According to the analysis of geographic distribution of IPv6 attack sources, China had the largest proportion of attack sources (86.76%), followed by the USA (3.97%) and Romania (0.77%).
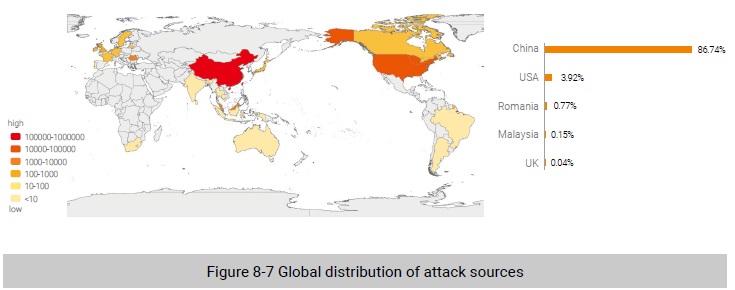
As shown in Figure 8-7, China was home to the largest number of attack sources.
Conclusion
In 2019, as the data breach situation was more severe than previous years, data security protection battles grew more and more intense. Trends in legislation and law enforcement suggest that governments at home and abroad are taking proactive measures. For enterprises, compliance has
become a top security concern.
DDoS attackers were powered by maturing techniques. Multi-vector volumetric attacks posed a greater challenge to defense operations. Amid DDoS attack incidents, behaviors of active gangs deserve special attention. Besides, the number of IoT devices involved in DDoS attacks increases year by year as a result of hackers finding their way into IoT devices via Telnet, repeatedly and successfully, further dampening the cybersecurity landscape.
The IPv6-based Next Generation Internet (NGI) will become the cornerstone to support the rapid development of cutting-edge technologies and industries. Amid this trend, IPv6-related vulnerabilities are on the rise. Besides, application-layer attacks using IPv6 addresses have become the simplest and most efficient attack method. For managers in charge of IPv6, the first priority is to follow up with the evolution of traditional security threats in IPv6 environments.
As mobile payment and mobile office are increasingly popular, mobile devices have become common constituents of the APT attack surface. APT groups still take phishing as the major means at the intrusion stage and have never slackened their pace of updating their toolkits and improving their attack methods. Worse still, they collude with other botnet owners. Predictably, botnets will open the door for APT attacks.
