Threats Against WS-Discovery
WSD is a multicast discovery protocol to locate services on a local area network (LAN). However, due to device vendors’ design flaw in the implementation, when a normal IP address sends a service discovery packet, devices will also respond to the request. If exposed on the Internet, these devices will be possibly exploited for DDoS reflection attacks. In February 2019, security researchers 1 from Baidu published an article 2 about WSD reflection attacks. This is the first report we have read about such attacks. In a post 3 , ZDNet mentioned that WSD reflection attacks were first reported in May, and in August, many organizations began to use this protocol to launch DDoS attacks. According to Akamai, one of its customers in the gaming industry suffered a WSD reflection attack weighing in at 35 Gbps at peak bandwidth.
Around the world, about 910,000 IP addresses (80% (730,000) were video surveillance devices) provided the WSD service and were thus at risk of being exploited to launch DDoS attacks.
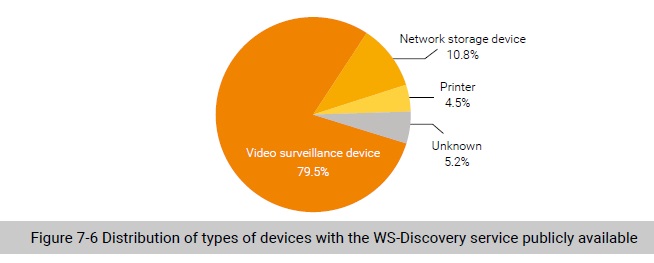
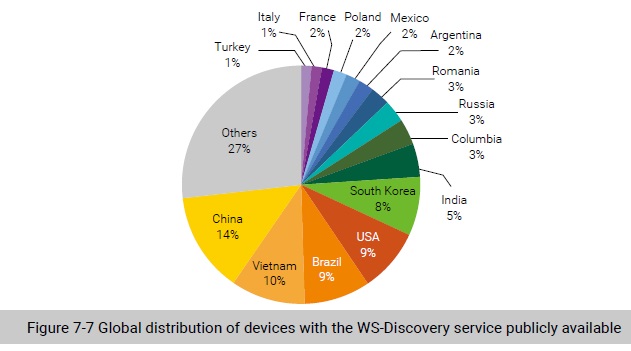
Figure 7-7 shows the global distribution of devices with the WS-Discovery service publicly available. We can see that China, Vietnam, Brazil, the USA, and South Korea saw the most devices with this service publicly available.
We analyzed attack events captured by NSFOCUS’s threat hunting system. Here all events about one IP address in one day add up to an attack event. Figure 7-8 shows the daily number of attack events. At a glance, WSD reflection attack incidents fluctuated all the time, but had been on the rise generally since mid-August, especially in September. This indicates that WSD reflection attacks have been gradually adopted as a regular weapon of DDoS attacks, to which all parties concerned, including security vendors, service providers, and telecom operators, should pay due attention.
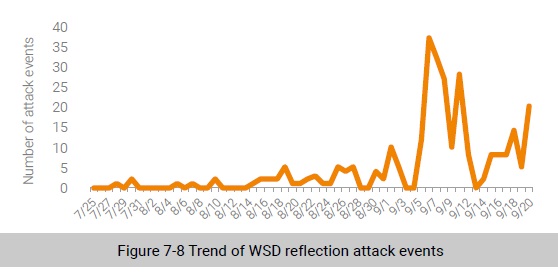
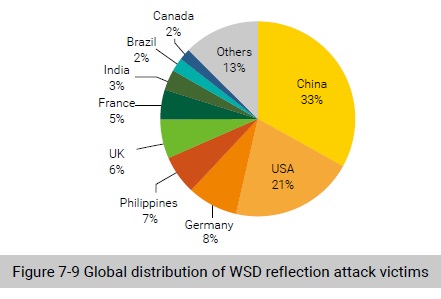
Figure 7-9 shows the global distribution of WSD reflection attack victims. We observed that up to 24 countries and regions were hit by this kind of attack. China was most targeted by WSD reflection attacks, home to 33% of victim IP addresses, followed by the USA (21%).
To be continued.
