Secret Life of Enterprise Botnets
The Secret Life of Enterprise Botnets is a speech in a session of RSA Conference 2023 by Dr. Craig Labovitz, Head of Technology for the Deepfield business unit at Nokia. In collaboration with global Internet providers, researchers tracked more than 500,000 compromised enterprise servers, security cameras and IoT (HVAC, PoS, etc.) over one year.
The Changed Landscape of Enterprise Botnet DDoS
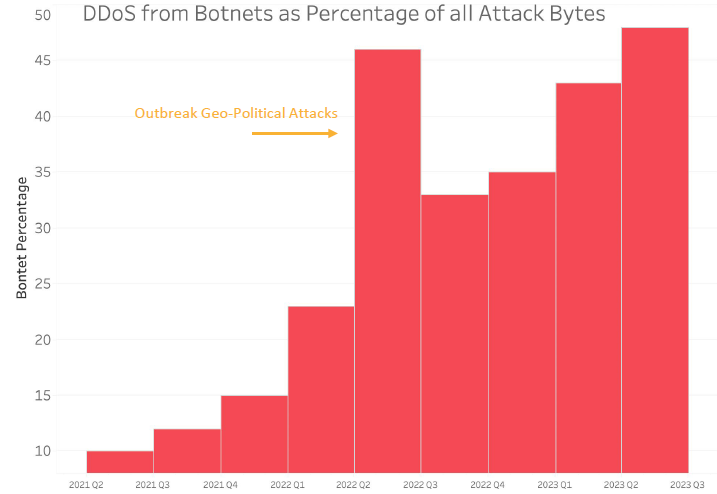
With the rapid development of the Internet and the extensive application of computer technology, DDoS traffic is growing faster than any other type of traffic. From 2010 to 2022, most DDoS attack traffic was spoofed traffic by abusing misconfigured DNS servers, NTP servers, and LADP servers. But the DDoS threat landscape has witnessed some changes recently. This is the first time that the majority of DDoS traffic originated from enterprise botnets.
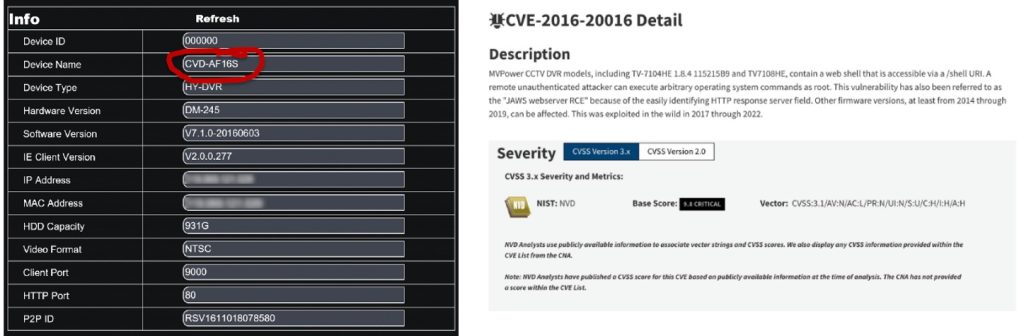
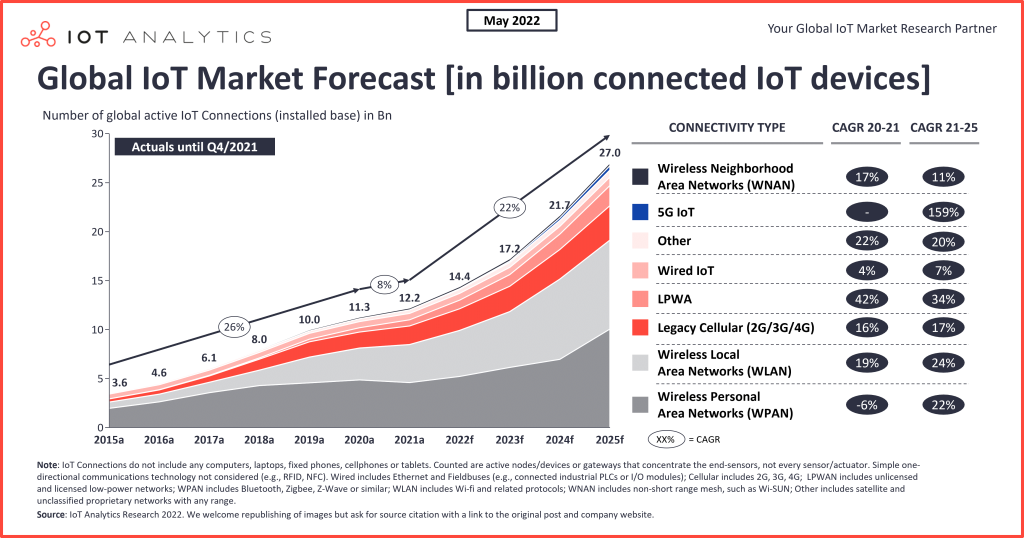
Undoubtedly, the widely applied IoT devices in enterprises are one of the main reasons. The number of global IoT connections grew by 8% in 2021 to 12.2 billion active endpoints, and It is expected there will be approximately 27 billion connected IoT devices by 2025, according to IoT Analytics Research report the State of IoT – Spring 2022 released in May 2022. We have to be aware of the extremely large amounts of IoT devices that have been deployed anywhere, such as DVR (Digital Video Recorder), wireless AP (Access Point), HVAC (Heating, Ventilation, and Air Conditioning), etc.
