Analysis of DDoS Attacks in 2018
3.1Â DDoS Attack Count and Peak Size
3.1.1Â Attack Count and Traffic
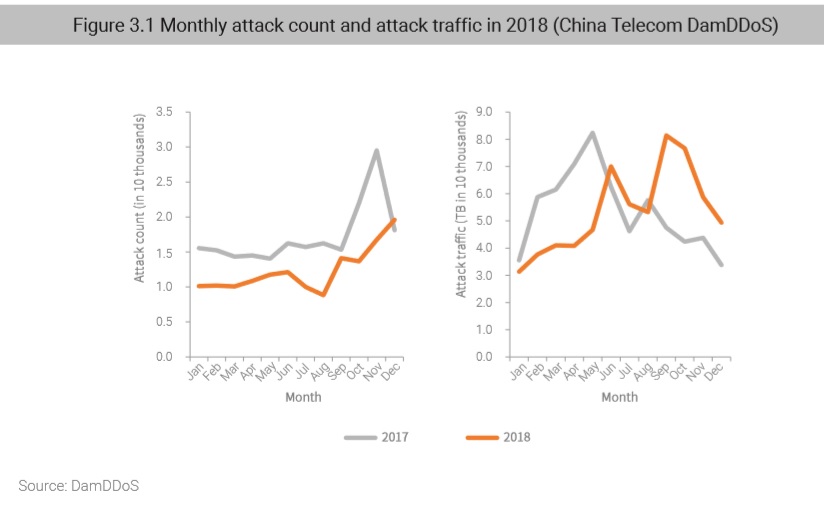
In 2018, we observed 148,000 DDoS attacks (down 28.4% from 2017), which generated a total of 643,100 TB of traffic, about the same level as in 2017. DDoS attacks keep expanding in size year by year as large and medium-scale attacks are on the rise, as shown in section 3.1 “Distribution of Peak Sizes.”
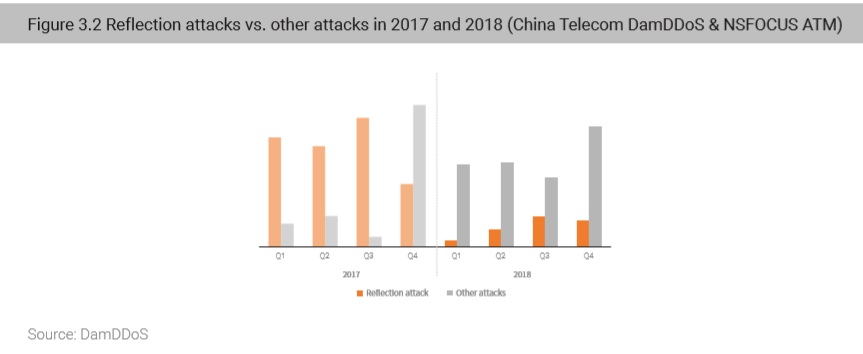
In 2018, the number of DDoS attacks dropped significantly, driven by effective protections against reflection attacks. Since the beginning of 2018, the National Computer Network Emergency Response Technical Team/Coordination Center of China (CNCERT/CC), in cooperation with carriers and cloud service providers around the country, carried out a special campaign against attack resources in China using techniques including identifying bogus source IP addresses and making reflection attack sources known to the public. These governance measures have effectively reduced the success rate of reflection attacks, forcing attackers to resort to other means. According to statistics, in 2018, the number of  reflection attacks decreased 80%, but that of other attacks increased 73%. As a result, reflection attacks accounted for only 3% of all DDoS attacks.
