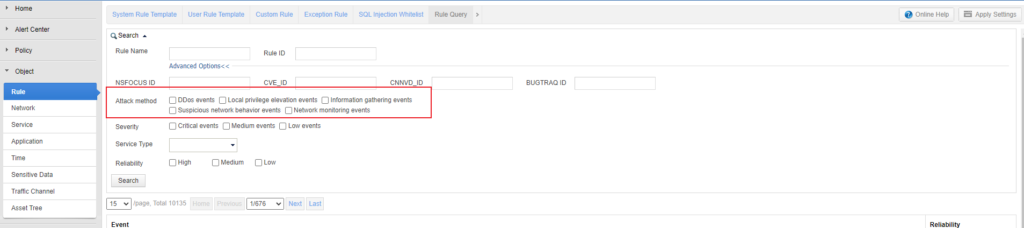
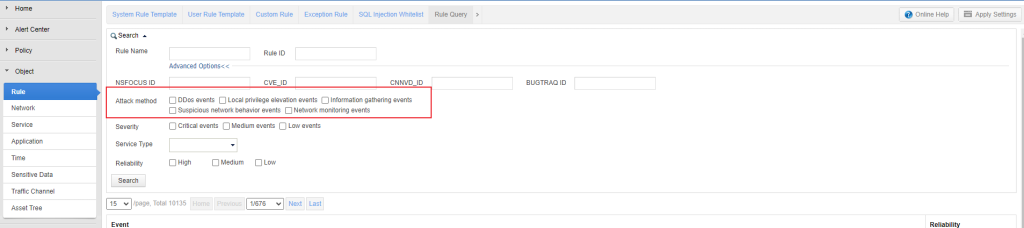
NIPS V5.6R10 has five types of rules to detect DDoS attacks, local privilege elevation, information gathering, suspicious network behaviors, and network monitoring events, respectively. They are described as follows.
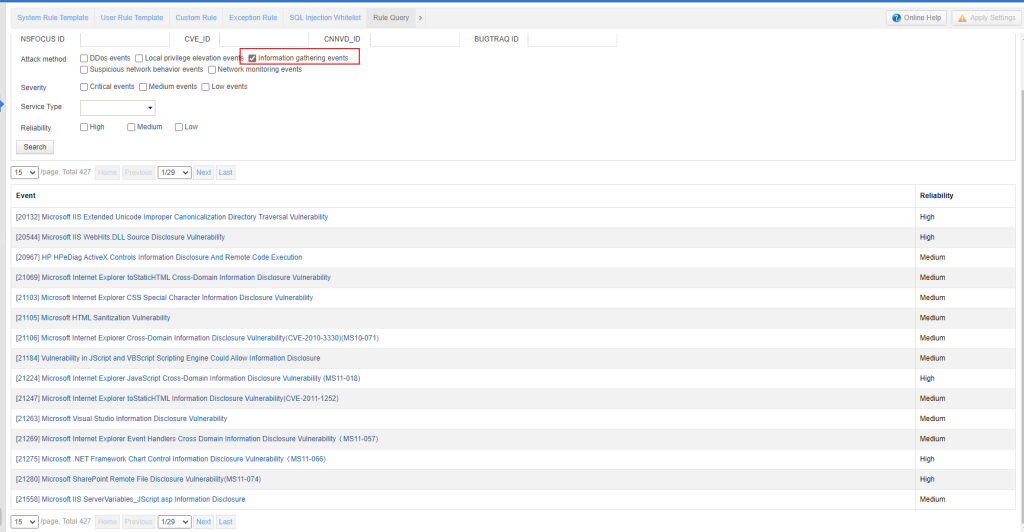
1. Information gathering
Information gathering is the first step of network intrusion. Attackers use various methods to scan and probe target hosts and identify paths to discover vulnerabilities on target servers. NIPS rule database contains rules for detecting directory traversal, information leak vulnerability exploitation, port scan, and so on.
Note that directory traversal vulnerability detection is strongly associated with web applications. If some web application signatures match IPS built-in vulnerability detection rules, legitimate traffic may trigger alerts. Handle alerts according to the actual situation.
2. Local privilege elevation
Attackers exploit the vulnerabilities on compromised hosts to start intrusion and obtain the server privilege for global control. NIPS rule database contains rules for detecting remote code execution, SQL injection, file inclusion, file upload, XSS, overflow attack, and other attacks.
