check the alert against the IOC library, so as to:
- Check whether the threat really exists.
- Check whether further forensics information of the endpoint is required.
Check whether the alert should be reported to the analysts who have the complete context, so that they can take further actions accordingly.
Via orchestration, an IOC which previously takes hours or even days for manual investigation can be investigated in dozens of seconds and threat responses can be completed within a few seconds by automatically executing a playbook.
Conclusion
No matter whether automated security orchestration is mature enough, it can greatly improve the value of the security operations system. When we pursue automatic security orchestration, some best practices stand out. We must have a good knowledge about our own security infrastructure, environments, resources, risks, and security objectives. By combing such information, we can identify automatic tasks with a higher priority more easily. The automation can produce high-valued outcomes, giving more time for security experts and significantly reducing the duration of cyberattacks. With the improvement of our ability to make strategic decisions, we can streamline and optimize the security operations process, so as to improve the overall security maturity.
In the past few years, via continuous attempts and exploration, NSFOCUS has established an automated security orchestration and response system based on its security operations platform by integrating the concept of fast development and deployment of DevSevOps into response device integration. We have rich operations experience regarding threat-oriented automatic blocking and terminal-oriented security response. We look forward to working with other security experts to create a bright future of automated security orchestration.