Since the Promoting Scale Deployment of Internet Protocol Version 6 (IPv6) (“Plan”) 1 was published in November 2017, IPv6 deployments in China are on the rise. By June 2019, the number of active IPv6 users had reached 130 million, and 1.207 billion telecom users had been assigned an IPv6 address. At the same time, IPv6 traffic in China in the past year steadily grew. The number of address resources ranked first in the world (47,282 IP address blocks (/32)) by May 2019. Telecom enterprises have made positive efforts to improve network infrastructure. All recursive domain name systems (DNS) of the three telecom magnates support IPv6 domain name resolution. Content delivery network (CDN) enterprises have conducted IPv6 deployments nationwide and have got the capability of accelerating distribution of IPv6 addresses. The transformation of backbone networks, LTE networks, and metropolitan area networks (MANs) has been almost completed2 . With the rapid development of the IPv6 technology, more attention should be paid to security threats in the IPv6 environment. This section describes the threat situation from the perspectives of vulnerabilities and traffic.
IPv6 Vulnerability Trend
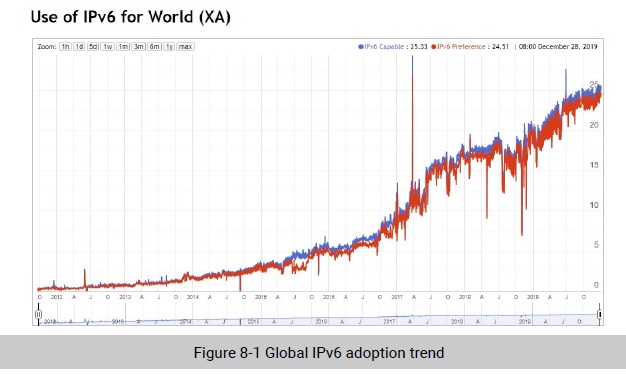
With the depletion of IPv4 addresses and since a World IPv6 Launch Day was carried out where countries permanently enabled IPv6 for their networks and applications in 2012, the deployment of IPv6-related systems, networks, and application services will be increasingly pervasive. So far, 25.33% networks have adopted IPv6 deployments.
With IPv6 networks and services going live, IPv6 system resources draw more and more attention from attackers. Amid this trend, IPv6-related vulnerabilities have gained momentum for rapid growth. Therefore, the Internet construction is facing severe security challenges. Compared with the IPv4 protocol, the IPv6 protocol is more secure, but the mechanism for transferring packets remains unchanged. As a result, IPv6 networks are still exposed to the same attacks as IPv4 networks. For example, HTTP attacks against the application layer and TCP attacks against the transport layer can also pose a serious threat to IPv6 networks. Since new fields and protocols are introduced, IPv6 packets are likely to contain vulnerabilities. For example, IPv6 extension headers, the Neighbor Discovery Protocol (NDP), and ICMPv6 protocol can be exploited by attackers for launching sniffing attacks and denial-of-service attacks. According to NVD statistics, a total of 369 IPv6 vulnerabilities have been detected since 2002.
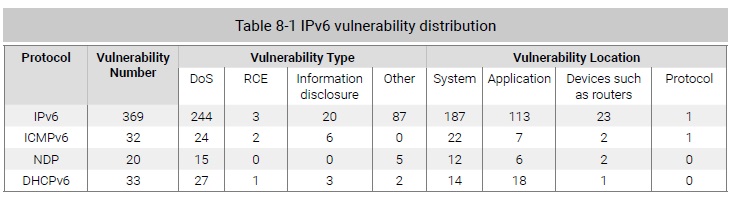
Among all IPv6 vulnerabilities, denial-of-service vulnerabilities account for 60% (244), 185 of which are remote ones. DoS attacks can be devastating to network devices and services. Given the large proportion of DoS vulnerabilities, it will be an arduous task to defend against related attacks. It is noteworthy that the current IPv4 Internet is such a huge system that the economic and technical costs of migrating corresponding devices and application systems to the IPv6 Internet will be enormous. As a result, IPv4 and IPv6 networks will coexist for a long time. For smooth transition from IPv4 to IPv6, corresponding transitional techniques have been developed and put into practice, including dual stack, tunneling, and protocol translation. Security issues related to transitional techniques should also be considered. Currently, there are 16 vulnerabilities related to transitional techniques in the current vulnerability database. It is predictable that this number will increase in future.
Attack Type Distribution
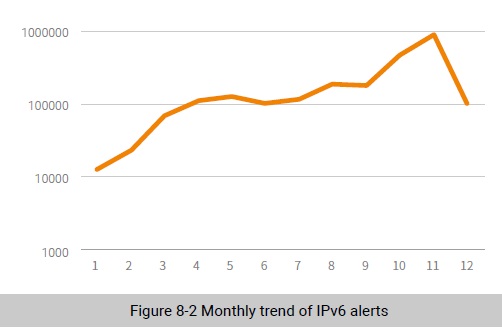
In 2019, there were 295 types of alerts in the IPv6 network environment, reaching 2.37 million in total. Figure 8-2 shows the monthly trend of IPv6 alerts. As shown in the figure, IPv6 alerts were in the upward trend; in November, the number peaked at 880,000.
Malware
Backdoors and cryptojacking malware are the most frequently detected malware, followed by trojans, ransomware, and worms.
