Finding 1: In 2019, over 30 types of IoT vulnerability exploits were captured, most of which targeted remote command execution vulnerabilities. Though hundreds of to thousands of IoT vulnerabilities are unveiled each year, only a few can exert an extensive impact. Attackers were keen on targeting devices (routers and video surveillance devices) exposed in large quantities, in a bid to broaden their influence.
Finding 2: IoT devices, especially cameras and routers, were major targets of Telnet weak password cracking attacks.
Finding 3: Since security researchers from Baidu disclosed that the Web Services Dynamic Discovery (WSD) protocol could be exploited for DDoS reflection attacks, there has been a notable increase in reflection attack events based on this protocol in the latter half of 2019. Since mid-August, WSD reflection attacks captured by us have been on the rise. Worse still, September has witnessed a sharp increase in such attacks. All parties concerned, including security vendors, service providers, and telecom carriers, should pay due attention to this type of threats.
Finding 4: Approximately 2.28 million IoT devices (port 1900) worldwide had the UPnP/SSDP service publicly accessible and were thus at risk of being exploited to launch DDoS attacks, an decrease of 22% from 2018.The UPnP port mapping service, exposed on about 390,000 IoT devices, was likely to be abused as a proxy or render intranet services accessible on the extranet.
IoT-related Malware
In the past few years, the IoT has gained momentum for rapid development, giving rise to an increasing variety of IoT devices, including processors, routers, cameras, and smart devices. These devices have insufficient safeguards. Successful exploitation of their vulnerabilities could lead to escalated system privileges. By analyzing attack alerts generated by intrusion prevention systems (IPSs), we can find out which vulnerabilities were most favored by hackers and how many times they were involved in actual attacks in 2019.
Vulnerabilities in IoT devices stem from web applications, systems, and protocols. As for web applications, users usually use default settings and weak passwords, exposing devices to SQL injection and XSS threats. At the system level, as far as cameras are concerned, the read-only memory (ROM)
usually uses such file systems as SquashFS, JFFS2, and UBIFS, which contain some vulnerabilities.
Whether the firmware is upgraded in time depends on the importance attached by device vendors on the one side and users’ willingness to promptly upgrade it on the other side. Finally, there is a broad variety of application protocols. Cameras alone use the Universal Plug and Play (UPnP), Real-Time Streaming Protocol (RTSP), and standards and specifications from the Open Network Video Interface Forum (ONVIF). If these protocols contain unauthorized access vulnerabilities, there is a good chance of cameras being attacked by hackers.
IoT-related Vulnerabilities Exploited
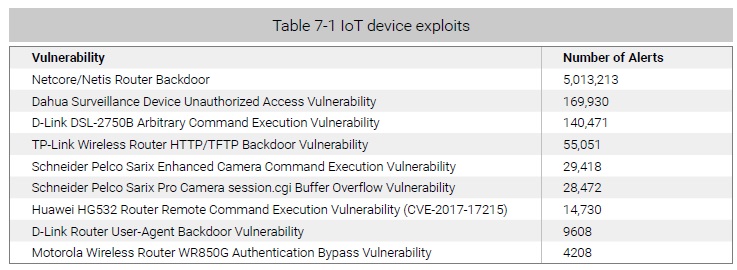
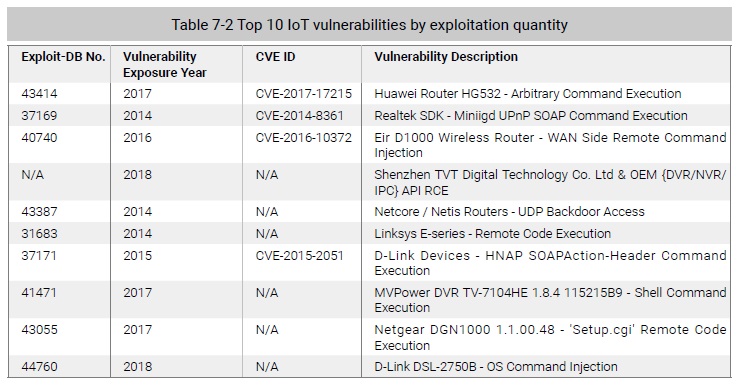
Based on logs captured by NSFOCUS’s threat hunting system from May 6 through November 6, 2019, we made an analysis of global IoT vulnerability exploits.
Over 30 types of IoT vulnerability exploits were captured, most of which targeted remote command execution vulnerabilities. Arguably, from the perspective of global IoT threats, though hundreds of to thousands of IoT vulnerabilities are unveiled each year, only a few can exert an extensive impact. We counted all logs generated one day for a source IP addresses as one attack event. Upon deduplication of attack IP addresses, we got top 10 IoT vulnerabilities listed in the descending order of exploitation quantity in Table 7-2. It can be seen that attackers’ vulnerability exploits mainly targeted routers and video surveillance devices, which fits in with the fact that routers and video surveillance devices were major IoT devices exposed on the Internet. Evidently, attackers prefer to hit devices exposed in large
quantities to extend their influence. The proof of concept (PoC) of most of these vulnerabilities can be found in the Exploit Database and those beyond this database are available on GitHub. Those publicly available PoCs have substantially reduced attackers’ cost of crafting attack payloads.
After statistics deduplication, we analyzed the global distribution of source IP addresses. As shown in Figure 7-1, China was home to most malicious IP addresses, about one order of magnitude higher than other countries following it such as Brazil, the USA, and Russia. In China, up to 20,000 IP addresses initiated exploit behaviors, 85% of which resided in Taiwan. Of those attack behaviors, nearly 90% targeted the same UPnP vulnerability (CVE-2017-17215).
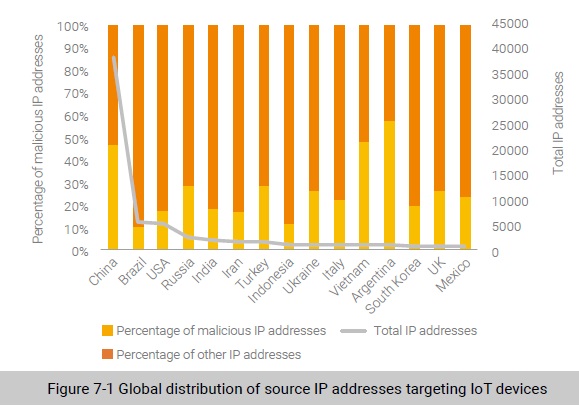
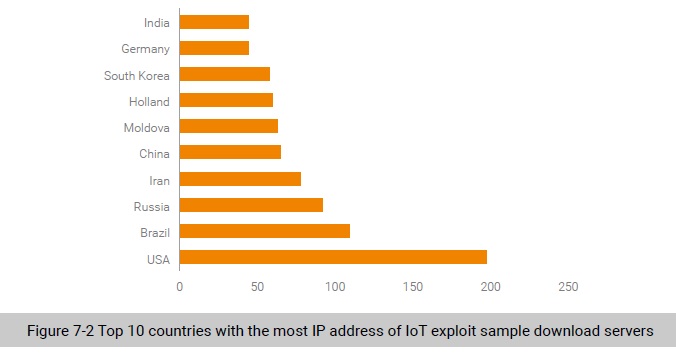
Figure 7-2 shows the global distribution of IP addresses of servers for download of exploit payload samples. Obviously, the USA had the most sample download servers, with a percentage of 15.9%.
To be continued.
