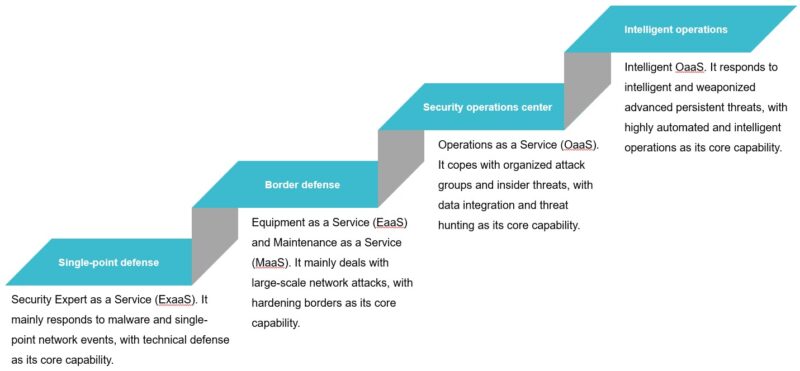
With the boom of the global digital economy, cybersecurity is converging with the Internet of Things (IoT), industrial Internet, cloud computing, and 5G, bringing about disruptive changes to security in various aspects, including traditional physical security, biological security, public security, and national security. Meanwhile, the attack surface keeps expanding in...
Tag: IoT
Function Identification in Reverse Engineering of IoT Devices
This document dwells upon function identification and symbol porting in reverse engineering of Internet of things (IoT) devices without using BinDiff and PatchDiff2, which are "too good" for the purposes here and are inapplicable in certain scenarios. Typical function identification technologies include the Fast Library Identification and Recognition Technology (FLIRT)...
Technical Analysis Report on Rowdy, A New Type of IoT Malware Exploiting STBs
In August 2017, NSFOCUS's DDoS situation awareness platform detected anoma-lous bandwidth usage over a customer's network, which, upon analysis, was confirmed to be a distributed denial-of-service (DDoS) attack. The attack was characterized by different types of traffic, including TCP flood, HTTP flood, and DNS flood. Tracing source IP addresses, we...