-
Vulnerability Description
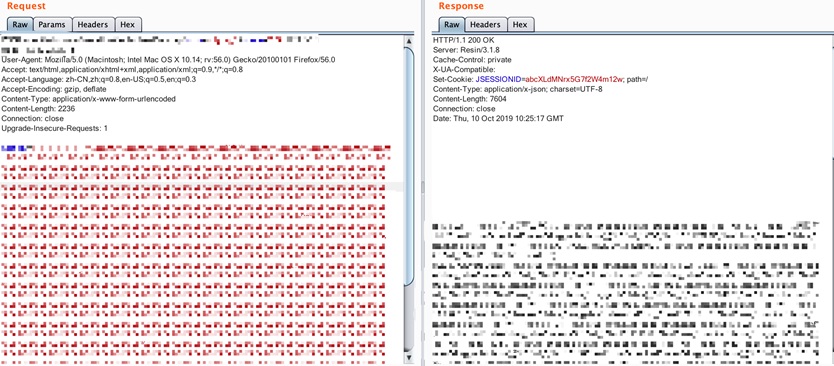
On October 10, 2019, the national information security vulnerability sharing platform of China (CNVD) announced a SQL injection vulnerability (CNVD-2019-34241) in the Weaver e-cology OA system. When the workflowcentertreedata interface of the Weaver e-cology OA system uses the Oracle database, due to the loose splicing of the built-in SQL statements, there is a SQL injection vulnerability in the Weaver e-cology OA system.
By exploiting this vulnerability, an attacker can send a specially crafted SQL statement remotely without authorization to obtain database’s sensitive information. At present, the vulnerability POC has been made public, but no patch has been released officially.
References:
https://www.cnvd.org.cn/webinfo/show/5235
 2. Scope of Impact
Affected Versions
- The Weaver e-Science OA system using the JSP version of Oracle database
 3. Mitigations
-
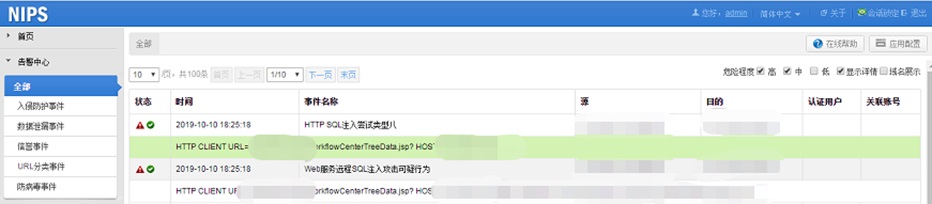
Product protection
Users deployed with NSFOCUS web application protection system and network intrusion prevention system (IPS) have the ability to protect against  the SQL injection vulnerability.
Alerts on WAF
Alerts on IPS
-
Temporary Mitigation Measures
At present, the Weaver OA has not officially released a patch to fix the vulnerability. The workarounds are as follows:
- Using the parameter check method, block parameters with SQL syntax;
- Using the pre-compiled processing method, handle SQL statements spliced with user parameters;
- Before the parameters are about to enter the database, perform the integrity check on the semantics of SQL statements to confirm that the semantics has not changed.
- When a SQL injection vulnerability occurs, filter or verify the parameters before they are spliced into SQL statements. Do not rely on the protection code at the beginning of the program.
- Regularly audit the database execution log to see if there is any SQL statement execution outside the normal logic of the application;
- It is forbidden to make the affected systems publicly available on the Internet.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide multi-layered, unified and dynamic protection against advanced cyber attacks.
NSFOCUS works with Fortune Global 500 companies, including four of the world’s five largest financial institutions, organizations in insurance, retail, healthcare, critical infrastructure industries as well as government agencies. NSFOCUS has technology and channel partners in more than 60 countries, is a member of both the Microsoft Active Protections Program (MAPP), and the Cloud Security Alliance (CSA).
A wholly owned subsidiary of NSFOCUS Information Technology Co. Ltd., the company has operations in the Americas, Europe, the Middle East and Asia Pacific.