I. Overview
In cybersecurity, big data is transforming threat intelligence and artificial intelligence, providing security teams with the flexibility to respond to changing environments. At the 2023 RSAC, Microsoft Vice President John Lambert discussed the convergence of intelligence and AI at the intersection of data and threats. The topic focused on how defenders can leverage threat intelligence and artificial intelligence to enhance threat defense and detection capabilities, thereby reducing the impact of escalating threats.
II. AI & Threat Intelligence & Big Data
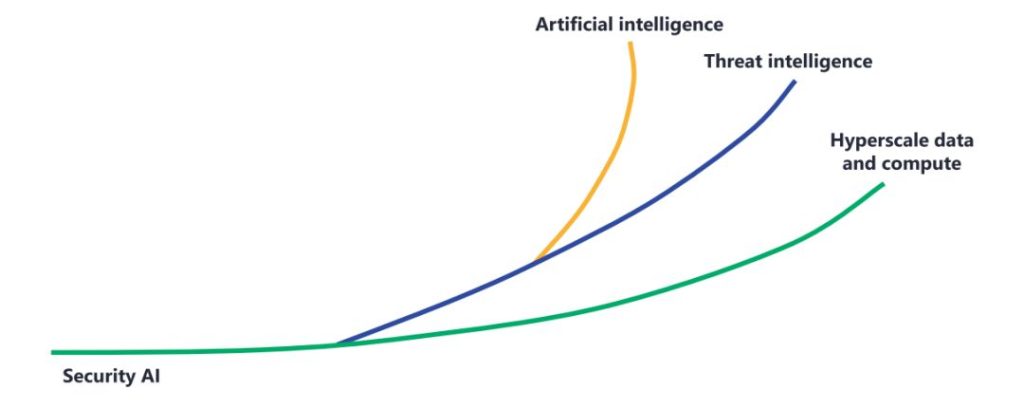
In the field of network security, emerging technologies such as artificial intelligence (AI), threat intelligence, and big data computing have transformed and strengthened network security defense. These three technologies are not independent of each other; instead, they synergistically combine their forces. Technological innovation or optimization in one area promotes continuous progress in the other two, and together, they complement each other, acting as driving forces for each other.
The reduction in the costs of big data storage and computing has made massive data collection more feasible. The information obtained from probes and various detection and protection devices serves as valuable intelligence data for threat intelligence. This, in turn, promotes the improvement of threat intelligence in detection defense and the convergence of attack surfaces.
With the continuous improvement in the quality and quantity of intelligence data, threat intelligence-driven threat detection can uncover a greater number of threat signals. These threat signals can also serve as training resources for large-scale language data models, enhancing the capabilities of artificial intelligence and machine learning. As a result, these technologies can be more effectively utilized in security detection and protection. This convergence enables threat intelligence to uncover threat clues while artificial intelligence expands the scope of security defense, combining the strengths of both domains (threat intelligence for identification and artificial intelligence for scalability).
III. Named Threats
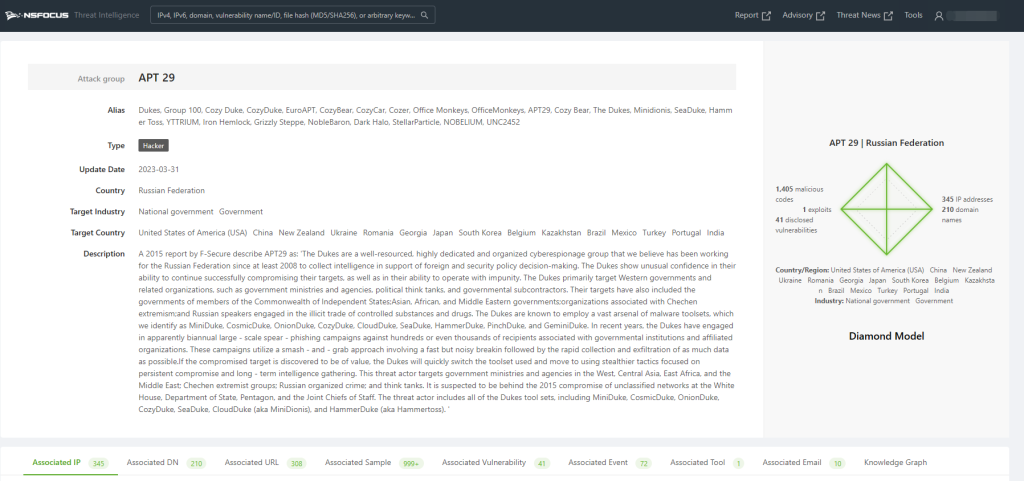
There are often multiple names for the same attacking organization, such as APT28, which is also referred to as Fancy Bear or Sednit. These names are assigned by different institutions or organizations, but they can be too abstract for users. Consequently, users may struggle to intuitively understand the characteristics of these organizations, and the naming conventions lack memorable points.
