A path traversal attack, or directory traversal, aims to access files and directories stored outside the web root folder. When the server does not check the user input strictly, by manipulating variables that reference files with “dot-dot-slash (../)” sequences and its variations or by using absolute file paths, it may be possible to access arbitrary files and directories stored on file system including application source code or configuration and critical system files. This attack is also known as “dot-dot-slash”, “directory traversal”, “directory climbing”, and “backtracking”. An attacker can obtain sensitive information from the server or control privileges of the system.
The most basic path traversal attack uses the “.. /” special-character sequence to alter the resource location requested in the URL. Although most popular web servers will prevent this technique from escaping the web document root, alternate encodings of the “.. /” sequence may help bypass the security filters.
Bypass methods:
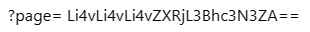
1. Encryption of data passed by parameters
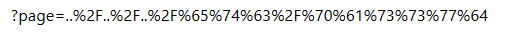
Some web programs use Base64 or other encryption schemes to encrypt data passed by parameters. Unencrypted parameters supplied by attackers will not be parsed, making it impossible for attackers to implement directory traversal. To bypass this protection, they may encrypt parameters with Base64 before passing them.
Example:
2. Encoding:
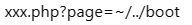
Attackers may encode parameters, such as the URL, before passing them to bypass the protection.
Example:
3. Directory access restriction bypass
Some web applications adopt access restrictions to prevent unauthorized access by attackers. To bypass this mechanism, attackers may add special symbols, such as “~”, in a URL.
Example:
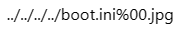
4. Extension filtering bypass
Some web applications check file name extensions before reading files. To bypass this check, attackers may append a null byte code to a file name.
Example:
5. Source validation bypass
Some web applications check whether parameters are supplied by trusted sources. To bypass this check, attackers may submit a URL on a website message board or at an interactive place, or directly change the HTTP referer.
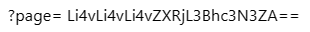
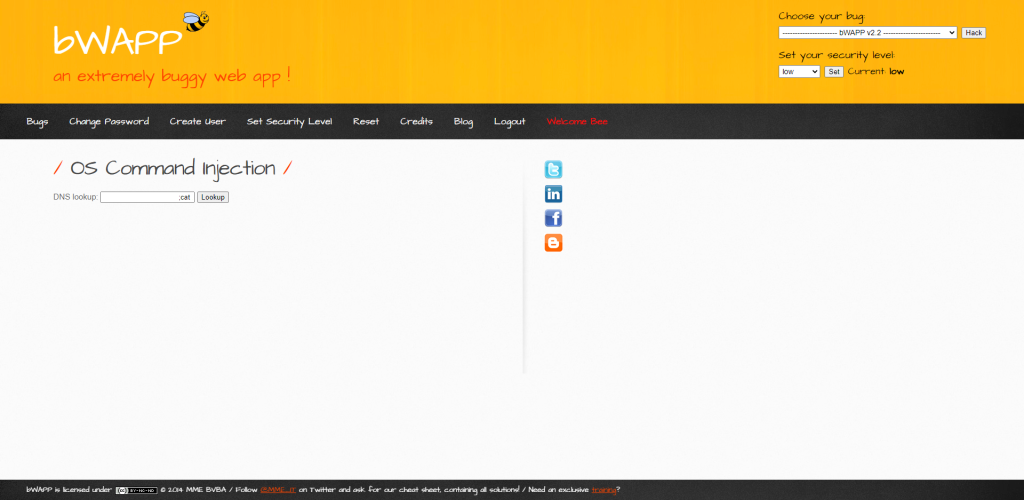
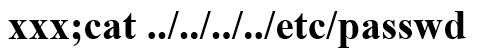
Example: path traversal attack demonstration by bWAPP OS command injection
Insert malicious code into the input box:
bWAPP response:
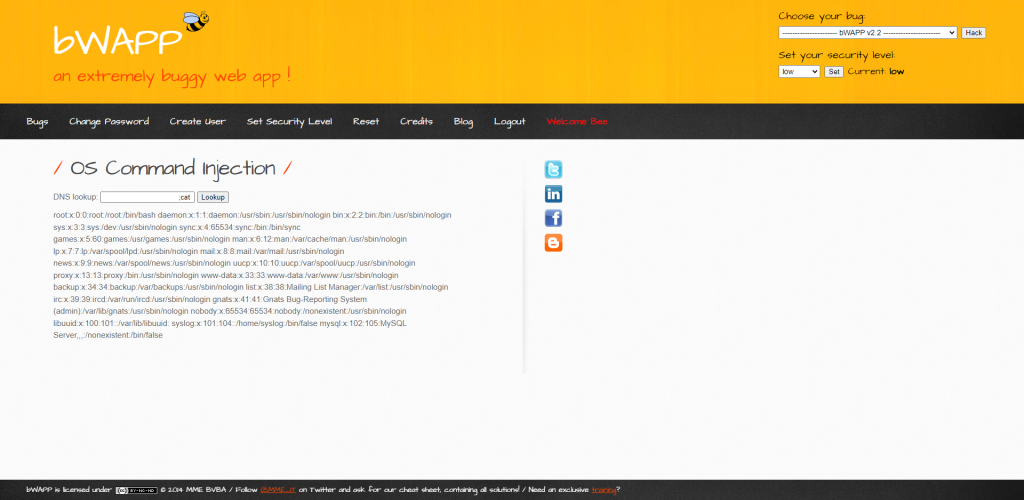
NSFOCUS WAF can analyze malicious scripts in the request packets and defend against malicious path traversal attacks.