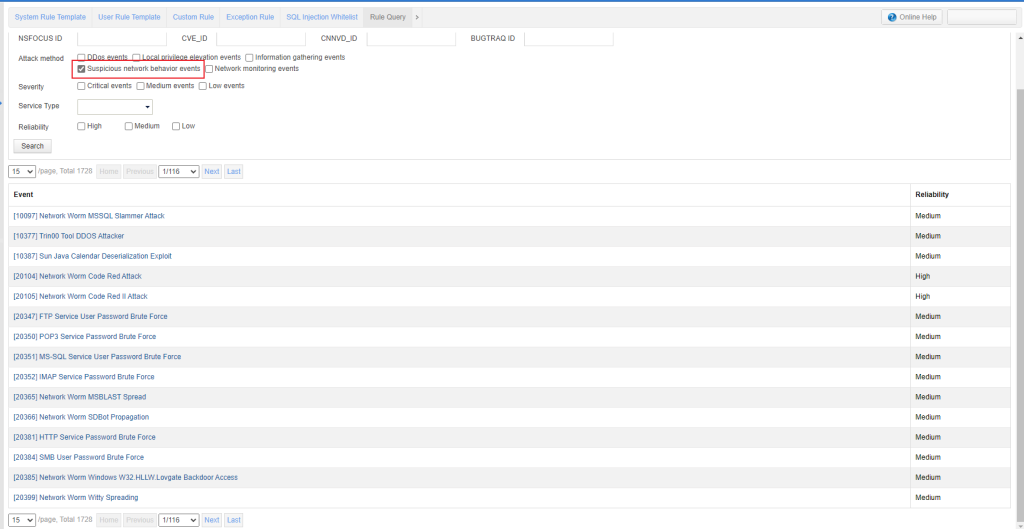
3. Suspicious network behavior
Generally, trojans or worms on compromised hosts perform suspicious network behaviors, such as malicious connections to external targets and cryptomining. NIPS rule database contains rules for detecting trojan communication, trojan file upload, worm, cryptomining, and other attacks. NIPS can detect HTTP/SMTP file upload behaviors of trojans and worms.
Note that suspicious network events are critical ones. If such events are alerted, trace back the source IP and check the server for a trojan infection.
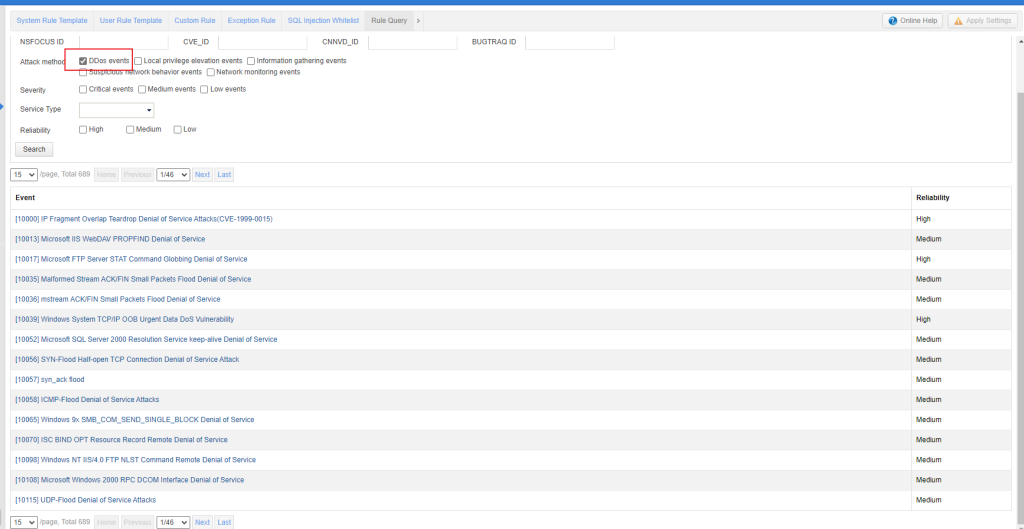
4. DDoS attacks
In a DDoS attack, attackers overflow the server with massive connection requests or exhaust the server’s resources or bandwidth to make it unresponsive to legitimate access.
NIPS rule database contains rules for detecting flood, port scan, and DDoS vulnerability exploit of common components, such as buffer overflows and memory leaks.