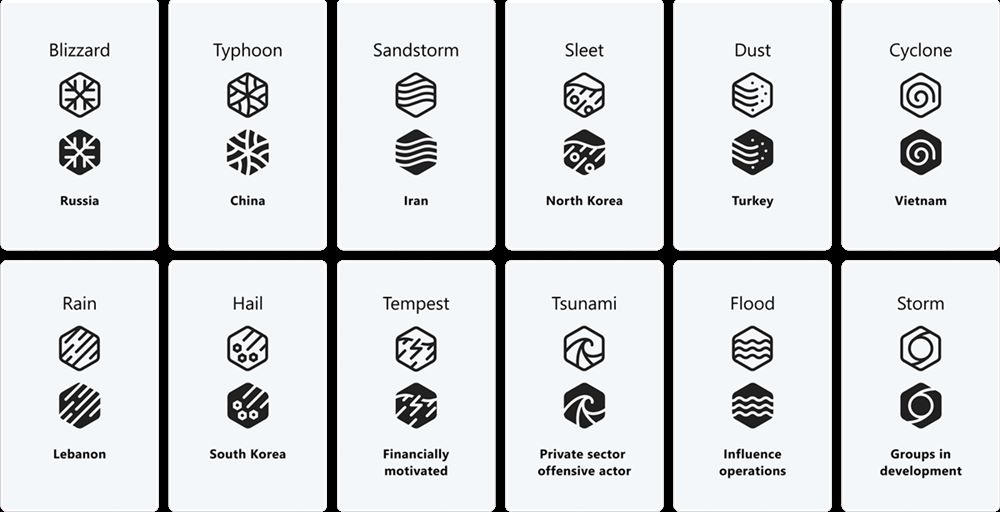
To solve this problem, Microsoft utilizes various weather events to redefine and name threat groups. With the new taxonomy, users and security researchers can more clearly process large amounts of threat intelligence data, refer to and describe threat actors in a more organized, clearer, and simpler way, and help users better identify, prioritize, and quickly take security measures.
Microsoft divides threat groups into five categories:
1. State Actors
An attack group directed on behalf of a state or by a state-affiliated group whose attacks are often motivated by espionage, financial gain, or retaliation for an attack. Its actions and attacks are mostly focused on government agencies, international organizations, and non-governmental organizations.
2. . Financially Motivated Participants
An attack group directed by a criminal organization/individual motivated by financial gain and without strong evidence of ties to a non-state entity or economic group. Such attack groups use methods including ransomware, phishing, business email theft, etc.
3. Private Sector Offensive Actors (PSOA)
Attack groups led by known/legitimate commercial actors who create and sell cyberattack weapons to users who then select targets and operate the cyberattack weapons to complete the attack.
4. Manipulator of Influence
A group that disseminates information online or offline in a manipulative manner to change the perceptions, behavior or decisions of a target audience to achieve specific interests and goals.
5.Emerging Organization
Temporary designation for an unknown, newly discovered, or developing attack group. When enough attack behavior characteristics are obtained, it will be merged into the existing organization name or given a new organization name.
In Microsoft’s new classification, meteorological events will be used as the last name for the attacking organization to name the five types of attacking organizations mentioned above. In the case of state actors, the surname will indicate the country affiliation of the attacking group. For example, the attack group APT35 from Iran, under the new naming method, is named Mint Sandstorm. For the other four categories of attacking groups, the last name indicates the motive. For example, Tempest refers to financially motivated participants. Attacking groups within the same weather series can use adjectives to distinguish organizational characteristics with different tactics, techniques, and procedures (TTPs), infrastructure, goals, or other identified patterns.