To configure path traversal protection on NSFOCUS WAF, follow these steps:
1. Choose Security Management > Policy Management > Common Web Protection.
2. Click Create in the upper-right corner of the page.
3. Configure parameters in the Basic Information area as required, and click Path Traversal
Protection on the rule list and select path traversal algorithms.
4. Click OK.
5. Enable path traversal protection for a protected website.
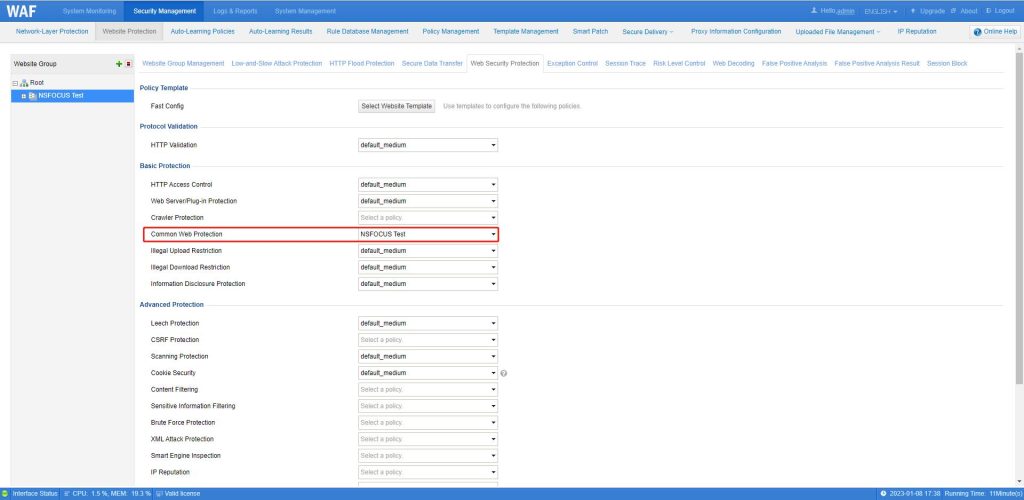
(1) Choose Security Management > Website Protection, select a website group, and click Web Security Protection.
(2) In the Basic Protection area, for Common Web Protection, select the policy created in steps 1–4, and click OK.
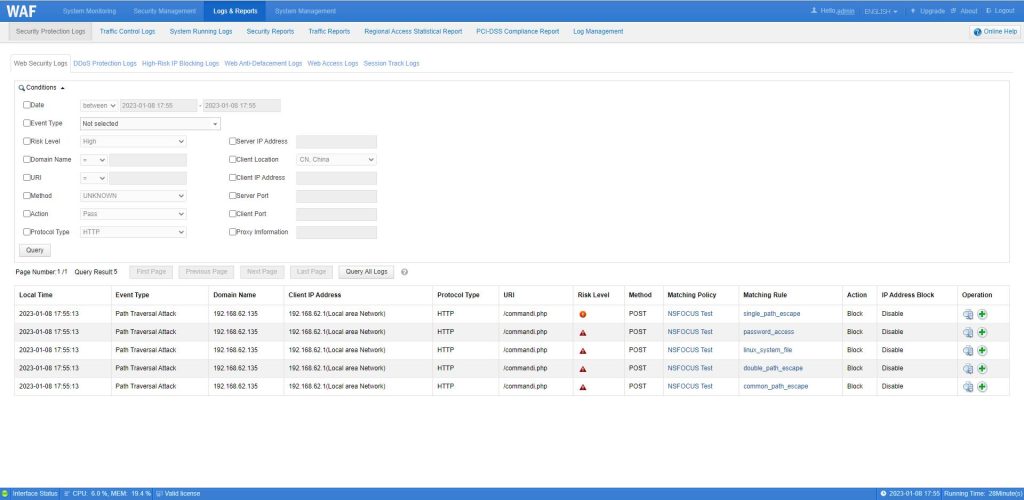
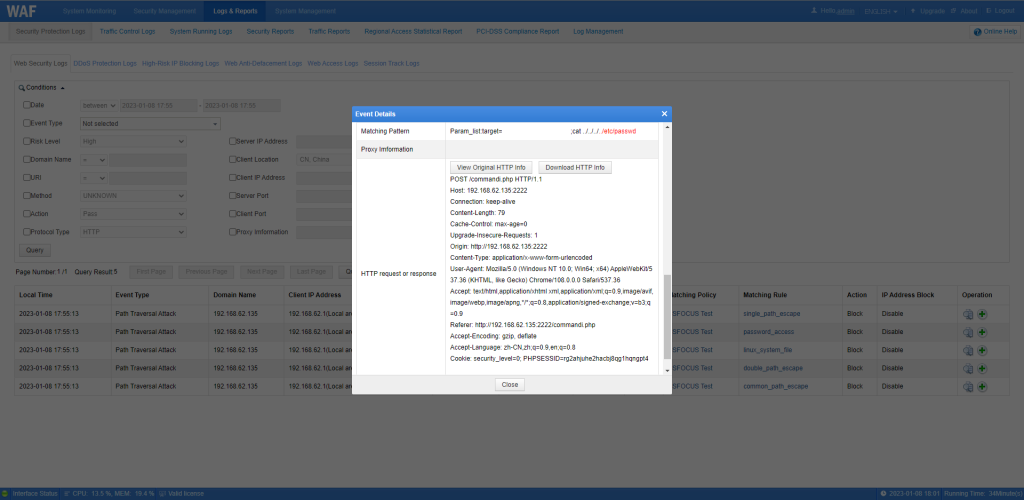
Check NSFOCUS WAF protection logs against bWAPP path traversal injections:
Choose Logs & Reports > Security Protection Logs > Web Security Logs.