SANTA CLARA, Calif., July 6, 2025 – Recently, NSFOCUS Anti-DDoS (NSFOCUS ADS) was recognized by the internationally renowned consulting firm Frost & Sullivan and won the 2025 Asia-Pacific “Competitive Strategy Leadership Award for Excellence in Anti-DDoS Protectionâ€[1]. Frost & Sullivan Best Practices Recognition awards companies each year in a variety of...
Tag: ADS
Coming Soon! NSFOCUS Will Enhance DDoS Protection Capabilities in New Version of ADS Products
We are excited to announce the upcoming release of the ADS V4.5R90F06 version, which brings significant enhancements to our DDoS protection capabilities. The update focuses on bringing more precise DDoS mitigations. This new version improves existing algorithms with an emphasis on advanced technology and usability. Key New Features: 1. DNS...
Shining Moments for NSFOCUS DDoS Defense in 2024
January - Release of the 2023 Global DDoS Landscape Report In the 2023 Global DDoS Landscape Report, NSFOCUS proposed important insights on global DDoS threats. DDoS attacks have become an indispensable weapon in cyber warfare, attackers are gradually favoring the use of Virtual Private Server (VPS) as attack sources, and...
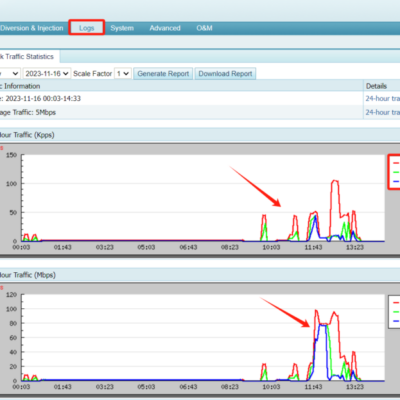
ADS Attack Traffic Statistics Graph
In the 24-Hour Traffic graph under Logs -> Logs Analysis > Attack Traffic Statistics of ADS, you will find the graph displaying three lines: ALL_RX_MAX (represented by the red line), ALL_RX (represented by the green line), and ALL_TX (represented by the blue line). The explanation of each line is: ALL_TX...
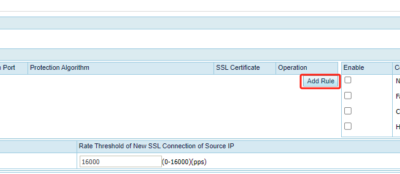
HTTP/2 Protection in ADS R90F03
Function Description For HTTPS application layer protection, ADS establishes a TLS connection with a client in replace of the server, and then authenticates the client through the application-layer protocol HTTP. If the client properly responds to the HTTP packet from ADS, ADS deems this client reliable and will add it...
FBI Warning: New DDoS Reflection Attacks Are Coming, Are You Ready?
According to ZDNet’s reports, FBI released a warning last week that some new network protocols were used by criminals to launch large-scale DDoS attacks. Three protocols and one Web applications were found as DDoS attack vectors, including CoAP, WS-DD, ARMS and Web-based Jenkins. (mais…)