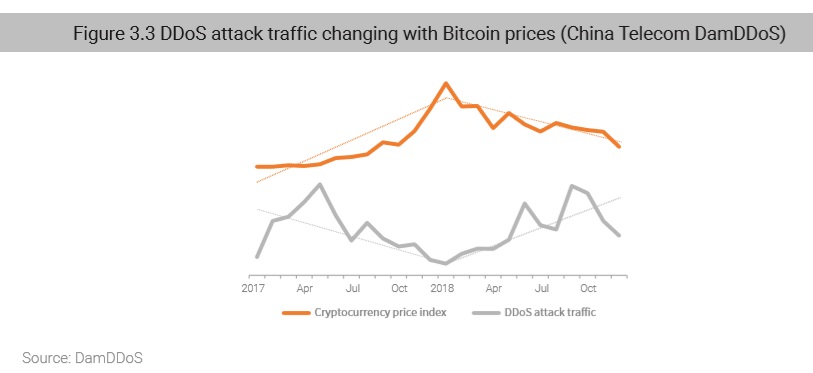
In the first half of 2018, the number of DDoS attacks increased slowly, but in the second half, the increase accelerated. We believe that the month-over-month increase in the number of DDoS attacks was linked with the fall of cryptocurrency prices. In the 2017 DDoS and Web Application Attack Landscape4, we pointed out that, with the appreciation of cryptocurrency, hackers on the black market began to divert prime botnet resources to cost-efficient cryptomining activities from costly DDoS attacks. In 2018, the price of cryptocurrency dropped, leading to decreased profits from cryptomining, which, in turn, made DDoS attacks more attractive and increase month by month.
Comparing the monthly Bitcoin price with the monthly DDoS attack traffic, we get the Pearson correlation coefficient of –0.48, indicating a negative correlation between the two, which corroborates our findings from last year.
3.1.2 Distribution of Peak Sizes
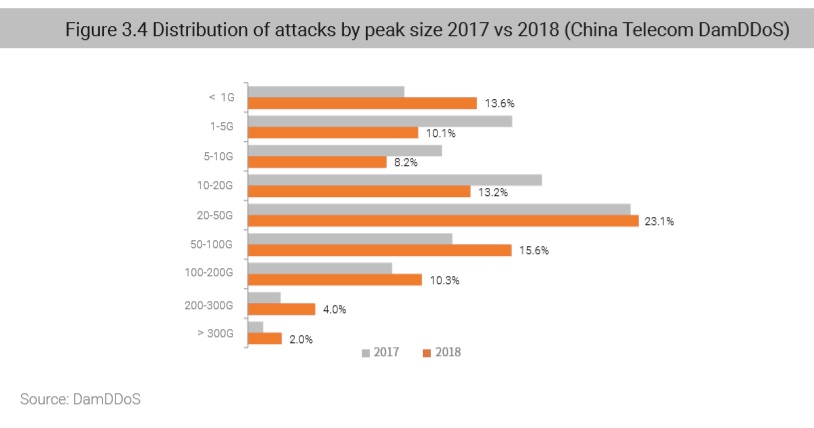
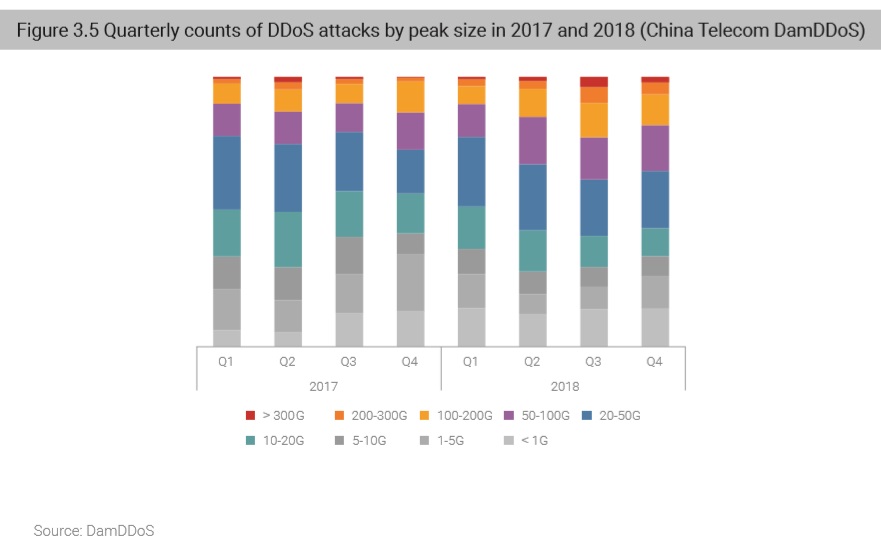
The peak sizes of DDoS attack traffic mainly ranged from 20 to 50 Gbps and attacks within this range accounted for 23.1% of all DDoS attacks. Compared with 2017, the year 2018 saw a decrease in smallscale attacks (< 20 Gbps), an increase in medium- and large-scale attacks (20–200 Gbps), and double the super-large attacks (> 200 Gbps).