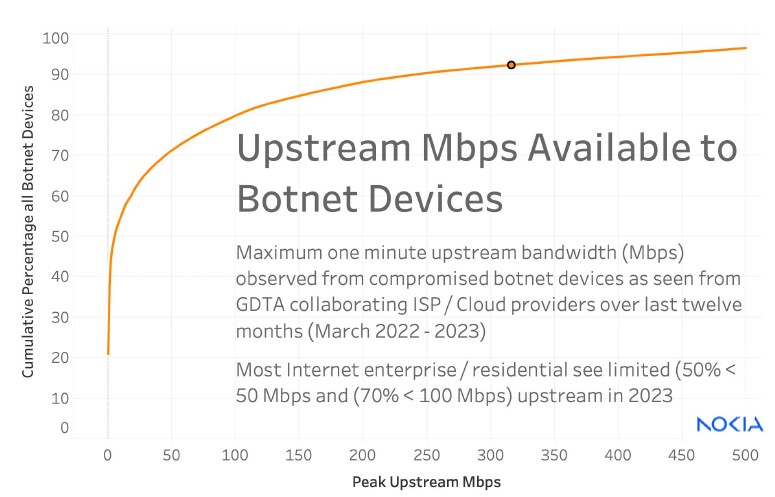
An interesting thing to note is that the DDoS traffic originating from IoT botnets has not resulted in tremendous influence before 2023. This is largely due to the fact that most Internet Service Providers (ISPs) provide asymmetrical connections service to residential customers, which means you can not have equal download/upload speeds. For example, 90/10 is the most common standard, meaning 90 Mbps download and 10 Mbps upload speed. And through data analysis, more than 70% of compromised IoT botnet devices can only generate less than 50 Mbps DDoS traffic. From this, we can see that the botnet is limited by today’s upstream bandwidth.
Plenty has changed since 2023. ISPs in the US and Europe started to upgrade their service to a symmetrical connection service with more than 1 Gbps download and upload speed. This change has resulted in exponentially growing DDoS traffic from IoT botnets.
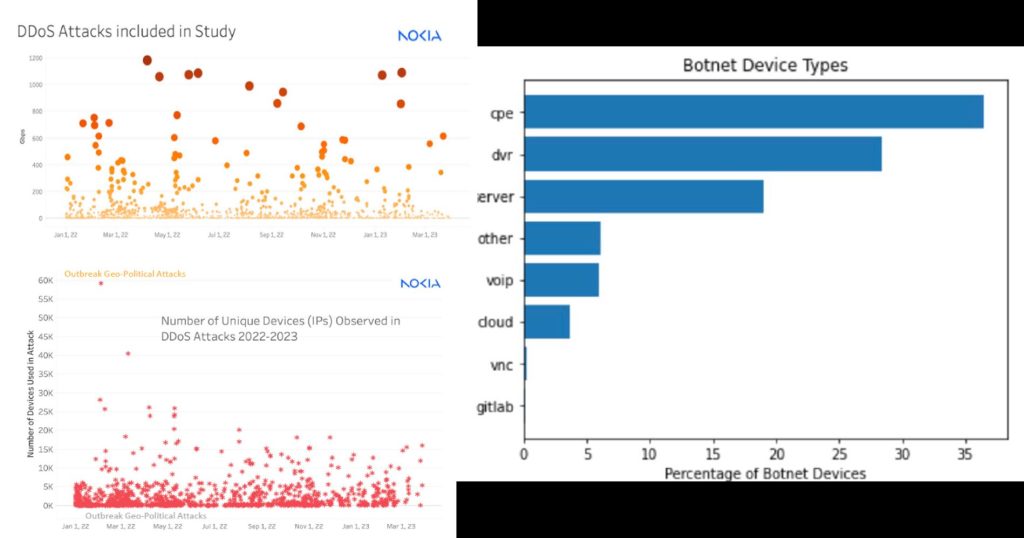
To get more effective information, Dr. Craig Labovitz started to study real-time data on botnets, worms, DDoS attacks, and other critical security threats shared within the Nokia GDTA program by collaborating with providers. Results from statistical analyses yielded three major findings:
1. The most disastrous DDoS attacks observed have peaked at 1 to 2 Tbps
2. A majority of IoT botnets are with fewer than 5,000 compromised IoT devices. But there is still a minority that controls more than 60,000 IoT devices.
3. From the perspective of device type, CPE (Customer Premise Equipment) devices comprise more than 35%, DVR devices are 30%, server devices are 20%, and others are 15%.