IV. Cobalt Strike attack and defense
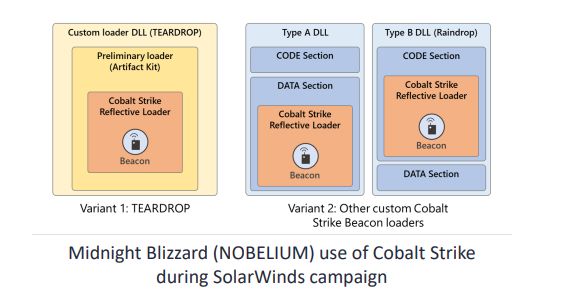
Cobalt Strike is a globally oriented commercial penetration software written in Java with a client/server (C/S) architecture. It is suitable for multi-person teamwork and can simulate APT (Advanced Persistent Threat) for simulated confrontations and intranet penetration. It serves as an opponent simulation and red teaming platform designed to perform targeted attacks and simulate post-exploitation actions of advanced threat actors. In recent years, it has gained popularity among attackers due to its various functions and scalability. According to Health-ISAC statistics, Cobalt Strike was used in more than 68 ransomware attacks against medical institutions in 19 countries worldwide. Additionally, in the SolarWinds supply chain attack incident, Midnight Blizzard (also known as NOBELIUM or APT29) utilized Cobalt Strike for the attack.
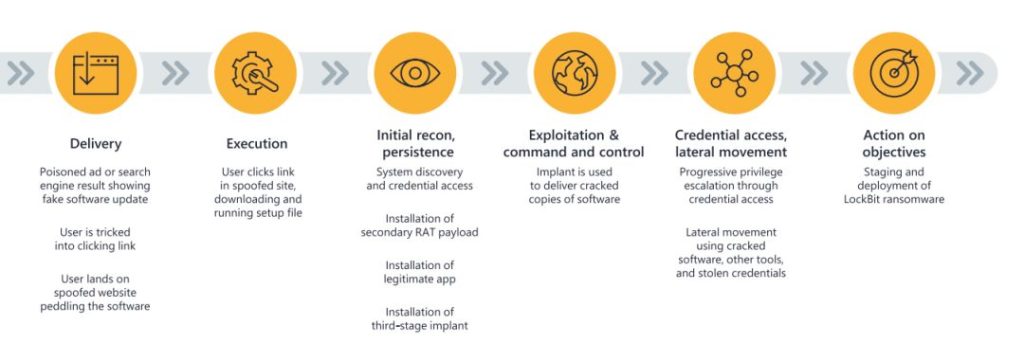
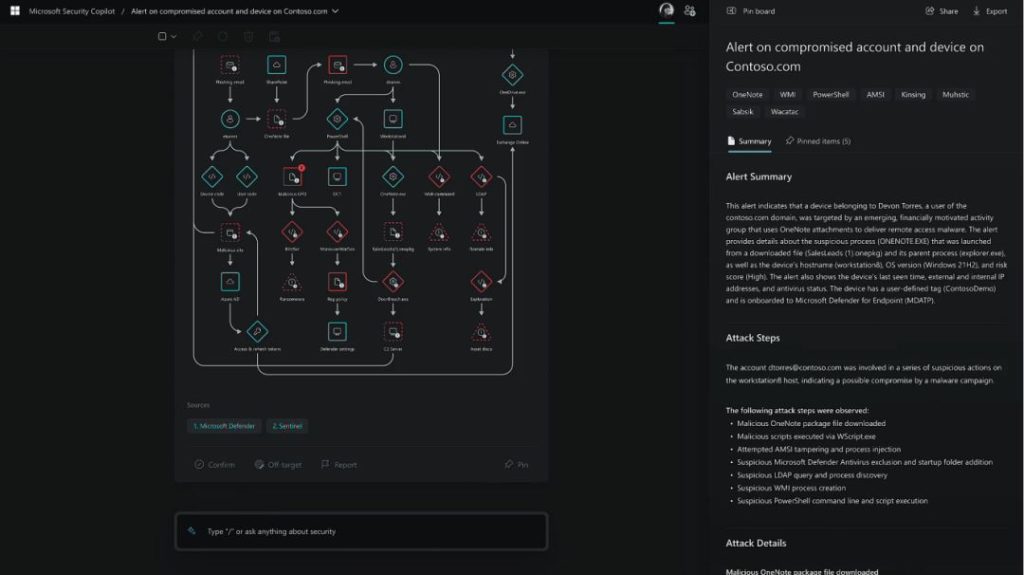
The figure below describes how the attackers induce victims to download malware step by step, install malware, steal credentials, and finally complete a ransomware attack based on Cobalt Strike.