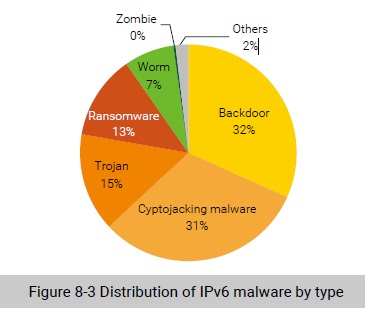
In 2019, most alerts were generated on backdoors in the IPv6 environment, accounting for 32%. Figure 8-4 shows the daily trend of backdoor attacks. June and July saw the most back alerts, and several daily peaks were formed. Most alerts were generated in early July, peaking at 1633 in a day.
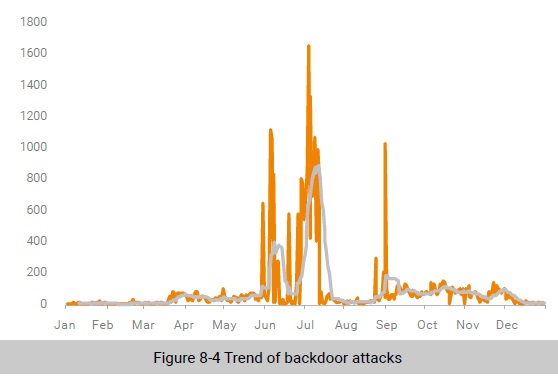
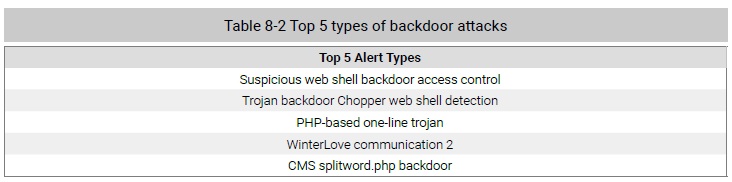
Table 8-2 lists top 5 types of backdoor attacks. It is worth noting that 27,500 alerts were generated on suspicious web shell backdoor access control attacks, contributing 87.8% of all trojan attacks.
In the IPv6 environment, cryptojacking alerts accounted for 31%, second only to backdoors. As shown in Figure 8-5, cryptojackers in the IPv6 environment had a lower level of activity in early 2016. Then the number of alerts increased slowly but burst in late June. At the end of 2019, there were a large number of IPv6 cryptojacking alerts. Late June and early July saw the most cyptojacking activities. The peak period lasted for nearly a month.
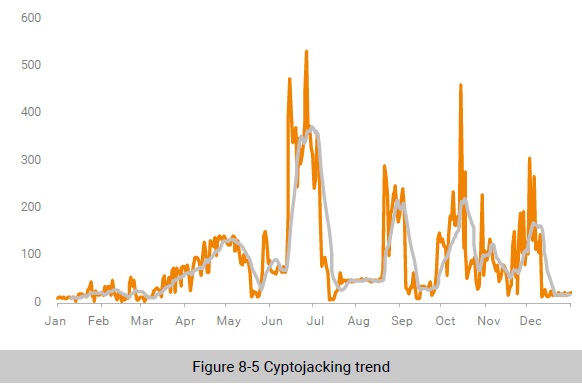
Table 8-3 lists top 5 cryptojacking activities. Most alerts were generated on WannaMine connection communication and WannaCry attempted communication, followed by Monero (XMR) cryptominer network communication, malicious cyrptominer XmrigDNS request connection, and cyrptominer query DNS mining pool server domain name.

Web Attacks
In terms of attacked applications, web services were the major attack target, accounting for 44%, followed by DNS services (42%).
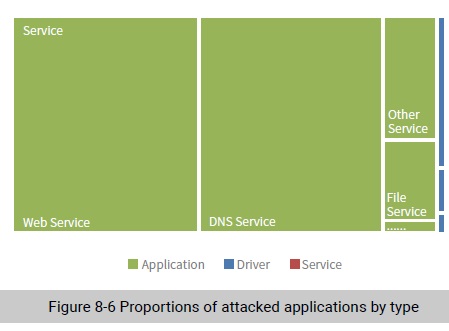
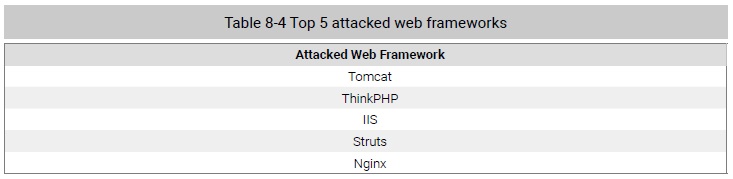
Table 8-4 lists top 5 attacked web frameworks. Tomcat and ThinkPHP received the most attacks, followed by Internet Information Services (IIS), Struts, and Nginx.
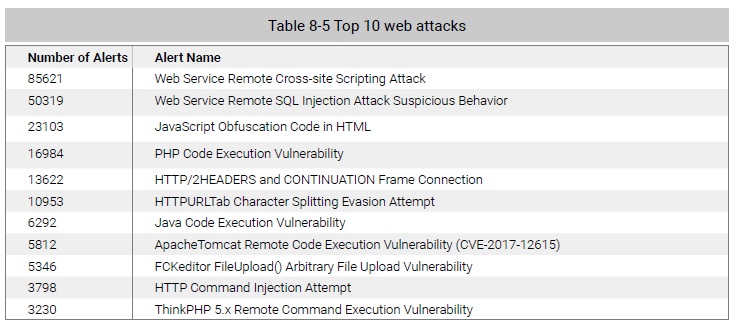
Remote cross-site scripting attacks were still the most common web attacks, an increase of 10 times from 2018.
To be continued.