We must realize that enterprise botnets are particularly dangerous because they’re used in DDoS attacks, which can be commercially devastating and extremely difficult to stop. DDoS attacks have forced businesses to cough up large ransoms in several high-profile cases.
We have also explored the causes of thousands of compromised IoT devices, management deficiencies are one of the most severe reasons for most deployed IoT devices worldwide. First of all, remote access is an essential feature for the majority of IoT devices and yet it is widely exploited by cybercriminals. At the same time, many IoT devices still use the default passwords in daily operations and maintenance. Once cybercriminals discover the IoT devices open remote access like Telnet ports, they will try to infect the devices by brute forcing the login credentials, such as “admin†and “passwordâ€. And most IT teams have neglected to update software for deployed IoT devices. Cybercriminals can take advantage of CVE to enlist unpatched devices to its DDoS botnet resource pool that it operates for profit. As a result, it is becoming increasingly common for cybercriminals to infect IoT devices and sell the use of these botnet resources online.
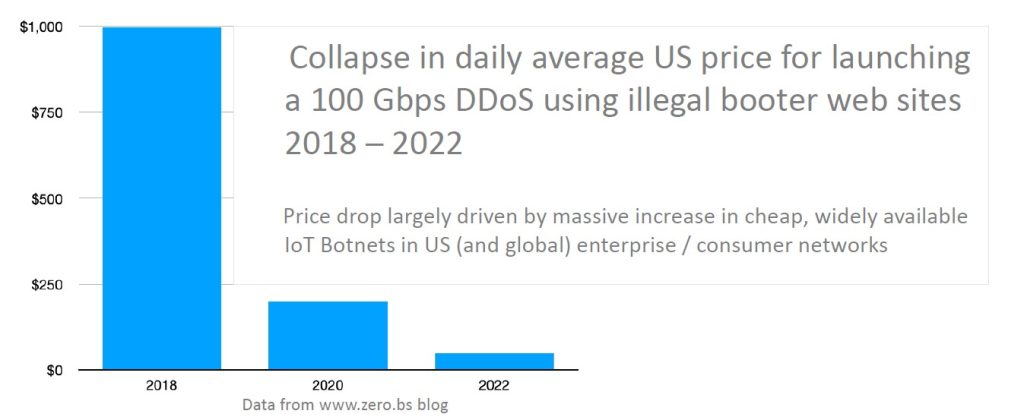
Another critical fact is that the price for launching a 100Gbps DDoS has dropped significantly from 2018 to 2022, meaning that almost anyone can launch DDoS attacks against their rivals to interrupt their services or attract their business with the cost of a few tens of dollars only. In addition, some botnet owners are operated legitimately and market themselves as “IP stressers†or “bootersâ€, which can be used to test the resilience of a website. That can create a vicious circle in that cybercriminals constantly capitalize on the added financial incentive to obtain more botnets. And falling prices of DDoS as a Service lower the skill threshold of such attacks and thus make them widely applied.
How to Mitigate Enterprise Botnet Attacks?
NSFOCUS recommends organizations follow the below mitigations to limit the damage caused by enterprise IoT botnets:
1. Implement network segmentation strategy, especially ensuring all IoT devices are deployed on a separate subnet from systems critical for daily operations.
2. Implement a strict password policy requiring IT teams to select and change a strong password frequently.
3. Check the software version of IoT devices at regular intervals to ensure less of a chance of infection.
4. Monitor inbound and outbound network traffic to detect anomalous behavior, such as botnet attacks.
5. Implement an advanced Anti-DDoS solution. NSFOCUS Anti-DDoS solutions mitigate network and application DDoS attacks by using approaches that mitigate malicious traffic without impacting legitimate traffic. Using machine learning and threat intelligence, NSFOCUS Anti-DDoS solutions can perform real-time behavioral analysis to detect botnet traffic and block all botnet activities before they even reach your network infrastructures while minimizing false positives.
6. Implement traffic analysis and visibility solutions. NSFOCUS MagicFlow Integrated Network Governance Platform allows for continuous, real-time monitoring and traffic analysis of business networks. Any anomalies that would indicate a DDoS attack can be detected via behavioral analysis, such as traffic directions, traffic components, and hotspot encrypted traffic, as well as to detect threats in large networks, providing all-around network-wide traffic analysis and handling capabilities for customers.
7. Establish a vulnerability management mechanism to prioritize possible threats and minimize their “attack surfaceâ€. Use NSFOCUS EASM (External Attack Surface Management) service to discover your internet-exposed attack surface and find potential risks continuously. Once a vulnerability is found, the critical and emergent vulnerability information will be sent to you automatically, including vulnerability description, affected software & versions and remediation plan.
References:
- The Secret Life of Enterprise Botnets: https://www.rsaconference.com/usa/agenda/session/The%20Secret%20Life%20of%20Enterprise%20Botnets?from_wecom=1
- State of IoT – Spring 2022: https://iot-analytics.com/product/state-of-iot-spring-2022/