V. How AI Empowers Security
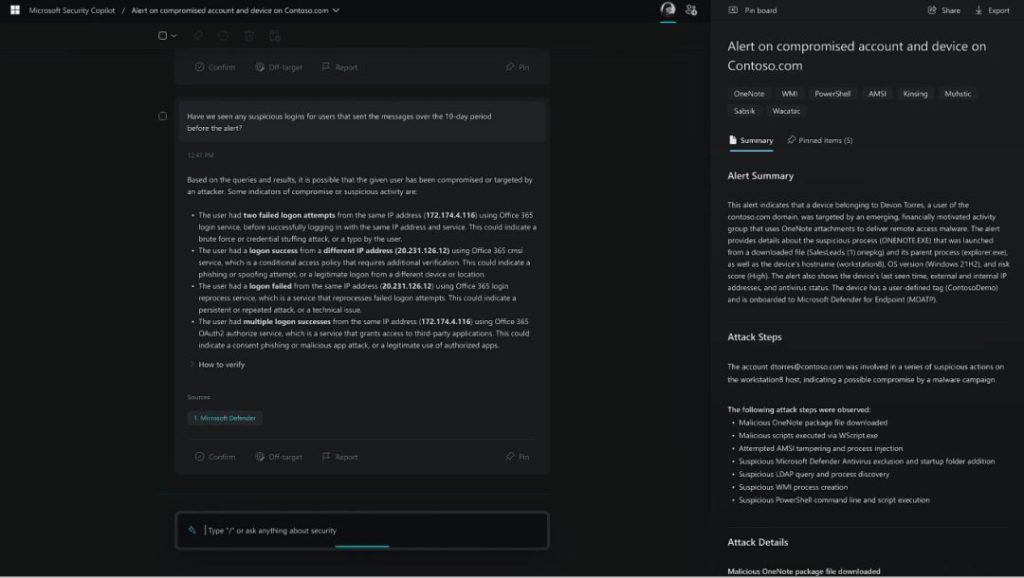
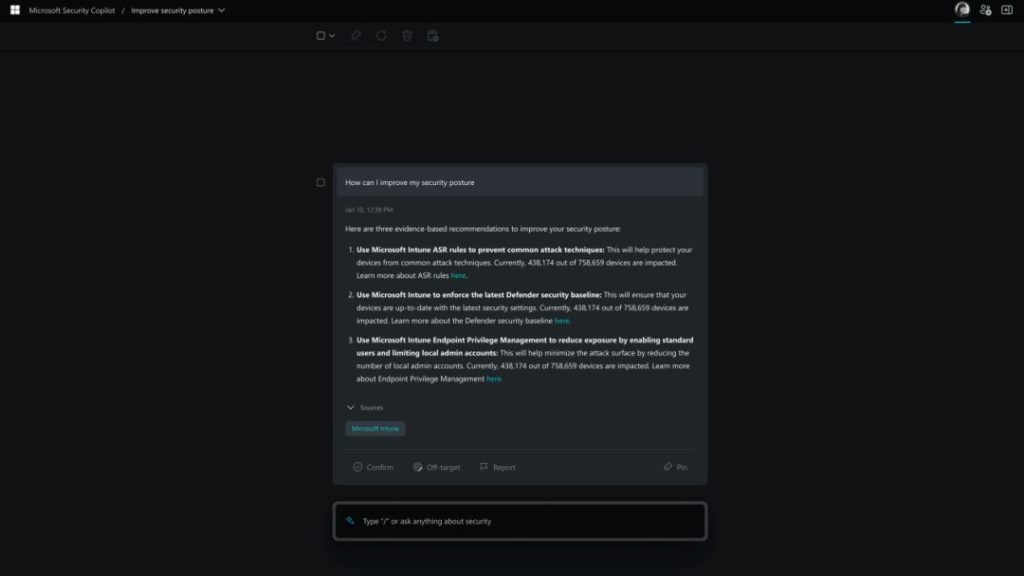
At the end of 2022, the release of ChatGPT set off a new wave of artificial intelligence and large language model applications. AI also has broad application prospects in the field of network security. In this sharing, John introduced the application of AI in network security, including:
- Natural language interaction
- Simplifies learning and writing custom query syntax
- Expand knowledge and technology
- Assist in finding security issues
- Create a security plan
By applying the large language model represented by ChatGPT, we can easily realize natural language interaction or ask it to convert text requirements into custom query syntax. In terms of code and problem detection, it can also help relevant practitioners quickly complete troubleshooting.
In addition, since a large amount of security knowledge has been obtained during its model training, as a library of network security knowledge, it can also assist users in obtaining or supplementing relevant knowledge, assist in establishing security protection plans, and improve security protection capabilities.
Reference
[1] https://aka.ms/threatactors
[2] https://blog.csdn.net/LUOBIKUN/article/details/108707160