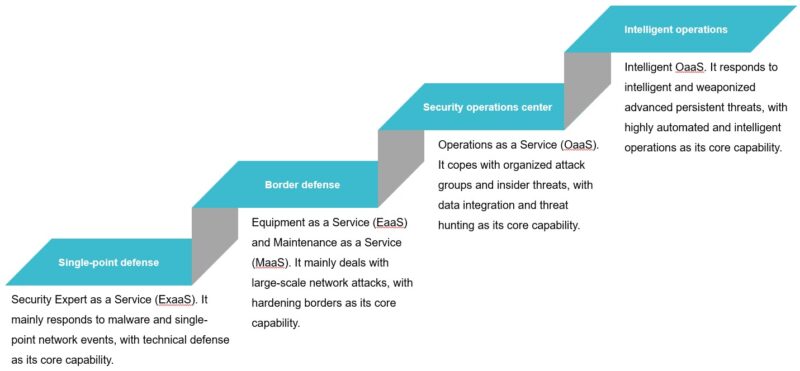
AISecOps Development Trend
As an old saying goes, “Rome was not built in a day”, it is impossible to build AISecOps capabilities simply by following the example of other businesses. In fact, the most topical and mature AI technology is widely applied, but needs to be delved a little deeper. For instance, typical intelligence services like intelligence speech […]