Notes:
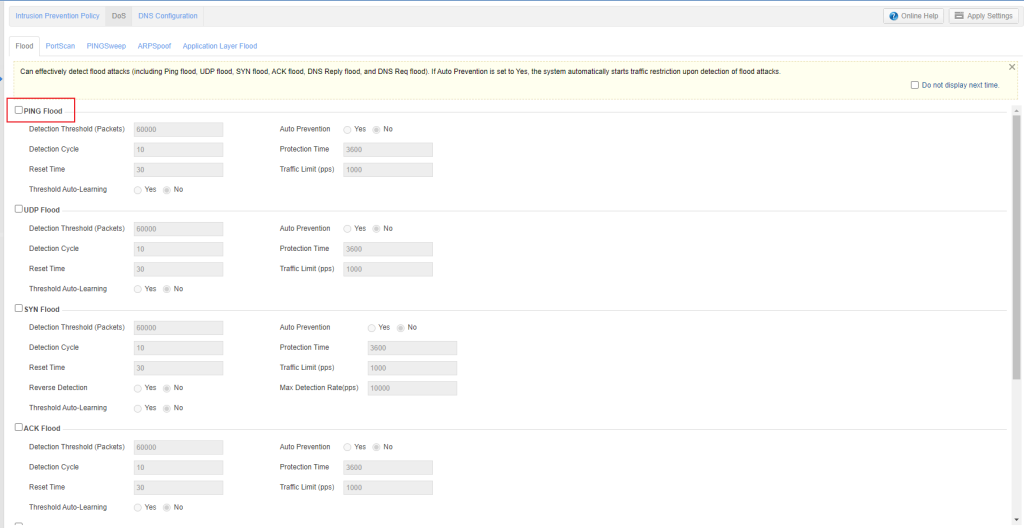
- DDoS detection rules are controlled by the DoS module. You should enable the DoS module to make DDoS detection rules take effect.
- NIPS performs traffic limit on DDoS attack traffic instead of blocking it. Even if block is chosen in the rule template, you will find DDoS attack traffic is allowed to pass according to the logs.
- Although port scan is used to collect information, this behavior is similar to a DDoS attack, and therefore, port scan detection is controlled by the DoS module.
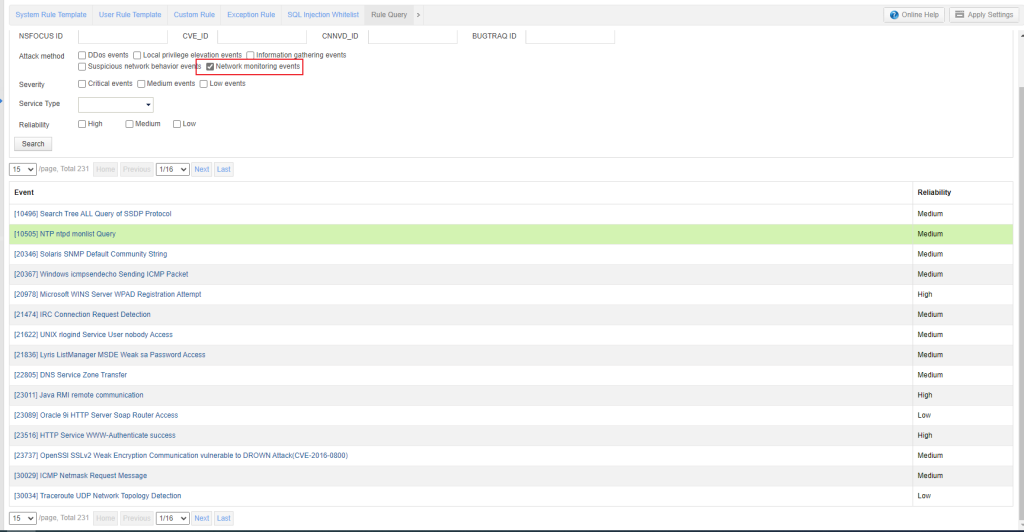
5. Network monitoring
Network monitoring alerts are used to notify customers of specific protocol packets in the customer network and whether they are legitimate. NIPS network monitoring rules can identify network events. However, a one-time event is not regarded as an attack. Network monitoring rules are those whose Technical Approaches in the rule description are set to Events Monitor. NIPS rule database contains rules for detecting FTP/SMB/Telnet login, web crawlers, weak password, ICMP detection, and so on.