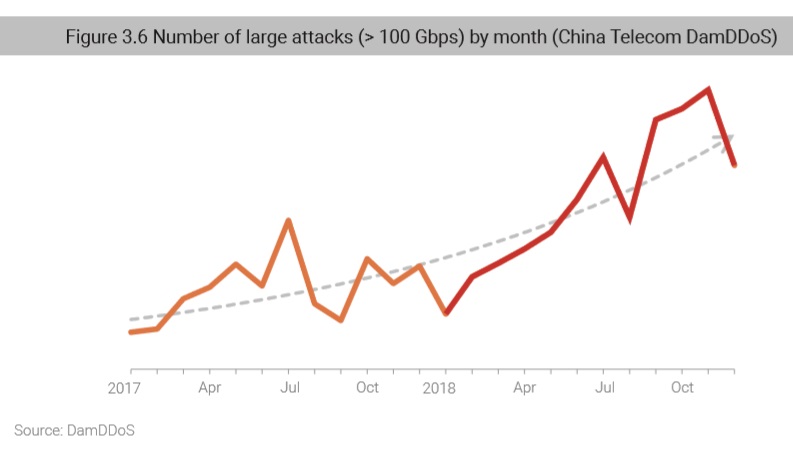
According to quarterly statistics, the number of large DDoS attacks with a peak rate of greater than 100 Gbps steadily increased. From the second quarter, large attacks increased rapidly, especially in the third quarter when large attacks took up 23% of the total attacks.
4ï¾ https://nti.nsfocus.com/pdf/2017_DDoS_and_Web_Application_Attack_Landscape_en.pdf
In recent years, super-large attacks have emerged and constantly grown in the peak size. In March 2018, the well-known code hosting website GitHub was hit by a DDoS attack peaking at 1.35 Tbps. As of the time of writing, the peak traffic rate of DDoS attacks had reached a record high of 1.7 Tbps.5
The monthly statistics in the past two years reveal that large attacks with a peak rate of more than 100 Gbps have rapidly increased. This indicates that the scale of attack resources controlled by attackers is expanding and their attack capabilities are constantly upgraded.
5ï¾ https://www.wired.com/story/github-ddos-memcached/
3.1.3Â Maximum and Average Peak Sizes of Individual Attacks
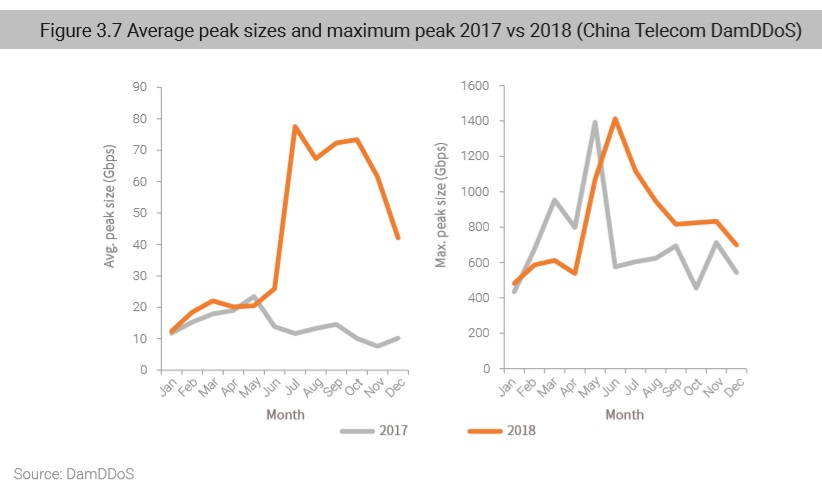
In 2018, the average peak size of DDoS attacks hit 42.8 Gbps, thrice that of 2017 (14.1 Gbps). Peak sizes were especially large in the second half of 2018, reaching 67 Gbps, mainly driven by the widespread improvement of network bandwidths and significant enhancement of DDoS attack capabilities.
As for the maximum peak size, we observed an attack in June 2018 peaking at 1.41 Tbps, on a par with 2017.
The improved DDoS attack capabilities and the record high of average peak sizes both point to the fact that DDoS attacks are becoming increasingly more damaging. As a matter of fact, most hackers can generate super-large traffic and their capabilities are still growing rapidly, which is becoming a greater challenge for defenders and security governance personnel.
to be continued